Release Notes
Announcements
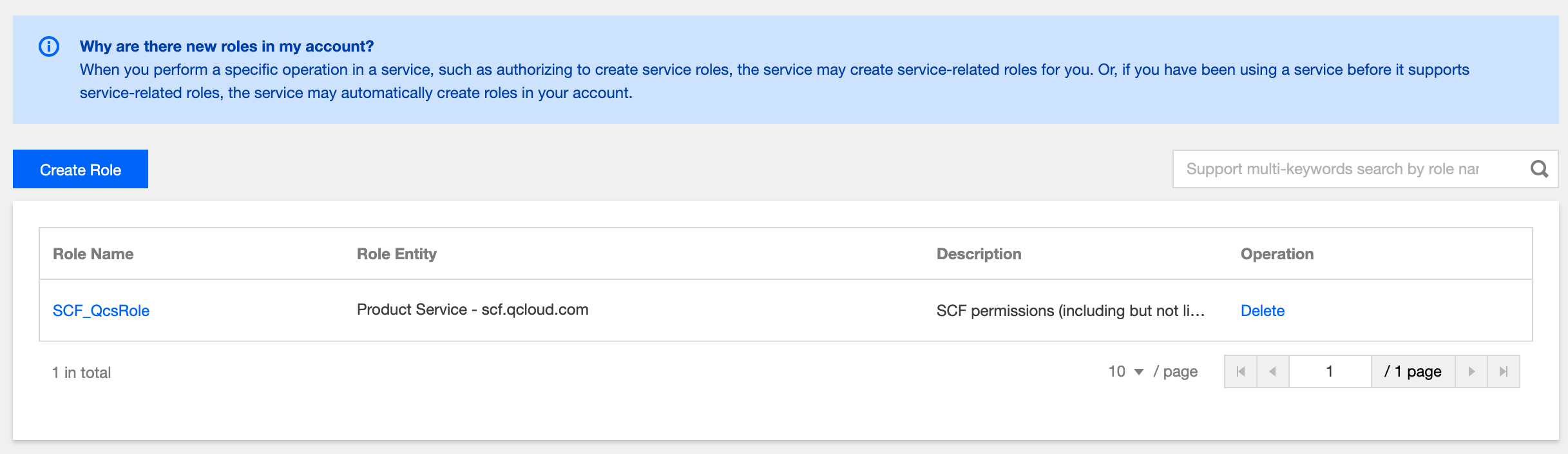
SCF_QcsRoleservice-scf.qcloud.comQcloudAccessForScfRole policy that can:SCF_QcsRole; however, modifying the associated policy of the role may cause SCF to fail; therefore, you are not recommended to modify it.SCF_QcsRole role is used to grant SCF the permissions to read and manipulate user resources during configuration. If you receive an error for missing role or permission when managing functions (such as using TCCLI or VS Code plugin to update function code), you need to configure the SCF_QcsRole role.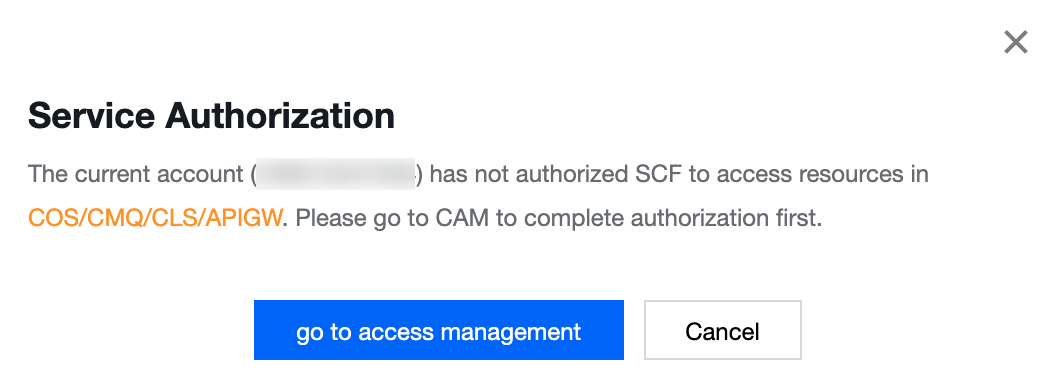
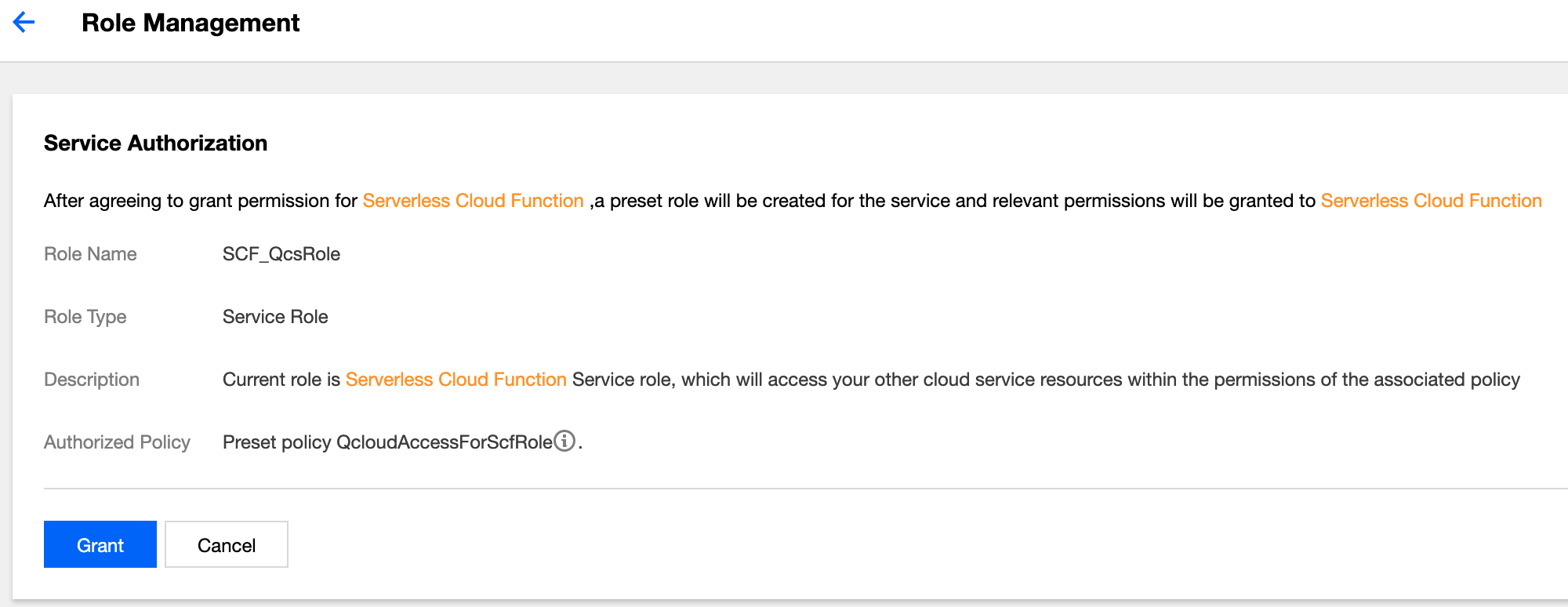
SCF_QcsRole will be automatically created for you as shown below:
QcloudSCFFullAccess and QcloudSCFReadOnlyAccess were modified, and the QcloudAccessForScfRole policy was added for the configuration role SCF_QcsRole as shown below:QcloudSCFFullAccess has the following permissions:{"version":"2.0","statement":[{"action":["scf:*","tag:*","cam:DescribeRoleList","cam:GetRole","cam:ListAttachedRolePolicies","apigw:DescribeServicesStatus","apigw:DescribeService","apigw:DescribeApisStatus","cmqtopic:ListTopicDetail","cmqqueue:ListQueueDetail","cmqtopic:GetSubscriptionAttributes","cmqtopic:GetTopicAttributes","cos:GetService","cos:HeadBucket","cos:HeadObject","vpc:DescribeVpcEx","vpc:DescribeSubnetEx","cls:getTopic","cls:getLogset","cls:listLogset","cls:listTopic","ckafka:List*","ckafka:Describe*","monitor:GetMonitorData","monitor:DescribeBasicAlarmList","monitor:DescribeBaseMetrics","monitor:DescribeSortObjectList","monitor:DescribePolicyConditionList","cdb:DescribeDBInstances"],"resource":"*","effect":"allow"}]}
QcloudSCFReadOnlyAccess has the following permissions:{"version": "2.0","statement": [{"action": ["scf:Get*","scf:List*","ckafka:List*","ckafka:Describe*","monitor:GetMonitorData","monitor:DescribeBasicAlarmList","monitor:DescribeBaseMetrics","monitor:DescribeSortObjectList","cam:GetRole","cam:ListAttachedRolePolicies","vpc:DescribeVpcEx","vpc:DescribeSubnetEx","cls:getLogset","cls:getTopic","cls:listTopic","apigw:DescribeService","cmqtopic:GetTopicAttributes","cmqtopic:GetSubscriptionAttributes","cos:HeadBucket","cos:GetService","cos:GetObject"],"resource": "*","effect": "allow"}]}
QcloudAccessForScfRole has the following permissions:{"version": "2.0","statement": [{"action": ["ckafka:List*","ckafka:Describe*","ckafka:AddRoute","ckafka:CreateRoute","apigw:ReleaseService","apigw:CreateService","apigw:CreateApi","apigw:DeleteApi","cls:*","cos:List*","cos:Get*","cos:Head*","cos:PutBucket","cos:OptionsObject","cmqqueue:*","cmqtopic:*"],"resource": "*","effect": "allow"}]}
QcloudAccessForScfRole can:Apakah halaman ini membantu?
Anda juga dapat Menghubungi Penjualan atau Mengirimkan Tiket untuk meminta bantuan.
masukan