Step 2: Configuring a Server Certificate
The server certificate is used to authenticate the server to clients, and the server uses the certificate you selected to establish connections with clients. To ensure cluster security, TDMQ for MQTT provides a default server certificate for performing one-way authentication. If you need to use your own certificate for authentication, you can refer to this guide to bind a custom certificate. The server certificate must be purchased or issued by youself, hosted in Tencent Cloud SSL Certificates, and then configured in the MQTT console.
Prerequisites
The CA certificate has been obtained.
OpenSSL v1.1.1i or a later version has been installed.
Step 1: Preparing a Certificate
Certificate Requirements
To ensure compatibility and security, the server certificate (End Entity Certificate) must meet the following requirements:
1. The certificate must include the X.509 v3 Extended Key Usage extension, which must contain serverAuth (TLS Web Server Authentication) as specified in the RFC 5280 standard.
To be specific, the certificate must include the necessary Subject Alternative Name (SAN) extension and Common Name (CN). Certificates issued by a publicly trusted Certificate Authority (CA) typically include these required extensions by default.
Note:
If the certificate includes both CN and SAN, when TLS Server Name Indication (SNI) selects a certificate, it will prioritize matching the domain name in the SAN extension.
Major browsers have deprecated CN matching, such as Chrome 58+ or a later version. Therefore, when using Web Secure Socket as the MQTT transport layer, you must ensure the SAN extension and Server Auth value are properly configured.
2. The certificate chain can contain up to 5 certificates.
3. The certificate chain file does not exceed 16 KiB.
Generate a Server Certificate Using a CA Certificate
You can purchase a server certificate from a trusted certificate authority or use a CA certificate to issue a server certificate. For how to obtain a CA certificate, see Configuring a CA Certificate.
If you use a self-signed CA certificate to generate a server certificate, you can follow the instructions below to generate it. After generating the server certificate, you can upload it to SSL Certificates.
1. Create the configuration file
server.conf, whose content can be modified according to actual requirements.[req]distinguished_name = req_distinguished_namereq_extensions = v3_reqprompt = no[req_distinguished_name]C = CNST = ZheJiangL = HangZhouO = ExampleCN = mqtt.example.com[v3_req]basicConstraints = critical, CA:FALSE# Common Key Usage Combinations# TLS Server: keyUsage=digitalSignature,keyEncipherment + extendedKeyUsage=serverAuth# TLS Client: keyUsage=digitalSignature + extendedKeyUsage=clientAuth# Code Signing: keyUsage=digitalSignature + extendedKeyUsage=codeSigningkeyUsage = critical, digitalSignature, keyEnciphermentextendedKeyUsage = serverAuthsubjectAltName = @alt_names[alt_names]DNS.1 = mqtt.example.comDNS.2 = www.example.comDNS.3 = api.example.comDNS.4 = *.example.comIP.1 = 192.168.1.100IP.2 = 10.0.0.50
2. Run the following command to generate the server certificate.
openssl ecparam -genkey -name prime256v1 -out server.keyopenssl req -new -key server.key -out server.csr -config server.confopenssl x509 -req -in server.csr -CA CA.crt -CAkey CA.key -CAcreateserial -out server.crt -days 365 -sha256 -extensions v3_req -extfile server.conf
openssl genrsa -out server.key 4096openssl req -new -key server.key -out server.csr -config server.confopenssl x509 -req -in server.csr -CA CA.crt -CAkey CA.key -CAcreateserial -out server.crt -days 365 -sha256 -extensions v3_req -extfile server.conf
3. Verify the server certificate.
openssl x509 -in server.crt -text -nooutopenssl verify -CAfile CA.crt server.crtopenssl x509 -in server.crt -text -noout | grep -A 10 "Subject Alternative Name"
4. Create a complete server certificate chain file.
cat server.crt > server.chain.crtcat CA.crt >> server.chain.crt
Step 2: Hosting a Server Certificate
You can upload the prepared certificate to Tencent Cloud SSL Certificates. For details, see Upload SSL Certificate Instructions.
Step 3: Binding a Custom Certificate
1. Log in to the MQTT console.
2. Click Resource > Cluster in the left sidebar. After selecting a region, click the "ID" of the target cluster to go to the cluster basic information page.
3. On the cluster details page, select the Server Certificate tab, and click Bind Custom Certificate in the top-left corner.
