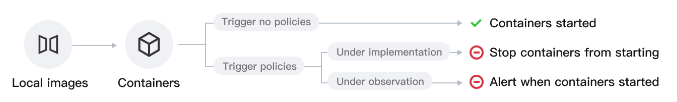
Users can configure alarms and interception policies on the Image Blocking Policies page. The Image Interception Policy allows you to intercept the startup of containers with severely security-issue-laden images to prevent malicious images from operating container services. After creating and activating an interception policy, it will take effect in about 3-5 minutes. Once active, if a detected risk image attempts to start a container, the system will alarm or intercept the container startup and report the interception records, based on the configured policy's alarm and interception requirements.
Currently supported intercepted image types: images with severe & critical vulnerabilities, Trojan viruses, sensitive information risks, and privileged mode startup images.
Privileged mode image interception supports only one rule configuration. To modify the range of intercepted images, you can edit the existing rule.
Note:
Container alert events retain data only from the past six months. Daily automated checks detect and purge alert events older than 180 days, and expired data will no longer be displayed or queried. For extended retention, Log shipping is recommended for archival purposes. Event Overview
After the user configures the image launch interception policy, if the policy becomes effective immediately, the interception of the target risk image's startup behavior will be in real-time, and event records will be reported when the target risk image starts the container. If the policy has an observation period configured, only alarms will be generated without interception. In both cases, event records will be generated.
In Image Blocking Events > Events, daily statistics will be provided for image boot interception events and alert-only events. Trend charts for both types of events over the past 7 days and the current total number of events will be displayed. Policy Overview
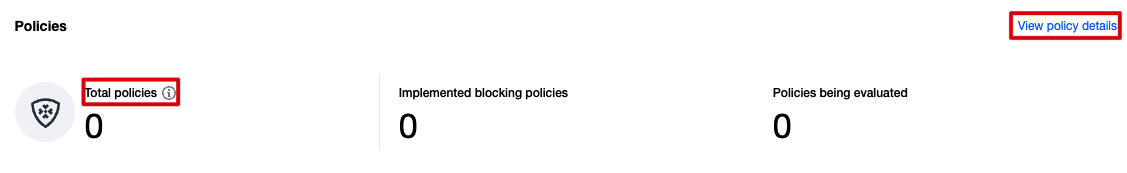
On the Image Interception Policy Page, after configuring alert and interception policies, the system will count the total number of enabled policies, as well as the number of effective interception policies and observation period policies. In Image Blocking Events > Policys, click View policy details to jump to Policy Management > Image Blocking Policies page to view the details of the image interception policy. Event List
In Image Blocking Events > Event List, recorded are the image boot interception events generated by effective interception policies and the image boot alert events generated by observation period policies. Users can filter by event type, recommended action, most recent generation time, or perform keyword searches through hit policy, image name, image ID, node name where image is located, node intranet IP, node internet IP, etc. Event type: Risky Image Interception, where the image contains certain vulnerabilities, trojans, or sensitive information, and needs interception; Privileged Image Interception, where the image is intercepted when starting a container in privileged mode.
Action: Interception Successful, indicating image boot interception events generated by effective interception policies; Alarm, indicating image boot alert events generated by observation period policies.
Users can click Details in the Operation Column to view event details, including event details, hit policy, impact range, risk description, and solution.
Event details: The system will aggregate the same interception or alert events for the same image, with the aggregation time being the current day. This section shows the event type, number of events, and time period of interception or alert events.
Hit policy: Displays the name, type, startup status, policy status, start blocking time, policy description, and policy blocking content of the effective interception or observation period policy. Users can click Details next to the policy name/policy type to view the policy details associated with this event.
Scope: Displays the name of the target image to be intercepted, the Image ID, the name and IP of the node where the image is located, etc.
Risk description: Displays the detailed reason for the interception event or alert event, such as the presence of a severe vulnerability, hitting the interception policy. Detailed image startup parameters are also displayed.
Solution: It is recommended that users repair images with vulnerabilities, trojan viruses, or sensitive information to avoid impacting the business.