Overview
Feature Overview
The NAT Firewall (Cluster Mode) is a new protection capability added by CFW for the "centralized egress" network architecture. When a user deploys a NAT Gateway as the public network egress in one VPC and other service VPCs route traffic to this NAT Gateway via CCN to access the public network, the Cluster Mode can perform unified security inspection and Access Control on this cross-VPC north-south traffic. This helps users defend against attacks and malicious access from the internet while restricting unauthorized outbound connections from cloud assets.
Notes:
If you only need to protect traffic that passes through the NAT Gateway within the same VPC, you can use the NAT Firewall's NAT Firewall Toggle (Primary/Secondary mode). Both modes can be enabled simultaneously without conflict.
Scenario
This document describes how to enable and configure the NAT Firewall (Cluster Mode). If your cloud network architecture matches the following scenarios, we recommend using this feature:
Centralized Egress Architecture: A NAT Gateway is deployed in one VPC as the public network egress, and other service VPCs are routed to this NAT Gateway via CCN to access the public network.
Cross-VPC North-South Traffic Protection: Unified security inspection and Access Control are required for inbound and outbound traffic from multiple service VPCs that passes through the NAT Gateway.
Prerequisite
You have purchased a CFW instance (all editions are available).
You have created a CCN instance and associated the service VPCs that require protection and the VPC where the NAT Gateway resides with this CCN.
To use the automatic access mode, you need to submit a ticket to CCN to apply for it.
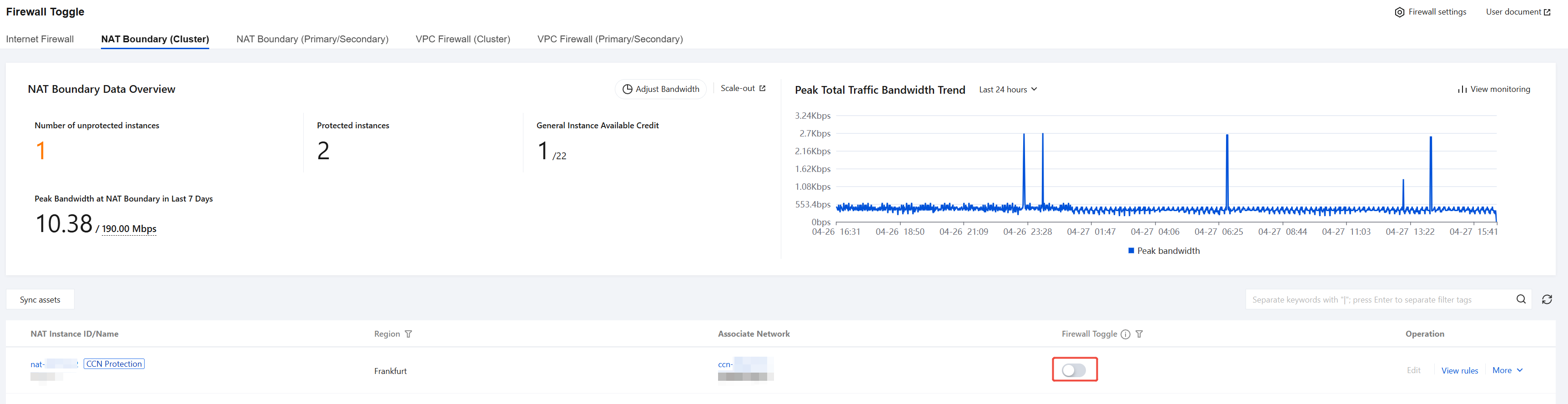
Firewall Toggle
Step 1: Enabling the NAT Firewall (Cluster Mode)
1. Log in to the CFW console, and click Firewall Toggle in the left sidebar.
2. On the Firewall Toggle page, select the NAT Boundary (Cluster) tab.
3. In the NAT Gateway list, locate the instance that requires protection, and click the toggle button in the Firewall Toggle column.
Note:
Enabling protection consumes one general instance quota. If the remaining general instance quota is insufficient, the toggle will be grayed out and display the message "Insufficient general instance quota. Please retry after scaling up." To scale up, go to the purchase page to increase your general instance quota.
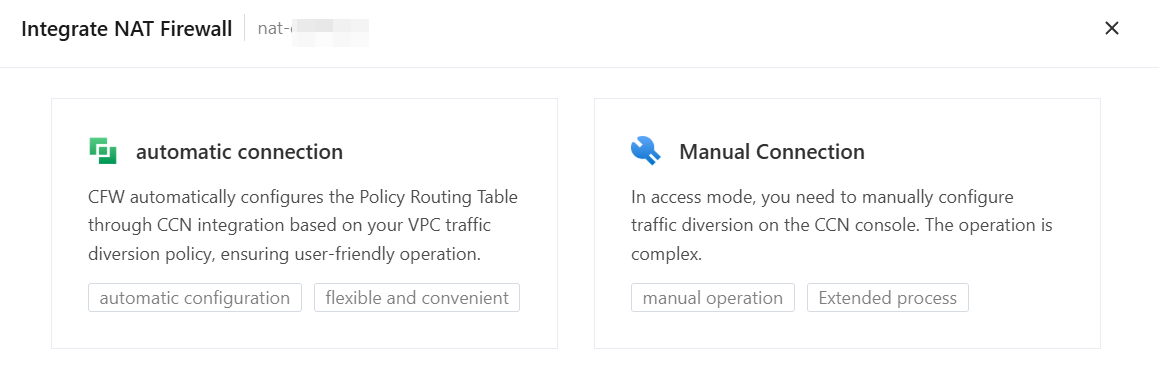
4. In the configuration drawer that pops up, select an access mode, and then complete the subsequent configuration based on the selected mode.
Step 2: Configuring Traffic Diversion
Automatic Connection Mode
After selecting the automatic connection mode, you need to configure the traffic diversion policy and traffic diversion VPC:
1. In the traffic diversion policy configuration area, select the service VPCs that require protection from the dropdown list.
Notes:
The VPC list automatically pulls all VPCs associated with the current CCN (including cross-account VPCs). The VPC where the NAT Gateway resides is not included in the list (protection for the same VPC is managed by a separate same-VPC row in the list).
2. In the input box on the right, enter the corresponding CIDR (for example,
10.0.0.0/16), and then click Next.To add multiple traffic diversion policies, click the Add One button to add them one by one. Each traffic diversion policy is a combination of a VPC + CIDR.
The CIDR must comply with the standard format, for example,
10.0.0.0/16 or 0.0.0.0/0.Notes:
After you enable protection, if the CCN adds associated VPCs or the selected VPCs add CIDR blocks, the new VPCs/blocks are not automatically protected. If there are any additions, use the Edit feature to reconfirm the traffic diversion policy.
If a traffic diversion policy for intra-region VPCs exists, you need to submit a ticket to the CCN to apply for enabling the intra-city traffic diversion feature for VPC instances.
3. Configure the creation method for traffic diversion VPCs by region:
Auto: The system automatically probes for an available /26 subnet (that is, a subnet containing 64 IP addresses) and creates a traffic diversion VPC.
Custom: Specify a /26 CIDR block. The system creates a traffic diversion VPC based on the specified CIDR.
4. Click Access Now and wait for the access process to complete.
Manual Connection Mode
After you select the Manual Connection mode, the configuration drawer adopts a step-by-step process:
1. For manual access, select multi-route table.
2. Configure the creation method for traffic diversion VPCs by region:
Auto: The system automatically probes for an available /26 subnet and creates a traffic diversion VPC.
Custom: Specify a /26 CIDR block. The system creates a traffic diversion VPC based on the specified CIDR.
3. Select the confirmation item: Acknowledge that traffic access to CFW requires manual configuration after enabling the firewall switch.
4. Click Create and wait for the traffic diversion VPC to be created (estimated time: 30 seconds).
5. In manual access mode, traffic is not automatically protected after you enable the Firewall Toggle. You must go to the CCN console to configure route traffic diversion to the CFW for protection to take effect. For detailed steps, see Manual Access Routing Configuration Guide.
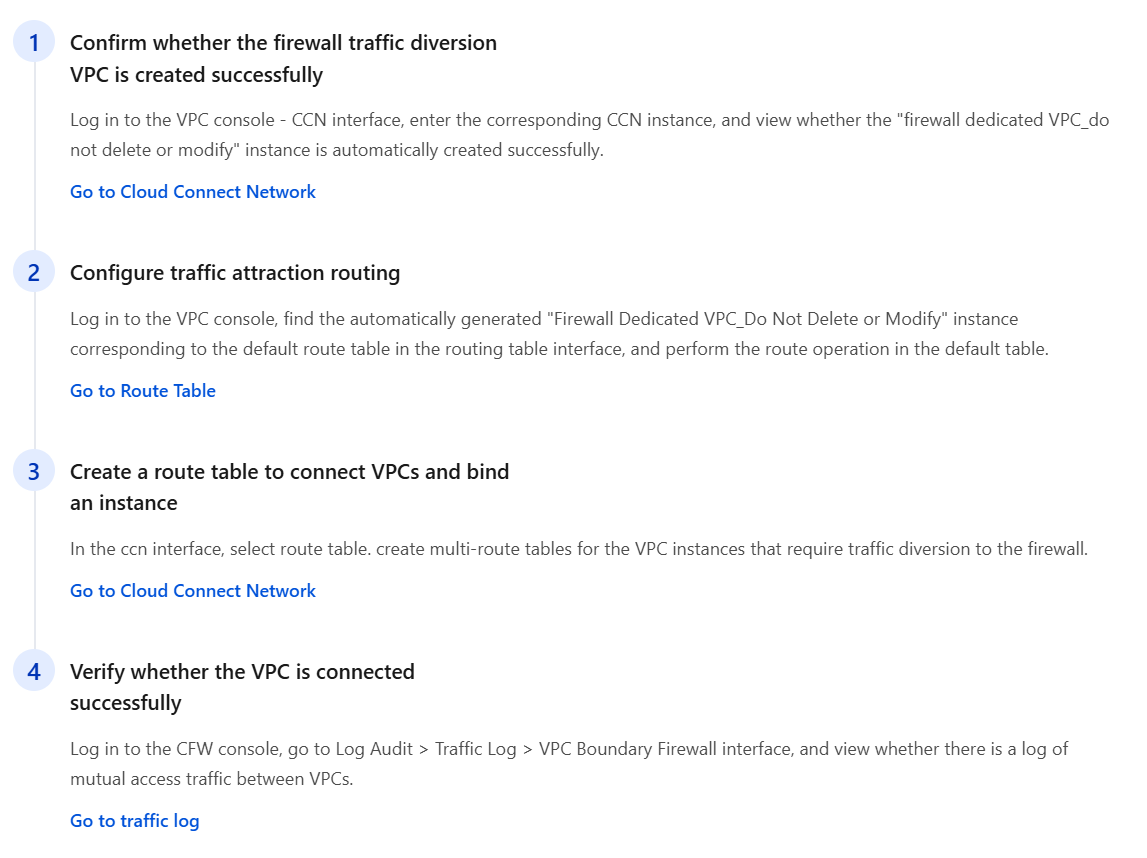
Step 3: Verifying the Protection Status
1. After successful enabling, the Firewall Toggle column for CCN protection will be displayed as Enabled.
2. For the automatic access mode, click the expand button at the beginning of the row to view traffic diversion policy details (traffic diversion VPC, region, traffic diversion CIDR).
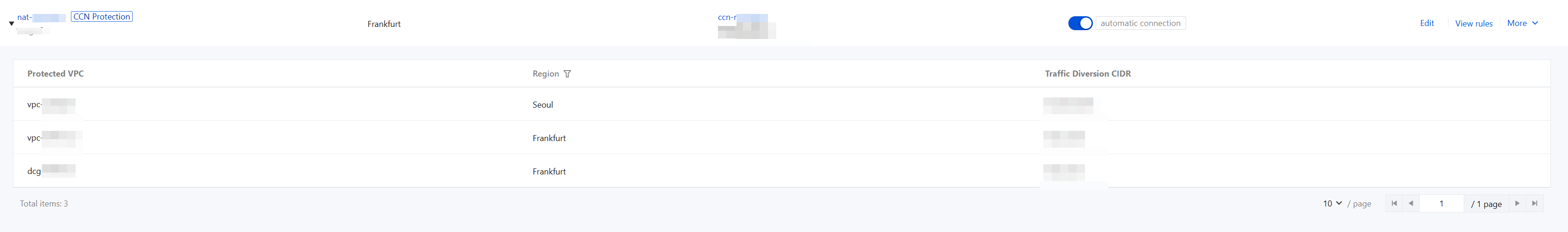
3. The firewall begins security inspection and Access Control on cross-VPC north-south traffic within the CCN associated with this NAT Gateway.
Editing the Traffic Diversion Configuration
On the NAT Boundary (Cluster) page, click Edit to adjust the traffic diversion configuration for instances with protection enabled.
Access Mode | Editable Content | Description |
Automatic Access | Traffic Diversion Policy Configuration + Traffic Diversion Network Configuration | Add/delete traffic redirection VPCs, modify CIDRs, and adjust traffic diversion networks |
Manual Access - Multiple Routing Tables | Traffic Diversion Network Configuration | Adjust the creation method and configuration of the traffic diversion VPC. |
Notes:
The access mode cannot be edited after protection is enabled. To change the access mode, you must first disable the Firewall Toggle and then re-enable it.
Editing is allowed in Bypass state. After you modify and save, the configuration is updated. The new configuration takes effect on traffic after Bypass is disabled.
Bypass Feature
The Bypass feature allows users to temporarily bypass the firewall while retaining traffic diversion resources, for scenarios such as troubleshooting or temporary traffic allowance.
1. On the NAT Boundary (Cluster) page, locate the protection instance for which you need to enable the Bypass feature.
2. In the Operation column, choose More > Enable Bypass.
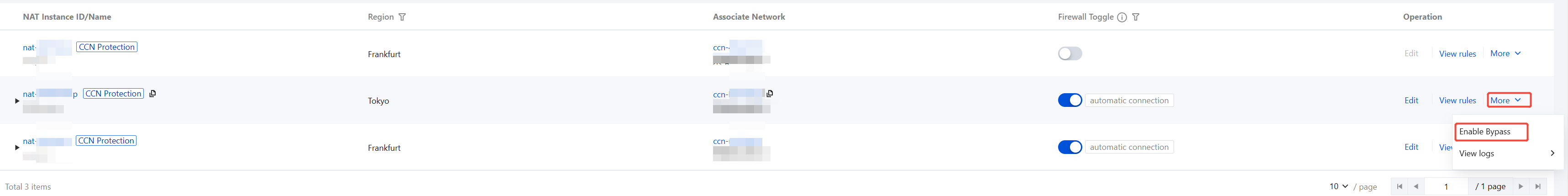
3. In the confirmation pop-up window, confirm to enable.
After enabling, a
Bypass Tag will be displayed after the switch in the Firewall Toggle column, indicating the current Bypass state. In Bypass state, no traffic fees are incurred, but the general instance is still occupied.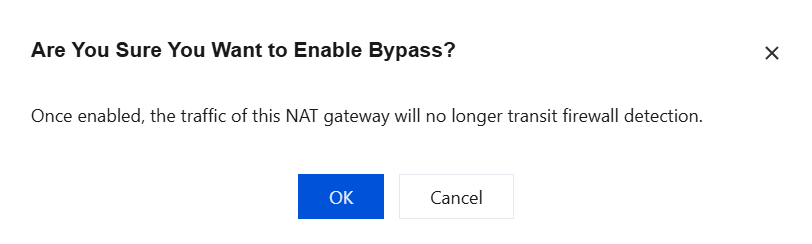
Note:
After Bypass is enabled, traffic from this NAT Gateway will no longer undergo firewall inspection and will not be constrained by Access Control rules or Intrusion Defense policies. It is recommended to enable it only temporarily for troubleshooting.
Disabling Protection
Note:
When the access mode of the current protection object is Manual Access, you must cancel the access of this CCN instance in the CFW console before disabling the Firewall Toggle. Otherwise, directly disabling the toggle may cause network interruption. For detailed steps, see Disconnecting a NAT Gateway from CFW (Multi-Route Table).
1. Click the toggle button in the Firewall Toggle column to disable protection.
2. The system displays a secondary confirmation pop-up window, showing the list of traffic diversion resources to be cleared (including Traffic diversion in VPC, Private Link terminal node and Region).
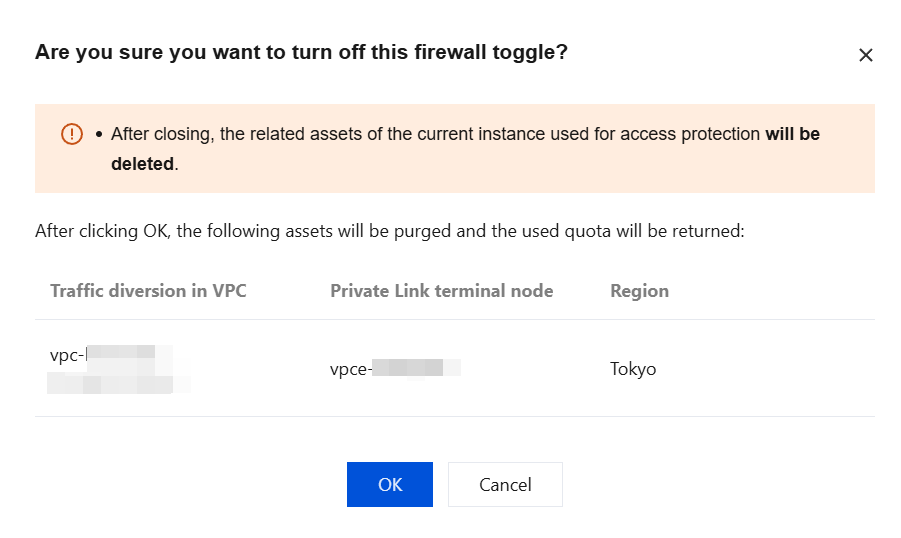
Note:
After the Firewall Toggle is disabled, the traffic diversion resources used by the current instance for protection access will be cleared, and the used general instance quota will be released.
3. After confirming that everything is correct, click OK to complete the disabling.
Overview Metrics
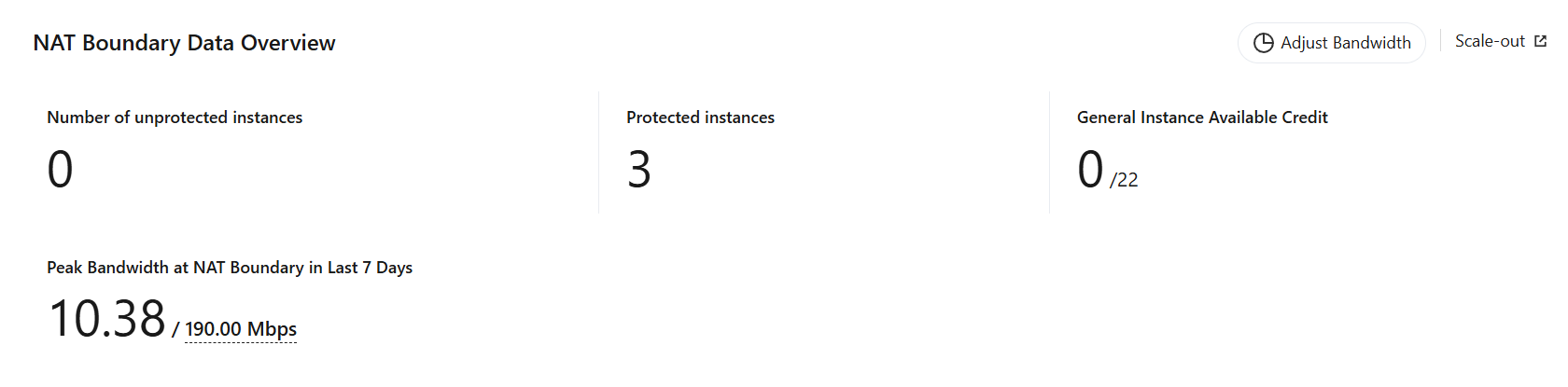
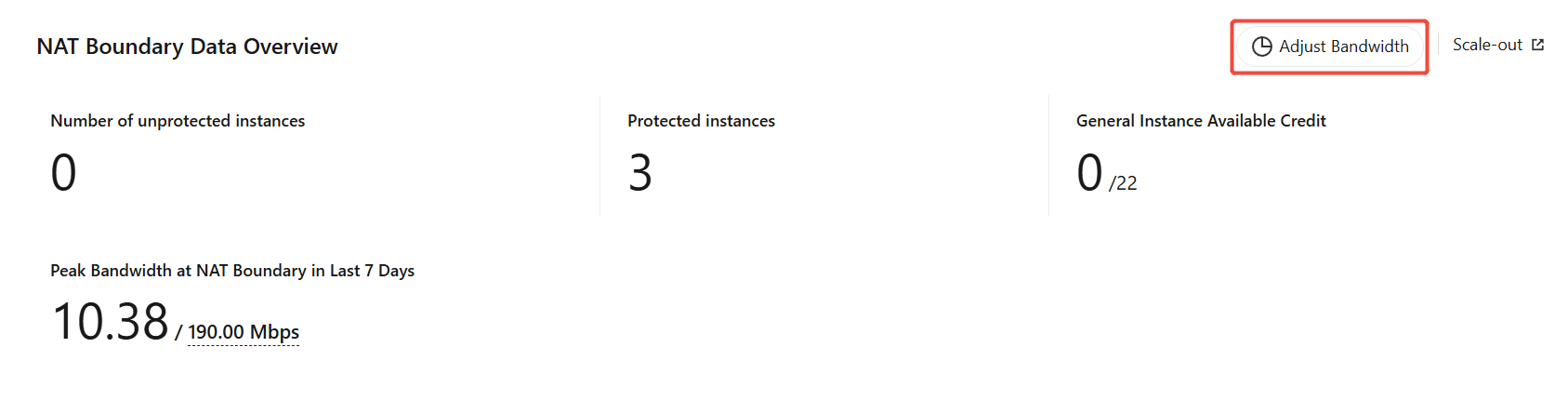
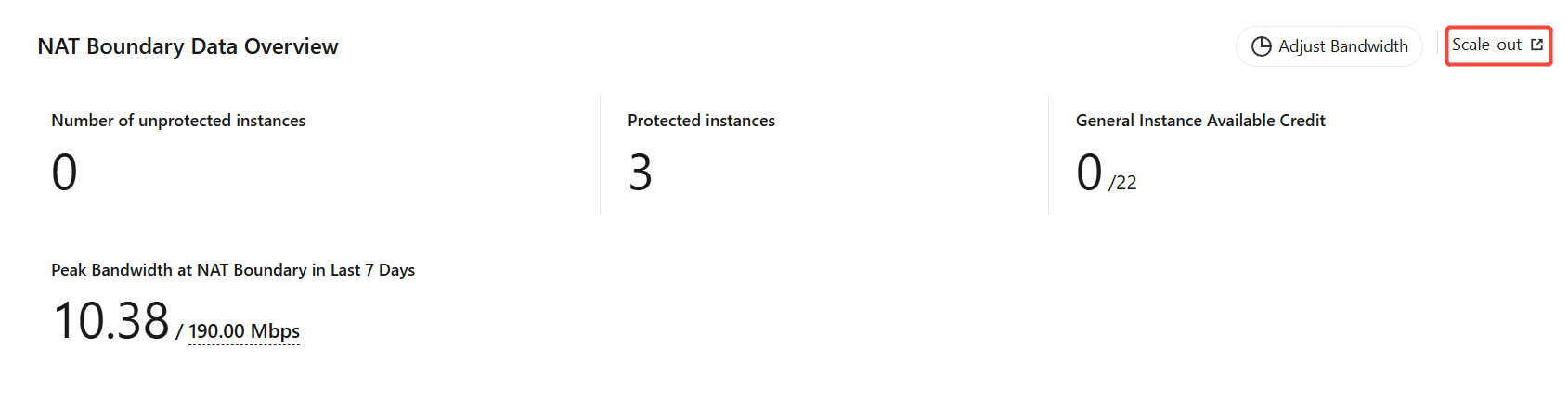
The following overview metrics and trend charts are displayed at the top of the NAT Boundary (Cluster) page:
Left-side Overview Metrics:
Metric | Description |
Number of unprotected instances | Number of instances in the NAT firewall list with the Firewall Toggle disabled |
Protected instances | Number of instances in the NAT firewall list with the Firewall Toggle enabled |
General Instance Available Credit | Currently used / Total quota |
Peak Bandwidth at NAT Boundary in Last 7 Days | Actual peak bandwidth of the NAT boundary (cluster) in the last 7 days / Allocated bandwidth |
