API Gateway TKE Tunnel Configuration
Download
Modo Foco
Tamanho da Fonte
Scenario
You can directly access Pods in a TKE cluster through API Gateway without passing through CLB. This document describes how to create a TKE tunnel and configure it as the backend type of an API in the console, so that requests from API Gateway go directly to the corresponding Pod of the TKE tunnel.
Feature strengths
API Gateway is directly connected to the Pods of the TKE cluster, reducing intermediate nodes (such as CLB).
A TKE tunnel can connect multiple TKE clusters at the same time.
Note
TKE tunnels are currently only supported by dedicated API Gateway instances.
Prerequisites
1. You have a dedicated instance.
2. You have a TKE cluster and have obtained its admin role.
Directions
Step 1. Create a TKE tunnel
1. Log in to the API Gateway console.
2. Select Backend Tunnel on the left sidebar and click Create.
3. On the Create Backend Tunnel page, enter the following information:
Backend Tunnel Name: Enter a custom name.
Tunnel Type: Select TKE tunnel.
VPC: Select a VPC.
Service List: Up to 20 services can be configured in the service list. The weighted round robin algorithm is used to distribute traffic among multiple Pods. The steps to configure a service are as follows:
3.1.1 Enter the weight ratio of each Pod of the service.
3.1.2 Select the cluster. If the cluster has not been authorized, API Gateway will request authorization.
3.1.3 Select a namespace in the cluster.
3.1.4 Select the service and its port.
3.1.5 Advanced options: Select additional node labels.
Backend Type: Select HTTP or HTTPS.
Host Header: Optional. It is the value of host in the request header carried in the HTTP/HTTPS request when API Gateway accesses the backend service.
Tag: Optional. A tag is used to manage resources by category from different dimensions.
Step 2. Connect the API backend to the TKE tunnel
1. On the Service page in the API Gateway console, click the target service ID to enter the API management page.
2. Click Create to create a general API.
3. Enter the frontend configuration information and click Next.
4. Select VPC resources as the backend type, select TKE tunnel as the backend tunnel type, and click Next.
5. Set the response result and click Complete.
Network Architecture
After the TKE tunnel is bound to the API, the architecture of the entire network is as follows:
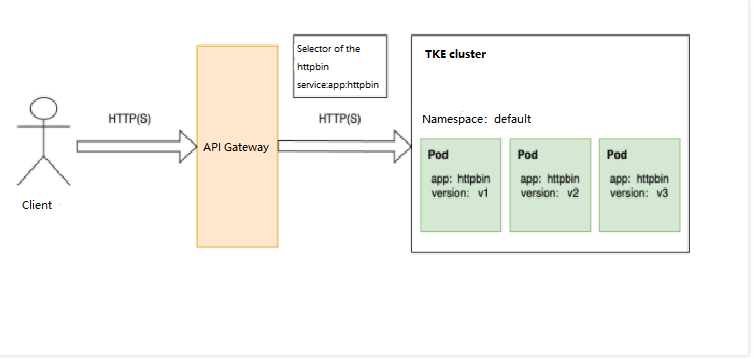
API Gateway directly accesses the Pods in the TKE cluster without passing through CLB. The YAML configuration file of the cluster's httpbin service is as follows, where the
selector indicates that the Pod with the tag key app and tag value httpbin is selected as the node of the TKE tunnel. Therefore, Pods on versions 1/2/3 are also nodes of the TKE tunnel.apiVersion: v1kind: Servicemetadata:name: httpbinlabels:app: httpbinservice: httpbinspec:ports:- name: httpport: 8000targetPort: 80selector:app: httpbin
Reminders
A TKE tunnel can connect up to 20 TKE services.
You should have the admin role of the TKE cluster.
The TKE tunnel and the dedicated API Gateway instance must be in the same region. Currently, API Gateway doesn't support cross-VPC access.
Ajuda e Suporte
Esta página foi útil?
Você também pode entrar em contato com a Equipe de vendas ou Enviar um tíquete em caso de ajuda.
comentários