Step 3: Configuring a CA Certificate
TDMQ for MQTT supports the use of client certificates for client authentication. CA certificates can be used to issue client certificates, server certificates, and verification certificates. When a client initiates a connection request, it passes the client certificate to the server. The server will verify the validity of the client certificate based on the CA certificate associated with the client. If the verification passes, the client is allowed to connect to the server.
Restrictions and Limitations
The maximum number of CA certificates that can be registered in a single cluster is 32.
Issuing a CA Certificate
You can directly purchase issued CA certificates from trusted authorities or generate private CA certificates through self-signing. The following briefly describes the steps to issue a CA certificate. If you already have an issued CA certificate, you can skip the current "Issuing a CA Certificate" step.
Note:
If you are using a Windows system, you need to add the bin subdirectory of the OpenSSL installation directory to your system's PATH environment variable, as shown in the figure below.
2. Generate a CA certificate: First, generate a key pair, and then use the private key from the key pair and parameters to generate a self-signed CA certificate
CA.crt. openssl ecparam -genkey -name prime256v1 -out CA.keyopenssl req -new -x509 -key CA.key -sha256 -subj "/C=CN/ST=ZheJiang/L=HangZhou/O=TencentCloud/CN=MQTT-CA" -days 3650 -out CA.crt
openssl genrsa -out CA.key 4096openssl req -new -x509 -key CA.key -sha256 -subj "/C=CN/ST=ZheJiang/L=HangZhou/O=TencentCloud/CN=MQTT-CA" -days 3650 -out CA.crt
Note:
The domain name entered in the Common Name field must match the cluster's access point domain. It is recommended to use
*.mqtt.tencenttdmq.com.To ensure that the certificate configuration takes effect only for the current cluster, you can enter the corresponding domain name based on the usage scenario (public network or VPC network). For example, for the public network, enter
mqtt-xxxxxx-gz-public.mqtt.tencenttdmq.com; for the private network, enter mqtt-xxxxxx-gz-vpce-xxxxxx.mqtt.tencenttdmq.com.Verifying a Certificate
After the local issuance of the CA certificate is completed, you can obtain a registration code in the console and generate a corresponding verification certificate. The verification certificate is used to validate the effectiveness of the CA certificate, including whether the certificate is issued by a trusted CA.
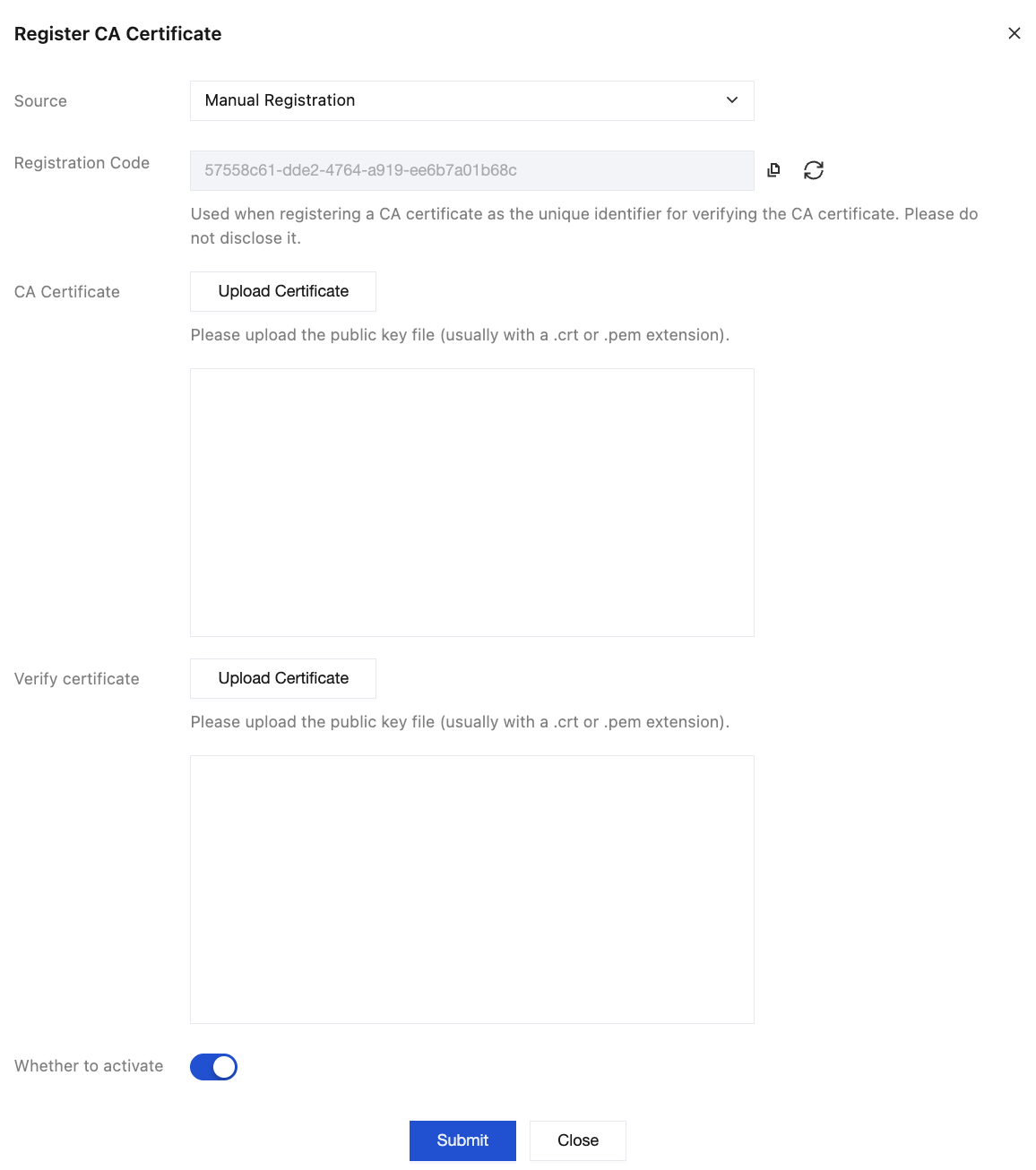
1. Obtain a registration code: Log in to the MQTT console, navigate to the CA Certificate Management page, click Register a CA Certificate, and copy the generated "Registration Code" in the pop-up window. Fill it into the
Common Name field in the next step.Note:
Do not close the current pop-up window before the verification certificate is generated and uploaded locally. Closing the pop-up will cause the registration code to be regenerated, resulting in verification certificate validation failure.
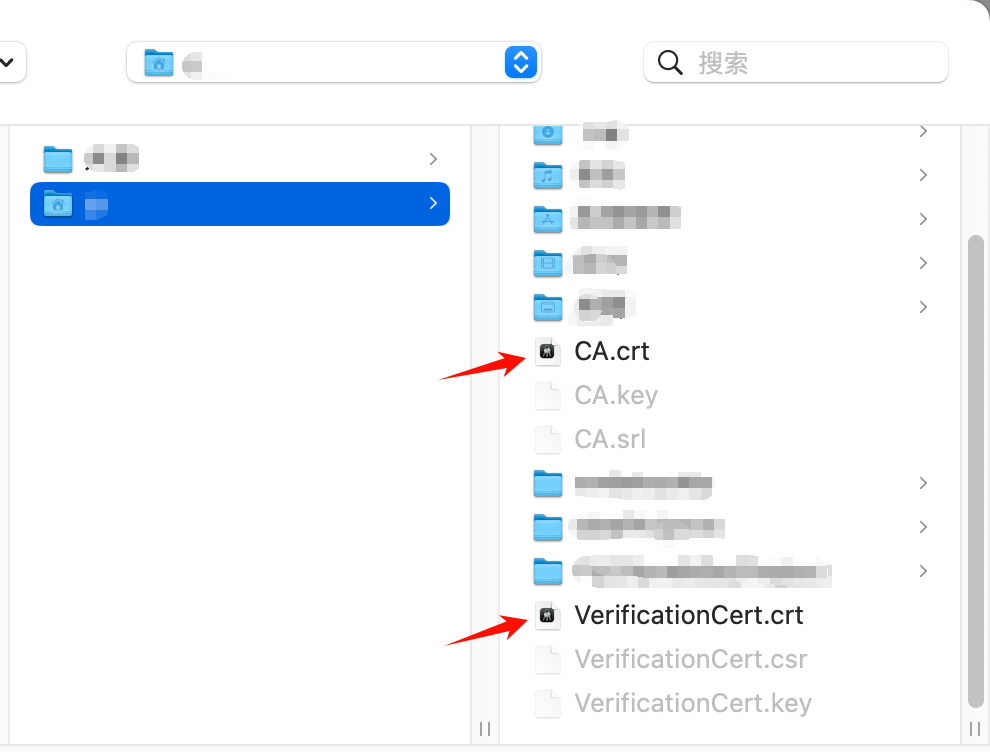
2. Generate the verification certificate: The example is as follows. Finally, the verification certificate for the CA certificate, which is VerificationCert.crt, is generated.
openssl ecparam -genkey -name prime256v1 -out VerificationCert.keyopenssl req -new -key VerificationCert.key -out VerificationCert.csr -subj "/C=CN/ST=ZheJiang/L=HangZhou/O=IoV/CN=your_registration_code"openssl x509 -req -in verify.csr -CA CA.crt -CAkey CA.key -CAcreateserial -out VerificationCert.crt -days 3 -sha256
openssl genrsa -out VerificationCert.key 4096openssl req -new -key VerificationCert.key -out VerificationCert.csr -subj "/C=CN/ST=ZheJiang/L=HangZhou/O=Tencent/OU=IT/CN=your_registration_code"openssl x509 -req -in VerificationCert.csr -CA CA.crt -CAkey CA.key -CAcreateserial -out VerificationCert.crt -days 600 -sha512
Uploading a Certificate
Return to the MQTT console pop-up window for registering CA certificates, upload the CA certificate and verification certificate, then click Submit after confirmation.
After the certificate is uploaded, the server uses the public key in the verification certificate to decrypt the signature of the CA certificate and compares it with the hash value of the content in the verification certificate. If they match, the signature is valid, thereby proving that the CA certificate is trusted.
Managing a CA Certificate
After the CA certificate is registered, on the CA certificate list page, you can view the status of the registered CA certificates. CA certificates have two statuses: Activated and Not activated. Certificates that are not activated can be deleted.
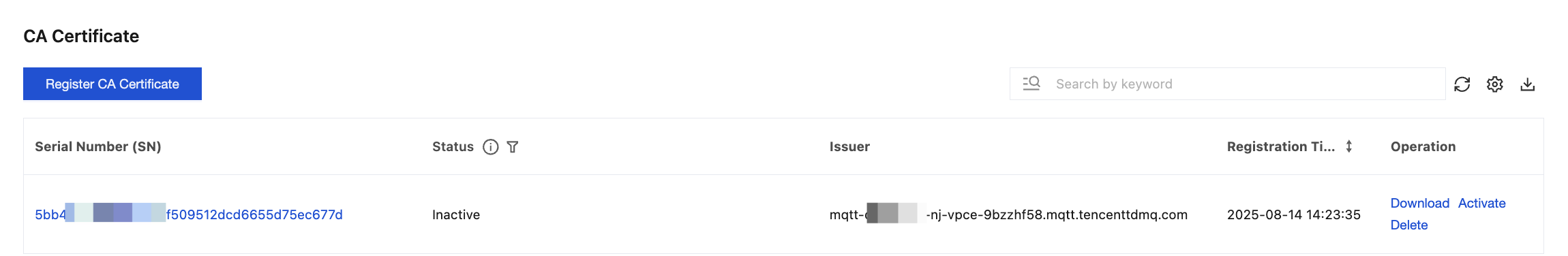
You can manage registered CA certificates on the page at any time.
Operation | Operation Path | Description |
Deactivating a Certificate | Click Deactivate in the operation bar. | After a CA certificate is deactivated, client certificates using that CA certificate will be rejected during connection. Therefore, special attention should be paid to the impact on client connections when CA certificate status is changed. |
Deleting a Certificate | Click Delete in the operation bar. | When a CA certificate is deleted, the system checks whether any client certificates (device certificates) under the CA certificate are in the "Activated" status. If such certificates exist, the deletion of the CA certificate is prohibited. If all client certificates (device certificates) under the CA certificate are in the "Not activated" or "Revoked" status, the CA certificate can be deleted. |
View Certificate Details | Click Serial Number of the certificate. | On the certificate details page, the following information of the certificate is displayed: Basic Information: Displays Status, Common Name, Serial Number, and other details of the CA certificate. Associated Client Certificates: Displays client certificates associated with the current CA certificate. Click the serial number of a client certificate to view its details. In the operation bar, you can perform management operations such as download, activate, and revoke on the client certificate. |
Help and Support
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback