Release Notes
Announcements
POST Object, you can add content-length-range in the HTML form to control the object size in this request as follows:[ "content-length-range", minNum, maxNum ]
[ "content-length-range", 1, 10]
{"expiration": "2021-12-31T12:00:00Z","conditions": [{ "bucket": "examplebucket-1250000000" },[ "starts-with", "$key", "exampleobject" ],{ "q-ak": "AKIDQjz3ltompVjBni5LitkWHFlFpwkn****" },{ "q-sign-algorithm": "sha1" },{ "q-sign-time": "1567150692;1567157892" },[ "content-length-range", 1, 10 ]]}
HTTP/1.1 204Content-Length: 0Connection: closeDate: Wed, 23 Aug 2020 08:14:53 GMTETag: "ee8de918d05640145b18f70f4c3aa602"Location: http://examplebucket-1250000000.cos.ap-guangzhou.myqcloud.com/exampleobjectServer: tencent-cosx-cos-request-id: NWQ2NzgxMzZfMmViMDJhMDlfY2NjOF84NGQz****
HTTP/1.1 400 Bad RequestContent-Type: application/xmlContent-Length: 498Connection: keep-aliveDate: Wed, 23 Aug 2020 08:14:53 GMTServer: tencent-cosx-cos-request-id: NTk5ZDM5N2RfMjNiMjM1MGFfMmRiX2Y0****<?xml version='1.0' encoding='utf-8' ?><Error><Code>EntityTooLarge</Code><Message>Condition key content-length-range doesn‘t match the value </Message><Resource>examplebucket-1250000000.cos.ap-guangzhou.myqcloud.com/exampleobject</Resource><RequestId>NTk5ZDM5N2RfMjNiMjM1MGFfMmRiX2Y0****</RequestId></Error>
HTTP/1.1 400 Bad RequestContent-Type: application/xmlContent-Length: 498Connection: keep-aliveDate: Wed, 23 Aug 2020 08:14:53 GMTServer: tencent-cosx-cos-request-id: NTk5ZDM5N2RfMjNiMjM1MGFfMmRiX2Y0****<?xml version='1.0' encoding='utf-8' ?><Error><Code>EntityTooSmall</Code><Message>Condition key content-length-range doesn‘t match the value </Message><Resource>examplebucket-1250000000.cos.ap-guangzhou.myqcloud.com/exampleobject</Resource><RequestId>NTk5ZDM5N2RfMjNiMjM1MGFfMmRiX2Y0****</RequestId></Error>
POST Object but not PUT Object. Moreover, since the requester can still modify the parameter in requests, uploading objects beyond the specified size range is still possible, making it hard for central management.cos:content-length.Condition Field | Description | Example |
numeric_greater_than | A number greater than | {"numeric_greater_than": {"cos:content-length": 1}}, The object size must be greater than 1 byte. |
numeric_greater_than_equal | A number greater than or equal to | {"numeric_greater_than_equal": {"cos:content-length": 1}}, The object size must be greater than or equal to 1 byte. |
numeric_less_than | A number smaller than | {"numeric_less_than": {"cos:content-length": 1}}, The object must be smaller than 1 bytes. |
numeric_less_than_equal | A number smaller than or equal to | {"numeric_less_than_equal": {"cos:content-length": 1}}, The object must be smaller than 10 bytes. |
{"version": "2.0","statement": [{"effect": "allow","action": ["cos:PutObject","cos:PostObject"],"resource":["qcs::cos:ap-guangzhou:uid/1250000000:examplebucket-1250000000/*"],"condition": {"numeric_greater_than_equal": {"cos:content-length": 1}, "numeric_less_than": {"cos:content-length": 10}}}]}
PUT Object or POST Object API to upload objects to the examplebucket-1250000000 bucket, with the object sizes limited to [1, 10), in bytes.cos:PutObject and cos:PostObject actions. Using other actions such as cos:GetObject will fail.HTTP/1.1 403 ForbiddenContent-Type: application/xmlContent-Length: 298Connection: keep-aliveDate: Wed, 23 Aug 2020 08:14:53 GMTServer: tencent-cosx-cos-request-id: NTk5ZDM5N2RfMjNiMjM1MGFfMmRiX2Y0****
content-type to specify the file type, as shown in the image below:
{"Statement": [{"Action": ["name/cos:PutObject"],"Effect": "Allow","Principal": {"qcs": ["qcs::cam::anyone:anyone"]},"Resource": ["qcs::cos:ap-nanjing:uid/1250000000:examplebucket-1250000000/*"],"Condition": {"ForAllValues:StringEquals": {"cos:content-type":["image/png"]}}],"version": "2.0"}
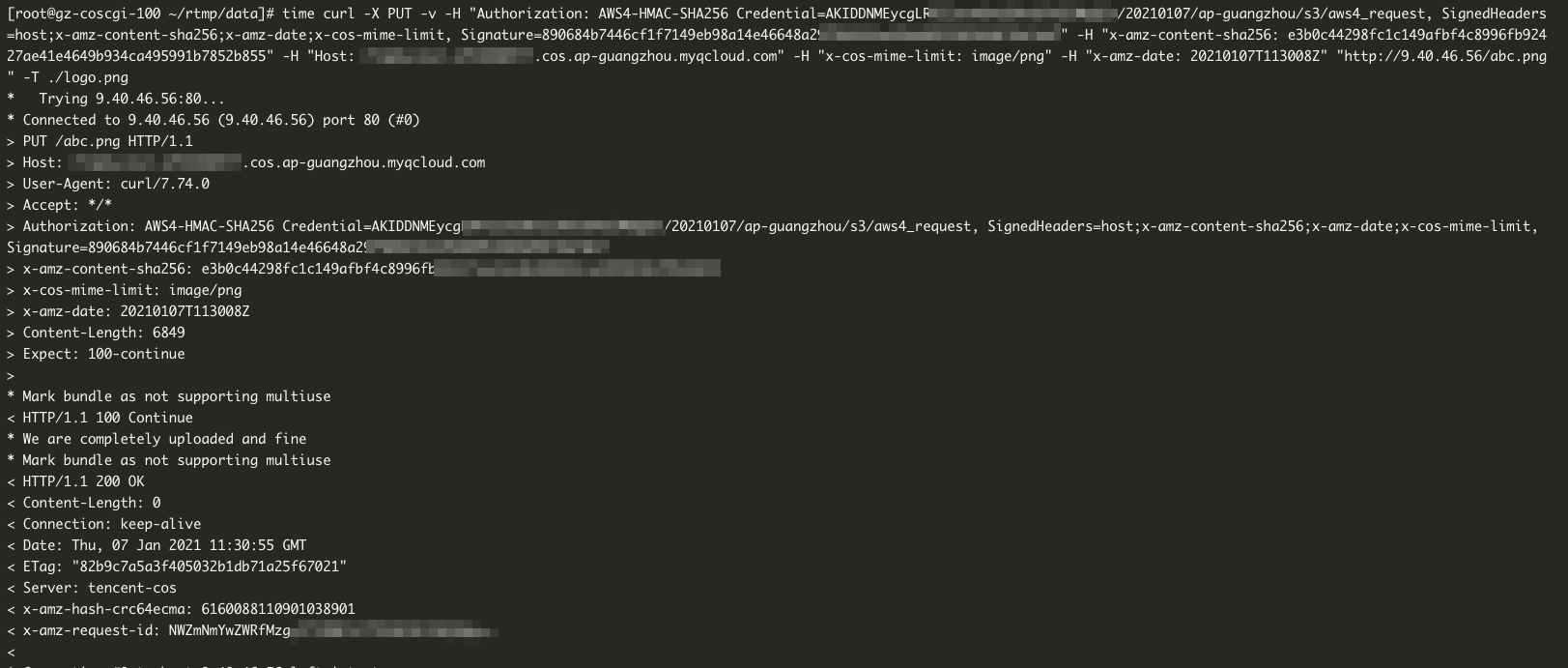
PNG files to be uploaded, and upload a PNG format file:PNG format file is successful:
JPEG format file is successful:
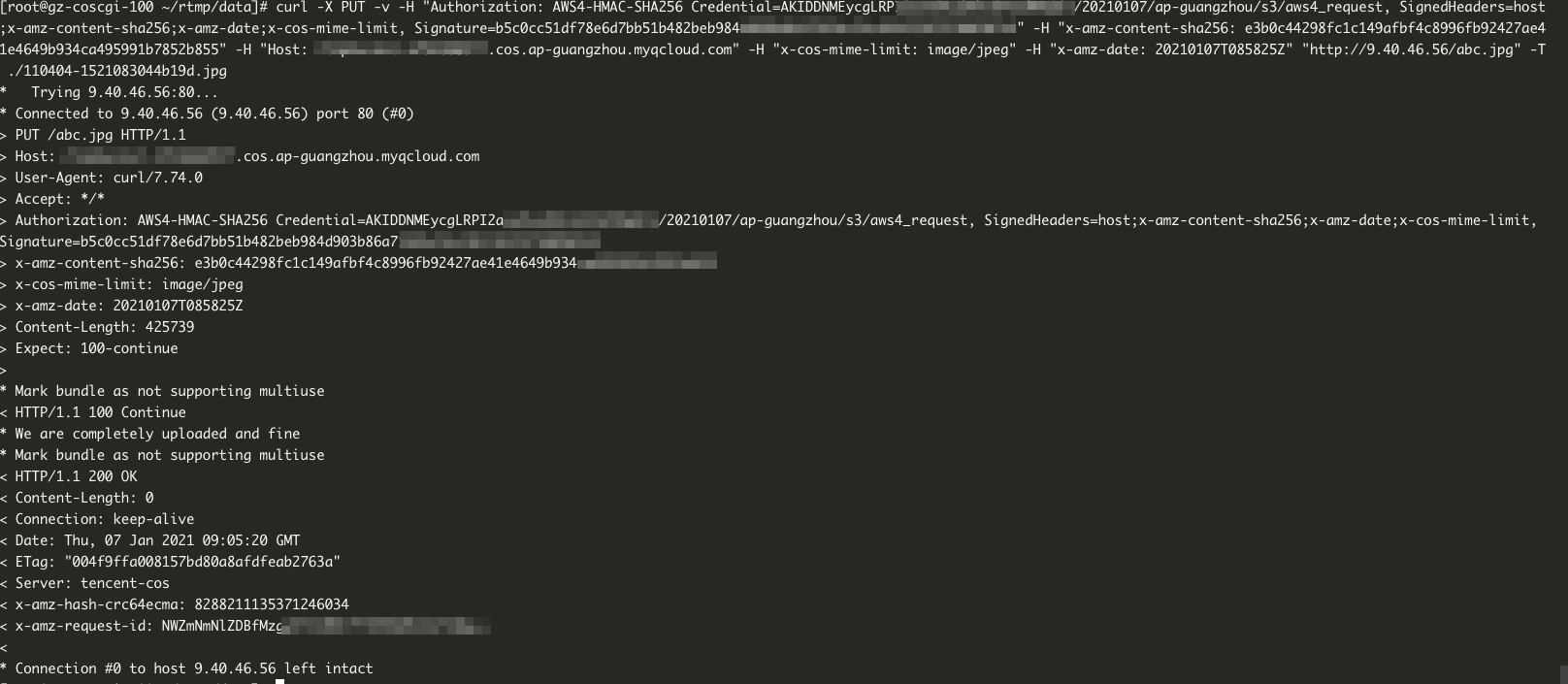
PNG format files from being uploaded to COS.Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback