Usage
Download
Focus Mode
Font Size
How do I download access logs of the last 180 days?
When Access Logs is enabled, WAF stores the logs for at least 180 days. You can query and download access logs of the last 30 days. To download logs of the last 180 days, please submit a ticket.
Does WAF support health check?
SaaS WAF supports a four-layer health check mechanism, which can be enabled for Enterprise Edition and above versions when the domain is accessed. After enabling, it actively detects the health status of all source IP addresses every 3 seconds. For more information, please submit a ticket.
Does WAF support session persistence?
Will logging still be available once WAF is disabled for the domain name list?
No. Once WAF is disabled, all its protection features are unavailable, and only the traffic forwarding mode starts to run instead, with no logs recorded.
When will a configuration change take effect?
In general, a configuration change takes effect within 10 seconds.
Note
It applies to connection configurations (including setting the real server, link mode, and whether to enable HTTP2.0).
The VIP of WAF-protected domain name is blocked due to DDoS attacks. What should I do?
WAF VIP addresses come with 2-GB Anti-DDoS Basic protection bandwidth. When you need to recover your business immediately after the VIP is blocked, purchase an Anti-DDoS Pro instance and bind it to the VIP address.
If the uploaded files are blocked, will they still be blocked with HTTPS or SFTP?
If WAF is disabled, the file will not be blocked. If WAF is enabled and the blocking mode is set, WAF will block malicious files uploaded over HTTP or HTTPS, but will not block files uploaded over SFTP. SFTP is a non-HTTP or non-HTTPS protocol beyond the protection of WAF.
Will the persistent connection be disconnected when the WAF certificate is changed?
No. Updating the certificate will reload nginx, and the thread will not be recycled until the end of the old request session, so it will not be disconnected.
What cipher suite does the SaaS WAF or CLB WAF support?
SaaS WAF does not support SSL cipher suites.
CLB WAF supports:
ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:ECDHE-RSA-CHACHA20-POLY1305:DHE-RSA-CHACHA20-POLY1305:kEDH+AESGCM:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128:AES256:AES:HIGH:!aNULL:!eNULL:!EXPORT:!DES:!RC4:!MD5:!PSK
WAF supports the following TLS versions:
TLSv1, TLSv1.1, and TLSv1.2.
Cipher suites: EECDH+CHACHA20:EECDH+AES128:RSA+AES128:EECDH+AES256:RSA+AES256:EECDH+3DES:RSA+3DES:!MD5.
Note
SaaS WAF supports ECDHE cipher suites by default (such as TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA).
Customization for TLS protocol and cipher suite is available in the Exclusive edition.
How do I query the module hit by a block page?
1. When a malicious request is detected, WAF blocks the request and returns a block page with a UUID.
2. You can copy the UUID and search for it on the Attack Logs page.
Note
Specify the query period.
Check information of the hit rule in the log fields:
attack_type, rule_id, and attack_content.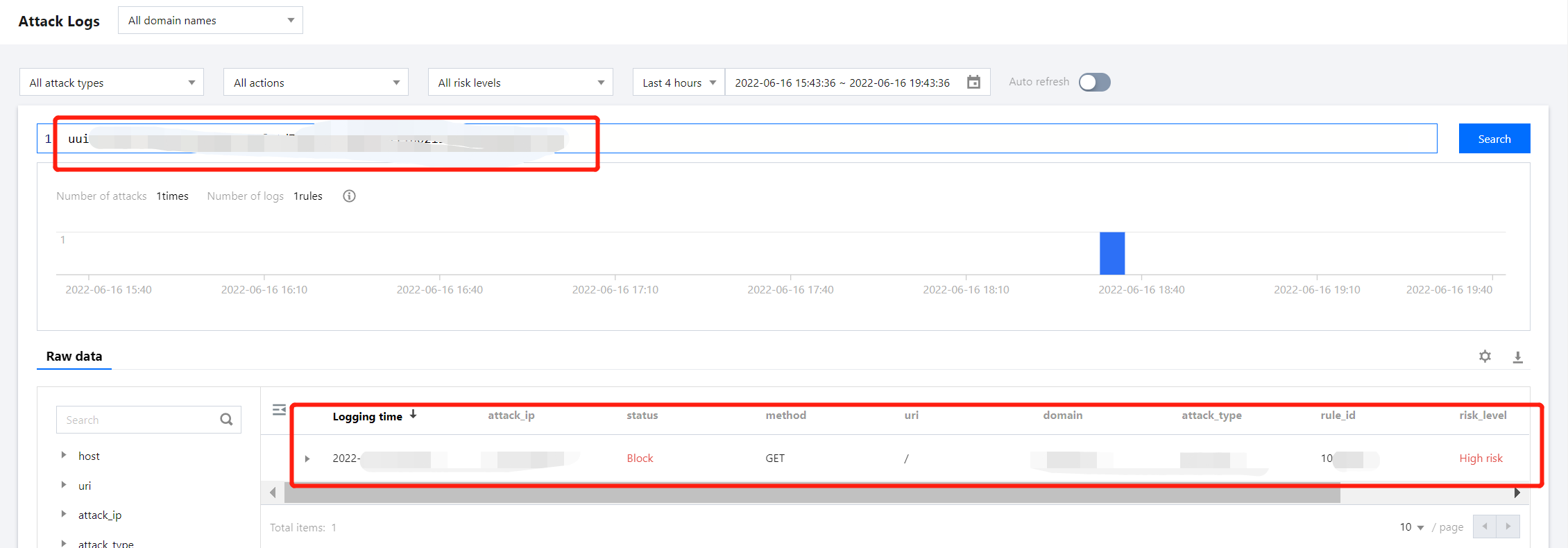
Help and Support
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback