计费概述
Download
聚焦模式
字号
版本说明
腾讯云安全中心为用户提供三个付费版本,分别是高级版、企业版和旗舰版。每个版本按照功能和默认规格划分,以适应不同规模和需求的客户。计费详情如下:
计费相关 | 高级版 | 企业版 | 旗舰版 | 弹性拓展 | |
基础价格 | | 375美元/月 | 1,000美元/月 | 2,667美元/月 | - |
可购买时长 | | 3个月、6个月、1年、2年、3年 | 1个月、3个月、6个月、1年、2年、3年 | | - |
资产与风险管理 | 资产管理 | 支持 | 支持 | 支持 | - |
| 资产体检 | 400次/月 | 1,200次/月 | 4,800次/月 | 0.83美元/次/月,扩展步长300次 |
| 扫描任务管理 | 1 | 10 | 20 | 50,可扩展至不限制 |
| 端口扫描 | 支持 | 支持 | 支持 | - |
| 应急漏洞扫描 | 支持 | 支持 | 支持 | - |
| 深度漏洞扫描 | 支持 | 支持 | 支持 | - |
| 弱口令扫描 | 支持 | 支持 | 支持 | - |
| 云资源配置检查 | 支持 | 支持 | 支持 | - |
| 内容扫描(网站内容风险) | - | 支持 | 支持 | - |
攻击与告警处置 | 日志分析量 | 1,000GB/月 | 3,000GB/月 | 10,000GB/月 | 0.104美元/GB/月,扩展步长1,000GB |
| 告警接入 | 支持 | 支持 | 支持 | - |
| 用户行为分析 | - | - | 支持 | - |
| 告警聚合、事件调查与关联分析 | 支持 | 支持 | 支持 | - |
| 联动处置 | - | 支持 | 支持 | - |
| AI 自动处置 | - | - | 支持 | - |
安全管理 | 安全报告 | 体检报告 | 巡检解读报告 | 安全专家洞察报告 | - |
| 日志投递 (投递 Ckafka) | - | - | 支持 | - |
| 日志接入 | 支持 | 支持 | 支持 | - |
| 多账号管理 | - | - | 可扩展 | 625美元/账号/月,超过10个不额外收费,若成员账号已购买旗舰版,则多账号功能免费 |
选型指引
云安全中心是一站式的云上安全管理平台,根据不同用户的需求场景提供高级版、企业版和旗舰版三种套餐,建议您从云上资产数、集团账号、日志审计、重要时期安全保障四个角度选择最适合您需求场景的套餐:
功能类型 | 高级版 | 企业版 | 旗舰版 |
云上资产数,例如:公网 IP、域名、主机、负载均衡、数据库、对象存储 COS、Elasticsearch Service 等资产的数量 | 100 | 300 | 900及以上 |
集团账号,是否使用腾讯云集团账号解决方案 | 否 | 否 | 是 |
日志审计,是否需要统一接入安全产品日志进行分析管理 | 否 | 是 | 是 |
重要时期安全保障,是否需要进行互联网攻防演练 | 否 | 是 | 是 |
资产体检说明
云安全中心支持对资产进行安全体检,涵盖端口、弱口令、应急漏洞、深度漏洞、服务暴露、网站内容风险、云资源配置等方面。
每次体检会消耗资产体检次数,即1次扫描1个资产(例如:公网 IP、域名、主机、负载均衡、数据库、对象存储 COS、ElasticsearchService 等)消耗1资产/次,云安全中心高级版、企业版、旗舰版分别包含400、1200、4800个资产体检数,支持付费扩展。
为降低资产安全风险,建议每月进行4次自动检测和1次手动全面检测,请根据您的云上资产数量计算购买的资产体检数。
增值服务计费说明
云 API 异常监测
计费策略:(基础服务计费 + AK 资产数计费*当前 APPID 下全部 AK 资产数)*服务时长
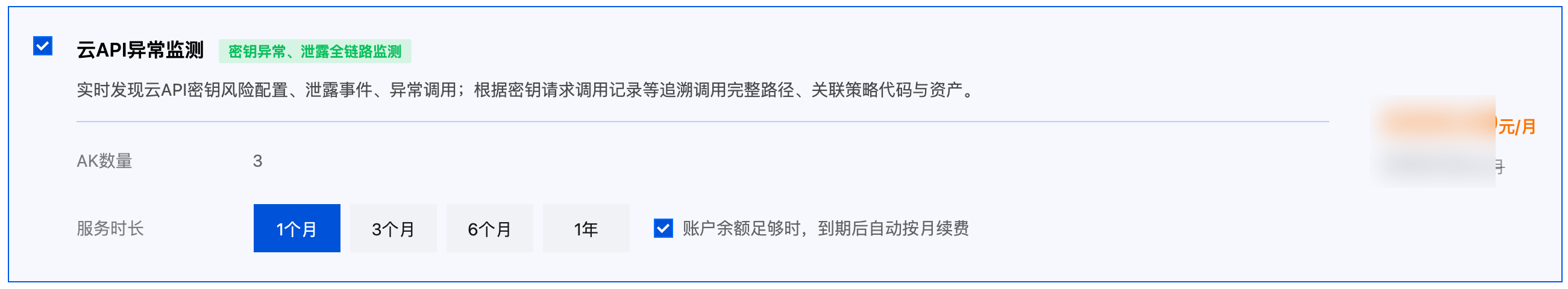
基础服务计费 | AK 资产数计费 |
857美元/月 | 14美元/个/月 |
计费示例:
账号 A 下有4个 AK,购买云 API 异常监测服务2个月,所付金额为(857 + 14*4)*2 = 1,826 (美元)。
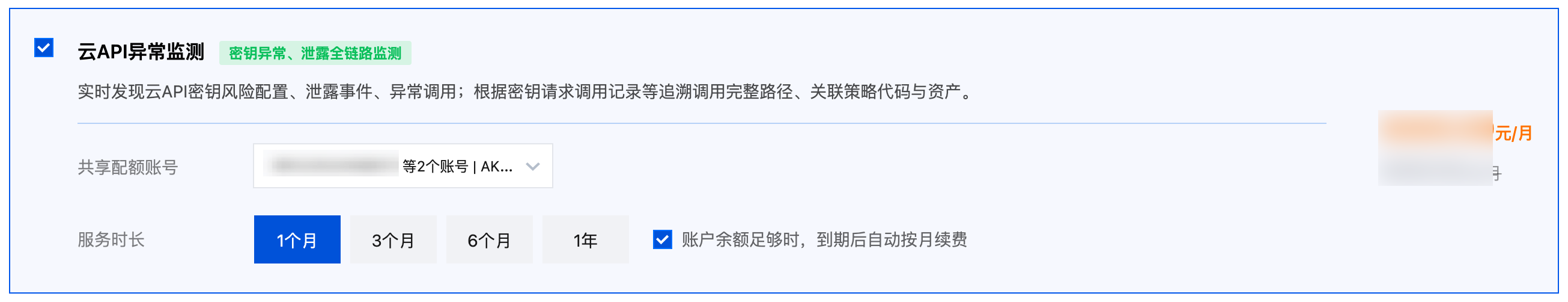
多账号场景说明
多账号管理员可为其成员账号统一购买服务,选择多成员时只需支付一次基础服务费用,AK 资产数费用按选择的多成员账号 AK 资产总数计算,付费的 AK 资产数作为配额在账号共享。
其他情况说明如下:
场景 | 订单归属 | 服务可用性 | 配额共享 | 购买限制 |
多账号管理员为其成员账号统一购买服务 | 管理员账号 | 管理员与成员默认均可用该服务 | 管理员与成员账号间配额共享 | 成员账号不可再单独购买该服务 |
成员账号单独购买服务 管理员账号单独购买服务 | 分别归属于成员账号、管理员账号 | 成员默认可用该服务,管理员可见成员数据 | 单独购买的成员账号与管理员统一购买的账号间配额不共享 | 管理员不可再为该成员统一购买服务,不可管理该成员订单 |
示例
1. 计费示例:
账号 A下有2个成员账号 B 和 C。A、B、C 账号下 AK 资产数分别为2、5、3,A 统一为 B、C 购买云 API 异常监测服务2个月,所付金额为(857 + 14*10)*2 = 1,994(美元)
2. 配额共享示例:
账号 A 下有2个成员账号 B 和 C。A、B、C 账号下 AK 资产数分别为2、5、3。
A 统一为 B、C 购买云 API 异常监测服务,付费资产数为10(配额为10),配额共享。若 A 的 AK 资产数由2变为0,B 的资产数由5变为7,三个账号总配额数仍为10,不需要进行扩容。
A 统一为 B 购买云 API 异常监测服务,付费资产数为7(配额为7);C单独购买服务,付费资产数为3(配额为3)。A 与 B 间配额共享,与 C 间配额不共享。若 A 的 AK 资产数由2变为0,C 的资产数由3变为5,A 不需要进行扩容;C资产数超出配额2,需变配扩容。
文档反馈