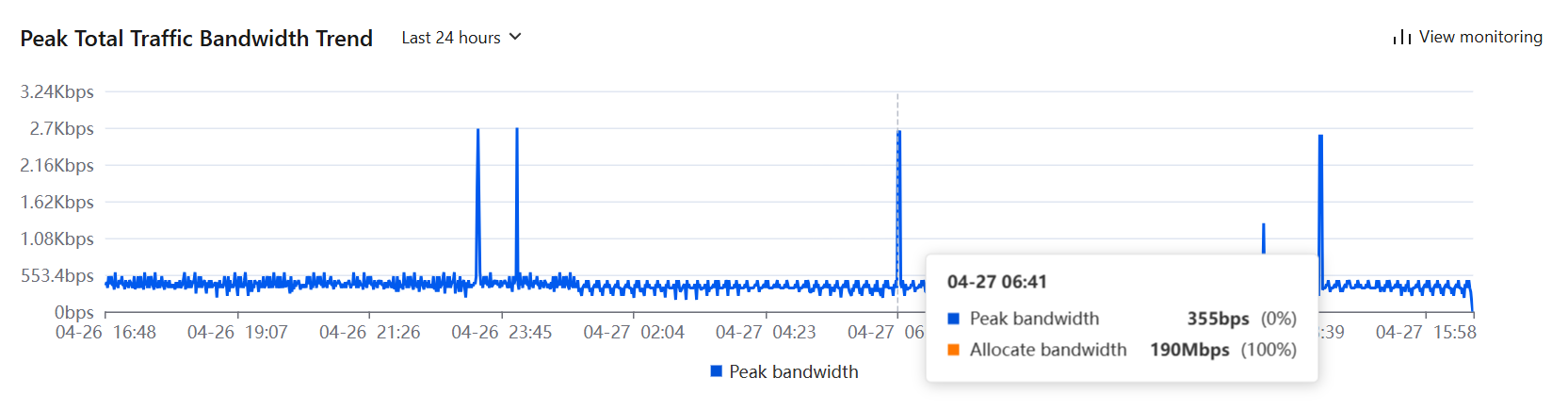
Right-side Total Traffic Peak Bandwidth Trend Chart:
It displays the peak bandwidth curve and allocated bandwidth baseline, and supports switching the time range to 24 hours / 7 days / 30 days for viewing. A View monitoring link is provided in the upper-right corner, which can redirect you to the status monitoring page.
In Monitoring, select NAT Firewall (Cluster) from the firewall type dropdown to view the operational status in cluster mode.
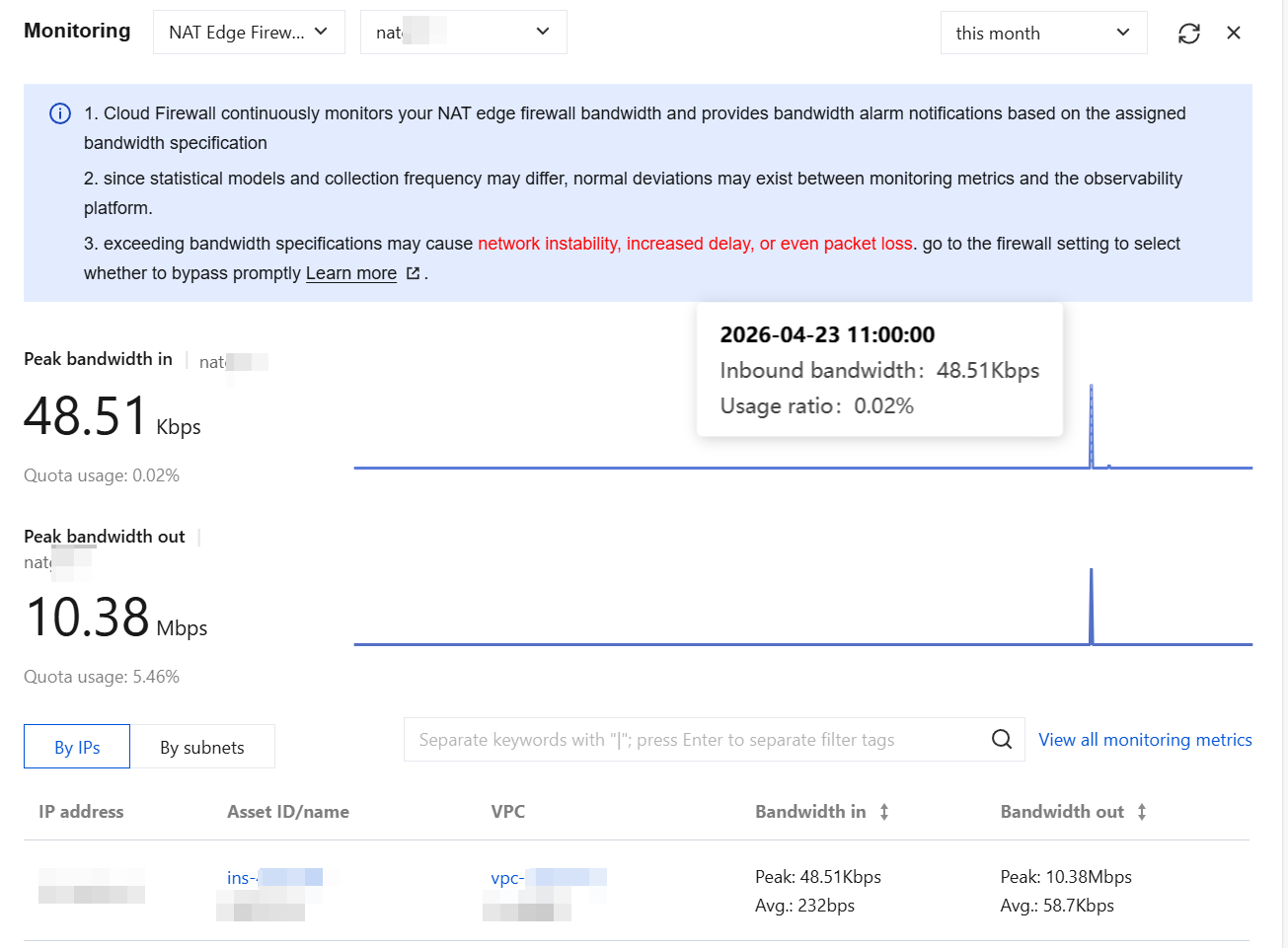
Monitoring Item | Description |
Instance selection | Select a CCN instance (dropdown displays CCN ID/name). |
Time Range | Select the time range for viewing |
Peak bandwidth in | Inbound peak bandwidth and trend chart for the selected CCN instance |
Peak bandwidth out | Outbound peak bandwidth and trend chart for the selected CCN instance |
Quota usage | Percentage of current bandwidth to allocated NAT boundary (cluster) bandwidth |
Adjusting Specifications
In cluster mode, the NAT Firewall (Cluster) bandwidth is shared among all NAT Gateway instances with the Firewall Toggle enabled. You can adjust the bandwidth by following these steps:
b. In NAT Firewall bandwidth configuration > NAT Boundary Bandwidth Configuration (Cluster Mode), click Edit.
c. Drag the bandwidth slider or directly enter the bandwidth value, then click Save.
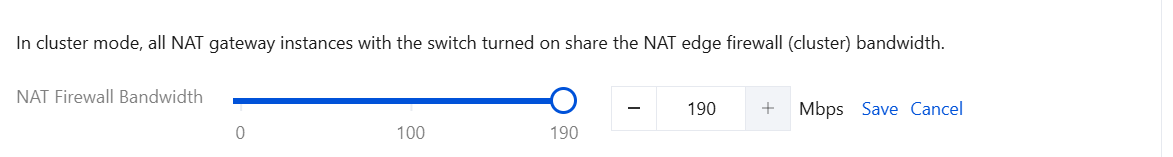
Notes:
After you adjust the bandwidth, the available bandwidth for other north-south traffic (Internet Boundary, NAT Boundary (primary/secondary)) will decrease accordingly. If you need more bandwidth, please Upgrade and Scale Out.
On the NAT Boundary (Cluster) page, click Scale-out to redirect to the Upgrade and Scale Out page, where you can scale out parameters such as bandwidth and log storage capacity.
Comparison Between Primary/Secondary Mode and Cluster Mode
Comparison Dimension | Primary-Secondary Mode | Cluster Mode |
Protection Scope | North-south traffic within the same VPC | North-south traffic across VPCs (CCN architecture) |
Deployment Architecture | Primary/secondary single-active | Active-active cluster architecture supporting elastic horizontal scaling. |
High availability | Single-active architecture. The standby node automatically takes over when the primary node fails. | Multi-active architecture with multi-node CLB. A single point of failure does not affect overall service. |
Scalability | Vertical scaling only (by upgrading single-node specifications) | Supporting both vertical scaling and horizontal scaling (by adding engine nodes). |
Access Mode | Manual instance maintenance | Automatic access / Manual access - multiple routing tables |
Engine Upgrade | Manual upgrade. The upgrade process may cause brief network jitter. | Automatic upgrade with zero service interruption. |
Intra-VPC Protection | Supported | Not supported. Can be deployed in parallel with the primary/secondary mode. |
Help and Support
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback