鉴权粒度方案
最后更新时间:2023-12-27 10:01:18
资源六段式说明
qcs:是 qcloud service 的简称,表示是腾讯云的云资源。该字段是必填项。
project_id:描述项目信息,兼容 CAM 早期逻辑,无需填写。
service_type:产品简称,如 CVM。
region:地域信息,如 bj(参考 CAM 文档,如有不同,请给出地域列表的简称)。
account:资源拥有者的主账号信息,如 uin/164256472。
resource:各产品的具体资源详情,如 instance/instance_id1或者 instance/*。
标签鉴权操作指引
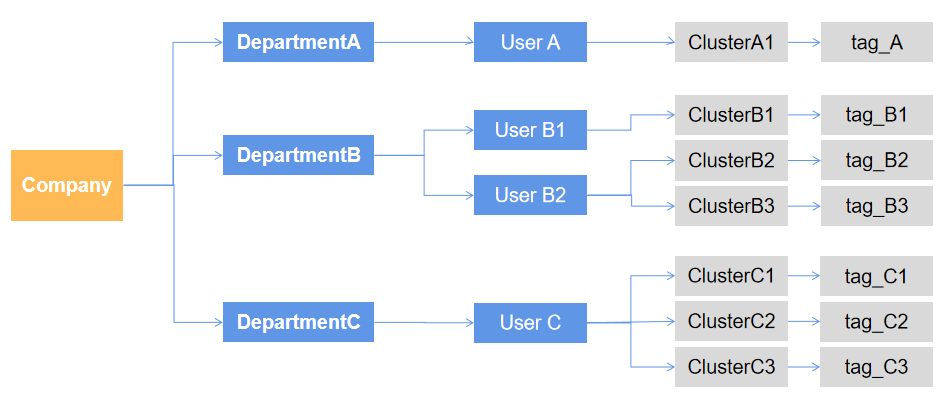
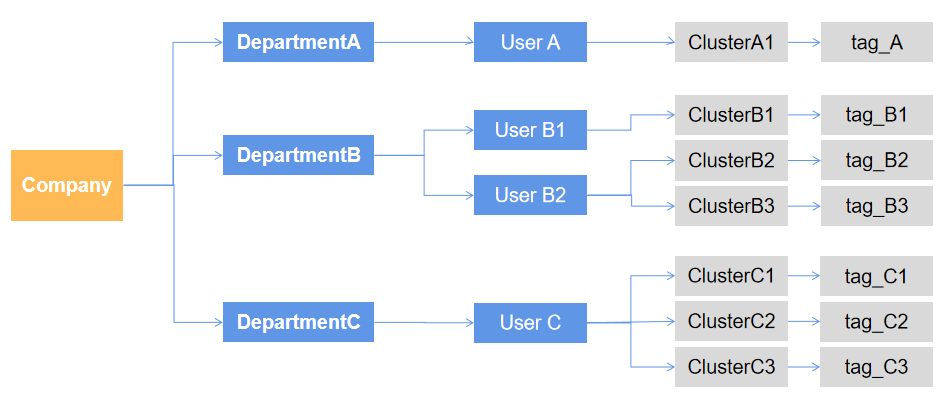
下文将为您介绍 EMR 标签鉴权的操作流程,使用标签对 EMR 上的资源进行鉴权管理前,您需要先对公司的部门或组织做好标签规划;例如下图,分别对部门 A/B/C 规划好对应的用户名、集群、标签等。标签相关操作请参考:标签 。
规划完成后,要实现部门 A 来管理集群 A1,需要按顺序完成如下操作。
1. 新建标签并为集群打上标签
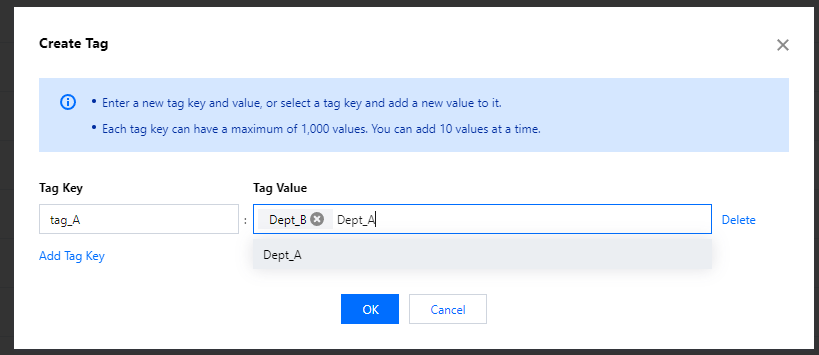
进入 标签列表页面,单击新建标签。
说明
此处及后续流程标签 tag_A 举例。
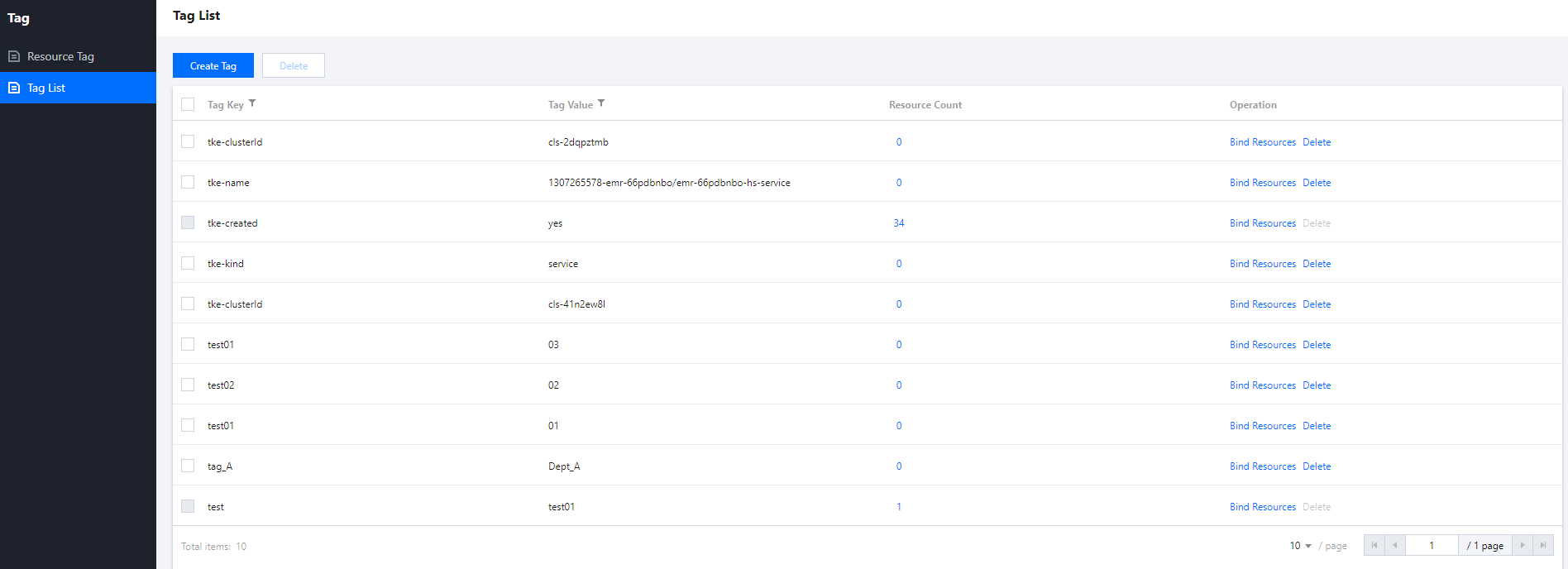
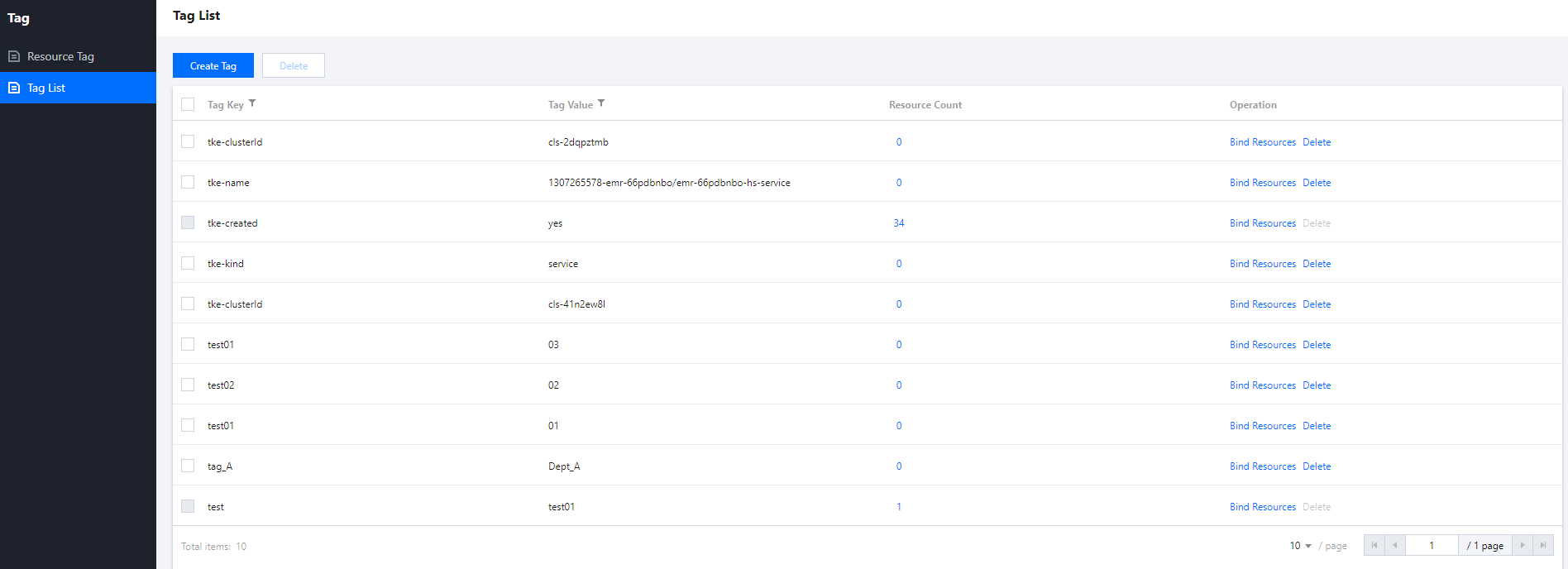
输入标签键和标签值,单击确定即可创建成功。
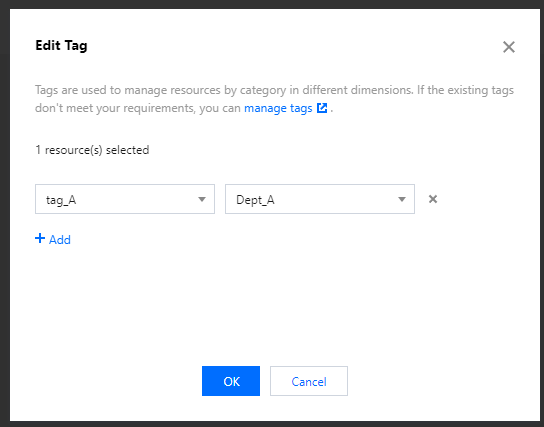
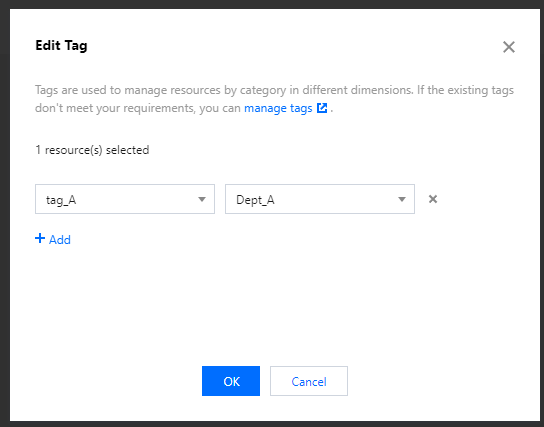
在 集群列表 页面选择要打标签的集群,单击上方更多操作,单击编辑标签。
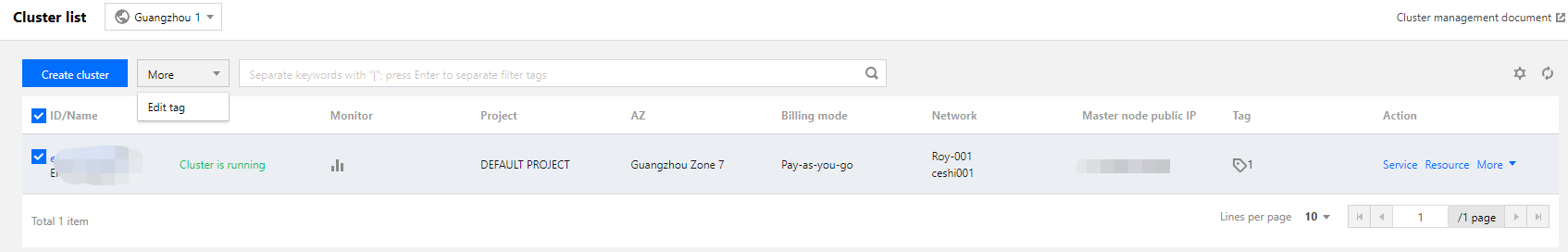
编辑标签中选择之前建立的 tag_A,单击完成即可。
2. 新建自定义策略
目前 EMR 部分接口不支持标签鉴权,所以目前需要设置两个策略,Policy_Dept_A1是标签策略,Policy_Dept_A2是不支持标签的接口策略。
新建自定义策略Policy_Dept_A1
进入 访问管理策略 页面,单击新建自定义策略。
选择按标签授权。
标签策略生成器,赋予用户选择 Dept_A,用户组不填,标签键和标签值选择规划好的对应标签,根据需求添加服务与操作,单击下一步即可。
新建 Policy_Dept_A1策略,在策略内容中将“action”和“resource”字段,改为如下内容,单击完成即可。
{"effect": "allow","action": ["emr:DescribeClusterNodes","emr:DescribeInstancesList"],"resource": ["*"],"condition": {"for_any_value:string_equal": {"qcs:resource_tag": ["tag_A&Dept_A","tag_B&Dept_B","tag_C&Dept_C","tag_D&Dept_D"]}}}
注意
新建自定义策略 olicy_Dept_A2
进入访问管理策略页面,单击新建自定义策略。
选择按策略语法创建。
选择策略模板时,选择空白模板,单击下一步。
新建 Policy_Dept_A2策略,将策略内容中原有内容清除后,粘贴如下内容,单击完成即可。
{"version": "2.0","statement": [{"effect": "allow","action": ["emr:RunJobFlow","emr:DescribeJobFlow","emr:FindClusterListForMC","emr:EmrScaleoutClusterWithAuth","emr:CreateClusterForMC","emr:CheckSoftRelation","emr:DescribeK8sResourcePrice","emr:DescribePodSpecs","emr:DescribePodSpec","emr:DescribeTkeWhiteList","emr:GenerateCreateGoodsDetail","emr:DescribeLogSearchFileNames","emr:DescribeEMRInstancesExtra","emr:DescribeClusterHardwareInfo","emr:DescribeInstanceServiceRoleNames","emr:DescribeServiceComponents","emr:DescribeCompareMetricsList","emr:DescribeHeatMapMetricList","emr:DescribeHBaseRegionList","emr:DescribeAutoScaleWhiteList","emr:DescribeOptionalSpecWhiteList","emr:DescribeServiceOverview","emr:DescribeEMRInstances","emr:DescribeEMRNodeType","emr:DescribeEMRNodes","emr:DescribeStepByTimeRange","emr:DescribeClusterOverview","emr:DescribeEMRNodeOverview","emr:DescribeNodeHardwareInfo","emr:DescribeTopNMeta","emr:DescribeMetricDataAutoGranularity","emr:DescribeLogSearchTabs","emr:DescribeEMRHostOverview","emr:DescribeLogSearchRecords","emr:DescribeTopNByProcess","emr:DescribeDiskInfo","emr:DescribeMetricInfo","emr:DescribeInstanceServiceAbstract","emr:ModifyMetricMetaPerInstance","emr:DescribeOverviewData","emr:DescribeClusterHardwareType","emr:DescribeClusterEmergencyCallback","emr:DescribeTopNByHost","emr:DescribeHeatMapDistribution","emr:DescribeInstanceServiceRoleTable","emr:DescribeEmrSaleInfoExtend","emr:DescribeNodeAlias","emr:DescribeInstanceNodes","emr:DescribeKeyPairs","emr:DescribeHbaseTableMetricData","emr:DescribeHbaseMetricMeta","emr:DescribeEmrMetaDB","emr:CheckMetaDBNet","emr:ModifyEmrRole","emr:DescribeEmrRole","emr:DescribeDisasterRecoverGroup","emr:DescribeTags","emr:InquiryPriceCreateInstance","emr:GetCreateGoodsDetail","emr:DescribleAccountBalance","emr:DescribeSecurityGroup","emr:DescribeMetricData","emr:DescribeEmrSaleInfo","emr:DescribeCvmSpec","emr:DescribeCdbPrice","emr:CreateInstance","emr:CheckCustomConfig","emr:CheckCosInfo","emr:GetCreateGoodsDetailList","emr:GetScaleoutGoodsDetailList","emr:GetRenewGoodsDetailList","emr:UpdateWebProxyPassForMcController","emr:SubmitServiceParamsForMC","emr:ReleaseClusterForMC","emr:RestartServiceForMC","emr:GetNodeListForMcController","emr:GetMetricDataForMcController","emr:GetServiceGroupForMcController","emr:EmrDestroyTaskNodeWithAuth","emr:DescribeModifySpec","emr:DescribeMasterIp","emr:DescribeMetricsDimension"],"resource": "*"}]}
3. 子用户赋权并验证
在用户列表页面找到要赋权的子用户,单击右侧的授权按钮;新建子用户请参考:新建子用户。
选择 Policy_Dept_A1和 Policy_Dept_A2,单击完成即可。
以子用户身份登录进行验证。
此时登录 EMR,子用户仅能通过标签 tag_A 看见和管理 test_A 集群。
资源级和接口级鉴权操作指引
下文将为您介绍 EMR 资源级鉴权的操作流程,使用资源级鉴权对 EMR 具体某功能鉴权时,您需要先对公司的部门或组织做好规划;例如,分别对部门 A/B/C 规划好对应的用户名、接口、集群等。
规划完成后,要实现部门 A 仅支持对集群的 DescribeRegionAndZoneSaleInfo 接口有访问权限,需要按顺序完成如下操作:
1. 新建自定义策略
进入 访问管理策略 页面,单击新建自定义策略。
选择按策略语法创建。
选择策略模板时,选择空白模板,单击下一步。
新建名为 DescribeRegionAndZoneSaleInfo-test 自定义策略,将策略内容中原有内容清除后,在策略里面配置 EMR 中 DescribeRegionAndZoneSaleInfo 接口的访问权限 deny 策略,创建好之后保存即可。
{"version": "2.0","statement": [{"effect": "allow","action": ["emr:DescribeRegionAndZoneSaleInfo"],"resource": "*"}]}
注意
支持资源级鉴权接口可参考支持资源级鉴权的 API 列表,因接口暂时只能采用列表的形式全量罗列,不排除后续接口新增时出现操作报错,如遇到权限报错情况,可根据报错提示缺少对应接口权限进行策略中补充。
2. 子账号赋权并验证
在用户列表页面找到要赋权的子用户,单击右侧的授权按钮;新建子用户详细操作请参见 新建子用户。
选择 DescribeRegionAndZoneSaleInfo-test 自定义策略名称,单击完成即可。
子账号登录后,调用上述接口出现类似下面需要授权的弹窗,说明鉴权成功。
文档反馈

