- Updates and Announcements
- Product Introduction
- New/Legacy Anti-DDoS Advanced Version Differences
- Comparison of Anti-DDoS Protection Schemes
- Purchase Guide
- Getting Started
- Operation Guide
- Best Practice
- API Documentation
- FAQs
- Troubleshooting
- Anti-DDoS Advanced (Global Enterprise Edition)
- Legacy Anti-DDoS Advanced (Legacy)
- Service Level Agreement
- Contact Us
- Glossary
- Updates and Announcements
- Product Introduction
- New/Legacy Anti-DDoS Advanced Version Differences
- Comparison of Anti-DDoS Protection Schemes
- Purchase Guide
- Getting Started
- Operation Guide
- Best Practice
- API Documentation
- FAQs
- Troubleshooting
- Anti-DDoS Advanced (Global Enterprise Edition)
- Legacy Anti-DDoS Advanced (Legacy)
- Service Level Agreement
- Contact Us
- Glossary
Anti-DDoS Advanced (Global Enterprise Edition) supports CC frequency limiting for connected web applications to restrict the access frequency of source IPs. It provides multiple defense levels and is set to "Loose" by default. You can customize a frequency limiting rule to apply CAPTCHA and discard on source IPs if any IP accesses a certain page too frequently in a short time.
You can adjust your frequency limiting rules based on the real-time traffic using the following levels:
At this level, there may be a risk that a small number of abnormal requests can bypass the policy. You can change the defense level when attacks come or configure the CC frequency limit for protection.
Prerequisite
You have purchased an Anti-DDoS Advanced (Global Enterprise Edition) instance and set the object to protect.
Directions
- Log in to the Anti-DDoS Advanced (Global Enterprise Edition) console and select Anti-DDoS Advanced > Configurations > CC Protection.
- Select an Anti-DDoS Advanced instance ID in the list on the left, such as "bgp-00xxxxxx".
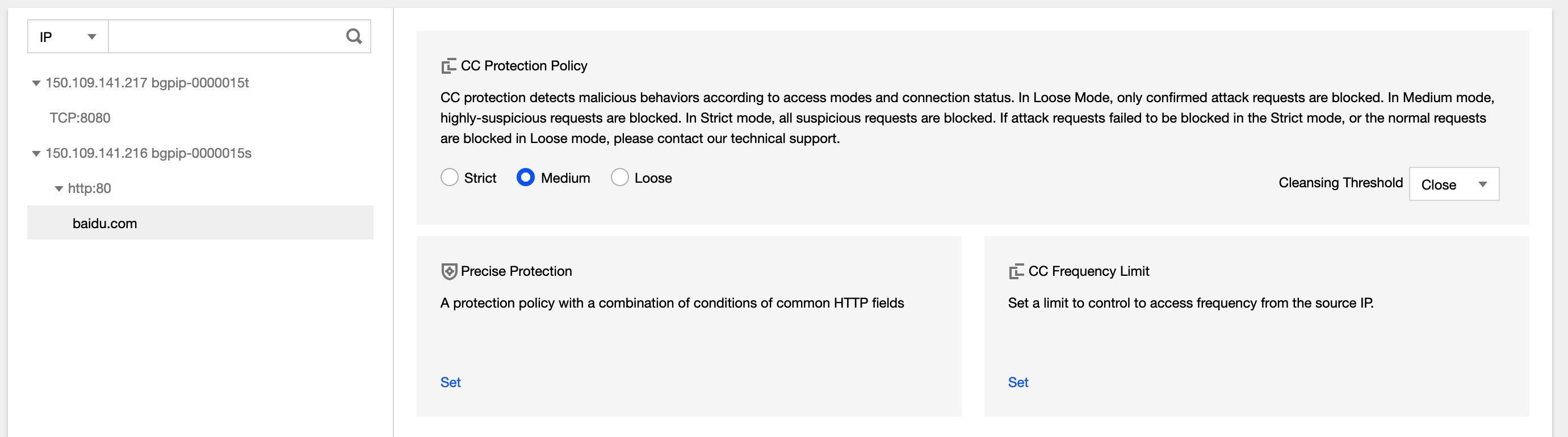
- Click Set in the CC Frequency Limit section.
- Click Create. Select or add a domain name, turn on the "Defense" switch, and then select an appropriate defense level.
- To configure custom rules, click Add Rule. On the pop-up page, enter the required fields and click OK.
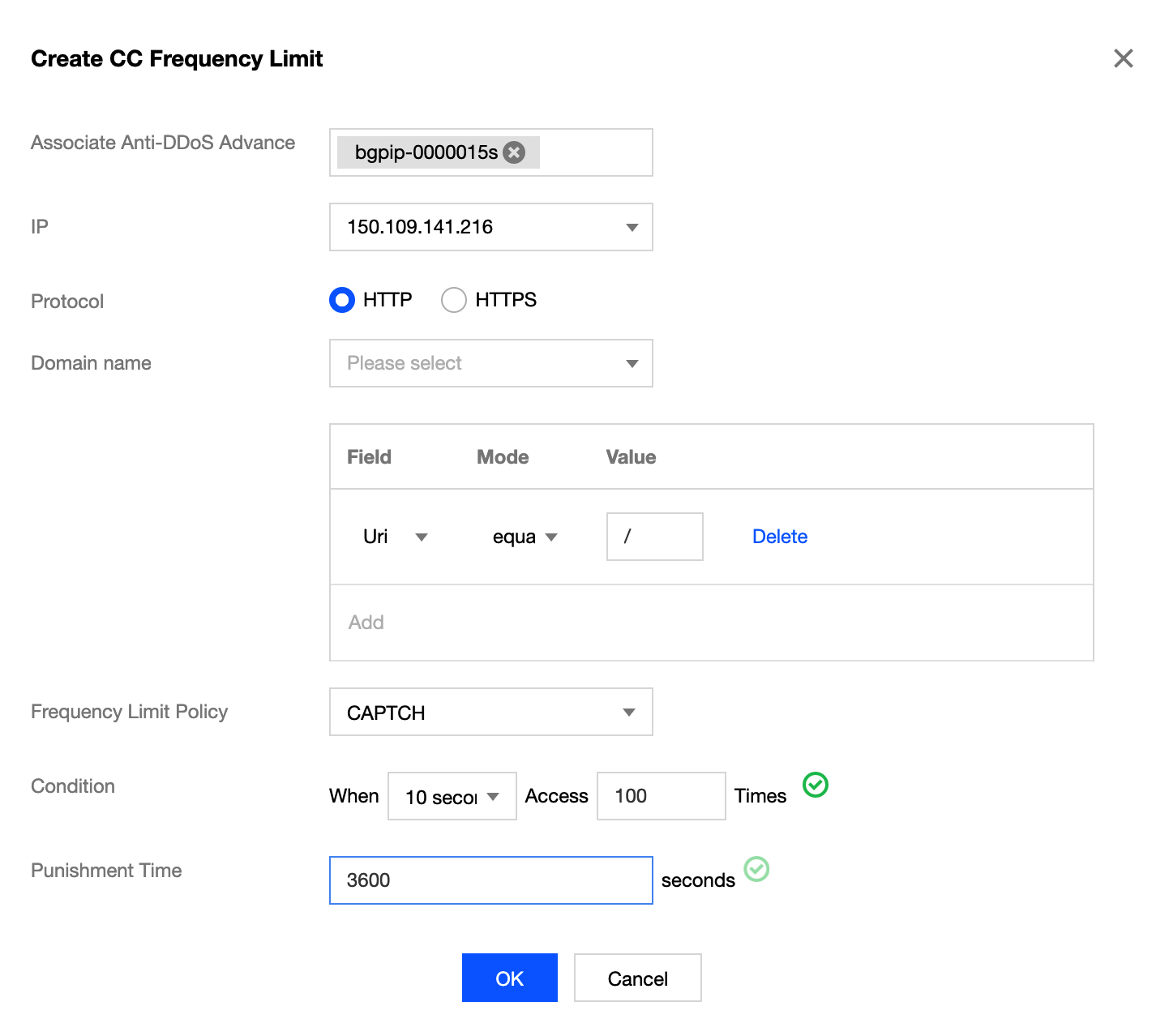
Parameter description:
- For "Domain name", select a domain name.
- For "Action", set to "Discard" or "CAPTCH".
- If "Discard" is selected, requests that matched the specified conditions will be discarded.
- If "CAPTCH" is selected, requests that matched the specified conditions will be verified via CAPTCH.
- For "Condition", set the number of requests that are allowed to access a source IP within a specified period.
- For "Punishment time", set a time period.
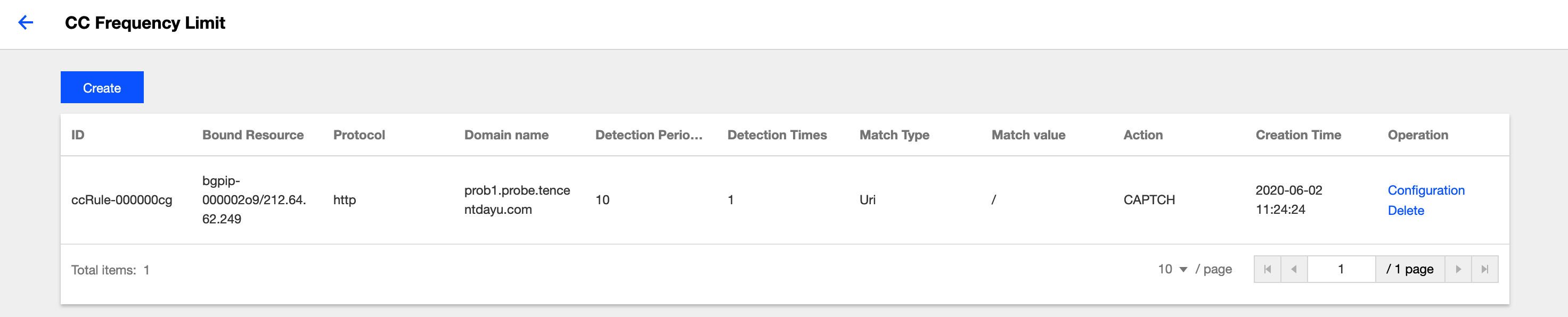
- After the rule is created, it is added to the rule list. You can click Configuration on the right of the rule to modify it.

 Yes
Yes
 No
No
Was this page helpful?