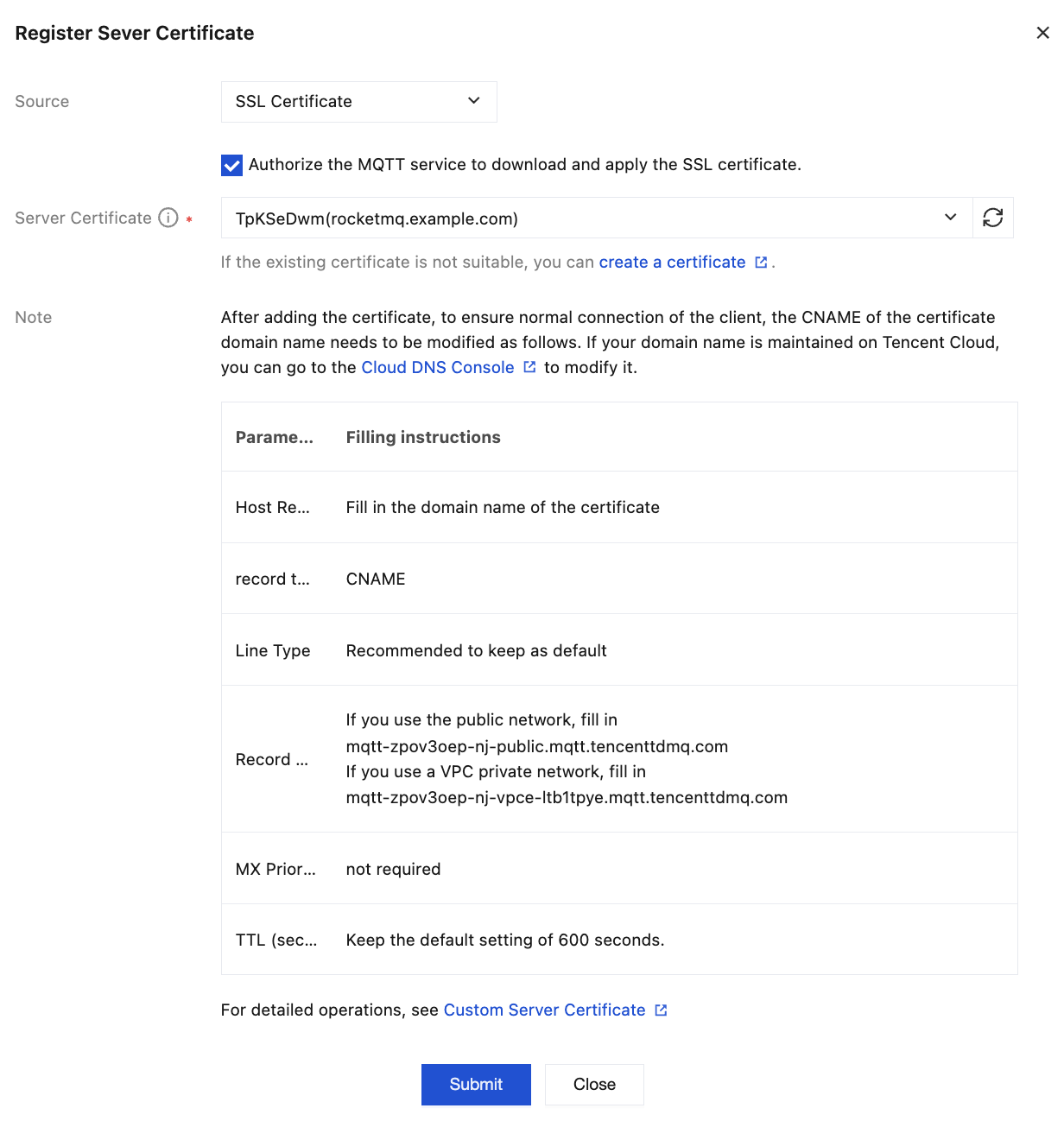
Source: Select SSL Certificates.
Server certificate: In the drop-down box, select the SSL Certificates hosted in Tencent Cloud.
4. Click Submit to complete the binding.
Step 4: Configuring a Custom Domain Name
After the certificate is added, to ensure normal client connections, the CNAME configuration for the certificate domain name must be modified accordingly. If your domain name is managed on Tencent Cloud, you can go to the DNS Resolution console to modify it.
Parameter | Description |
Host Record | Fill in the domain name for the certificate in use. |
Record Type | CNAME |
Record Value | If using a public network, enter -. If using a VPC private network, enter mqtt-xxxx-nj-vpce-xxx.mqtt.tencenttdmq.com. |
MX Priority | Not required |
TTL (seconds) | It is recommended to retain the default value of 600s. |
Assume the selected server certificate Subject Alternative Name contains the following domain names:
mqtt-abc.company.com.Refer to DNS - CNAME Record to create a CNAME record that resolves
mqtt-abc.company.com to the domain name provided by the cluster's access point: mqtt-xxx-sh-public.mqtt.tencenttdmq.com. Subsequently, the cluster can be accessed via mqtt-abc.company.com.Step 5: (Optional) Disabling the Default Server Certificate
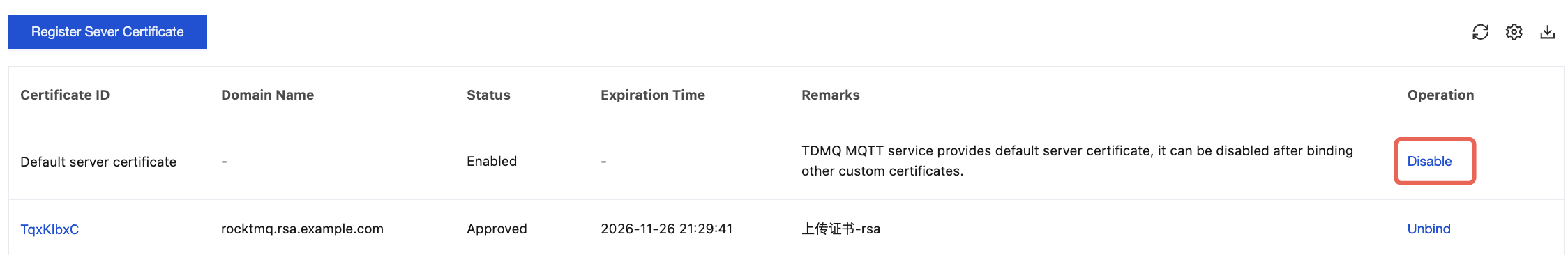
After a custom certificate is bound, you can disable the default server certificate provided by TDMQ for MQTT. The specific steps are as follows:
On the server certificate management page, click Disable in the operation column of the default server certificate. After confirmation in the pop-up window, the default certificate can be disabled.
Help and Support
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback