Kebijakan Privasi
Perjanjian Pemrosesan dan Keamanan Data




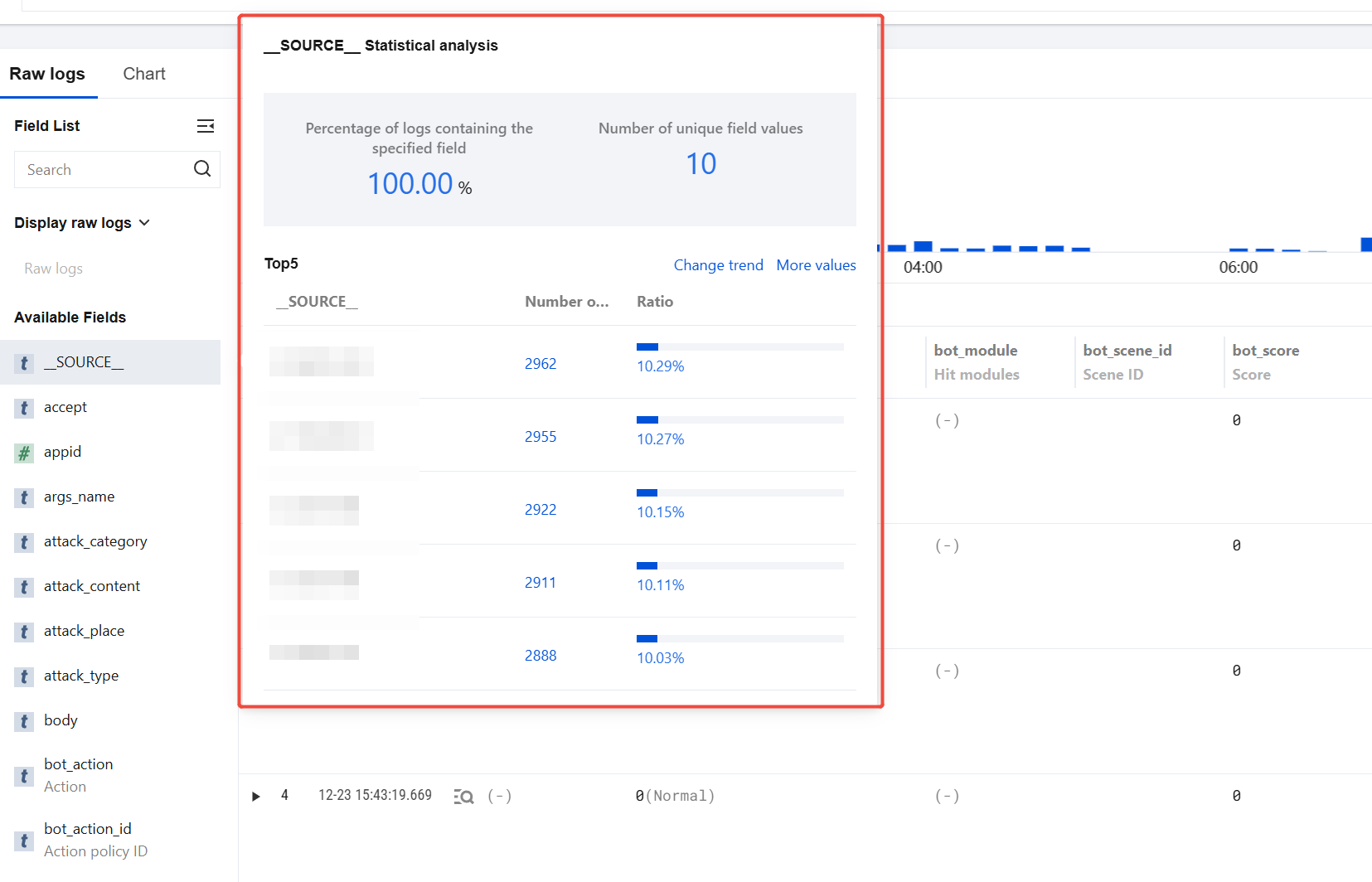





*.abc.com) is selected, logs from all associated subdomains (ending with .abc.com) will also be downloaded.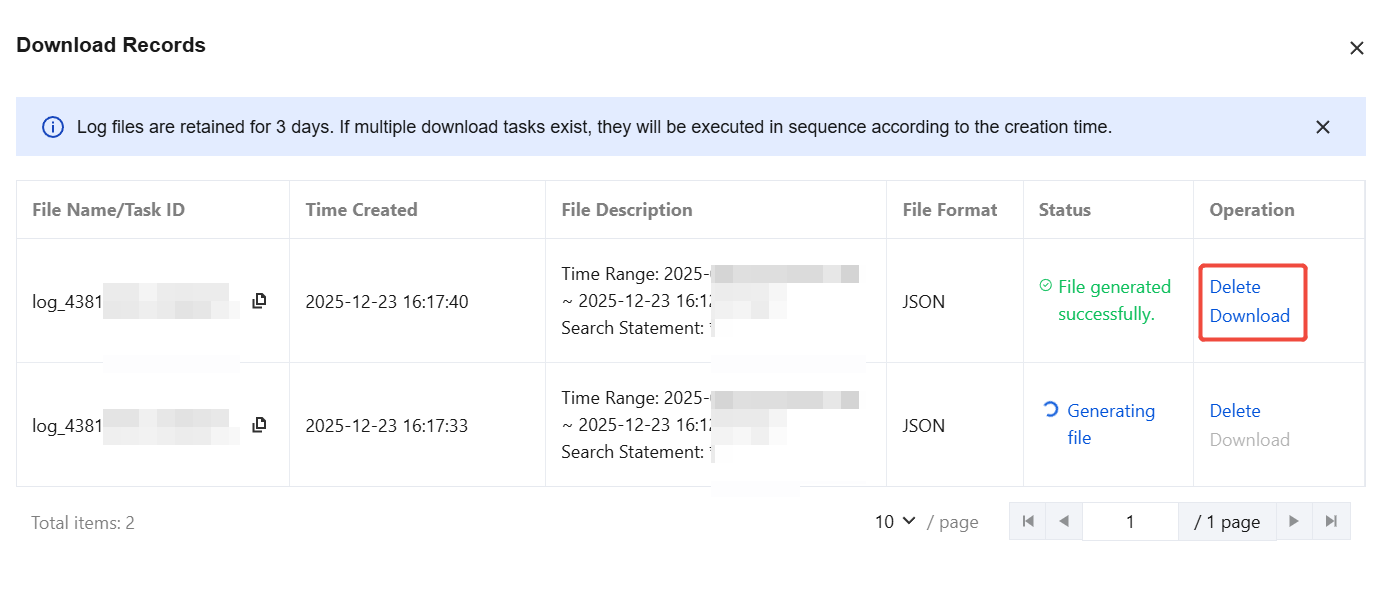
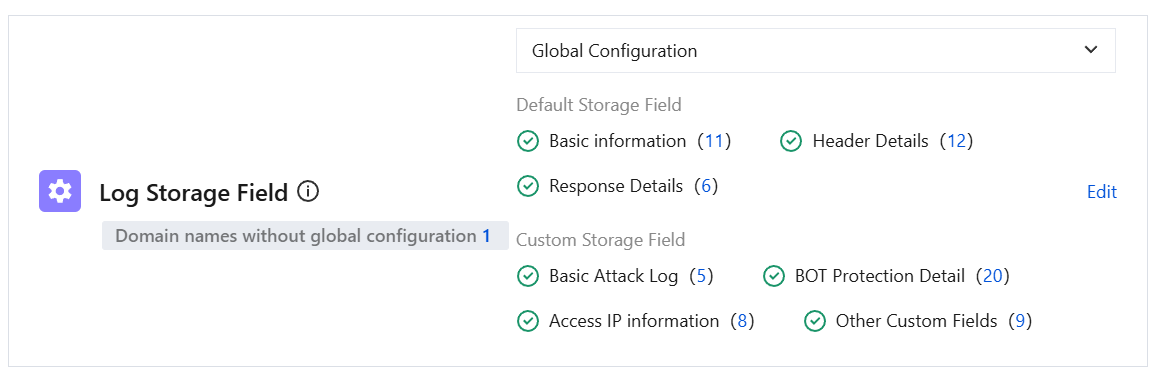
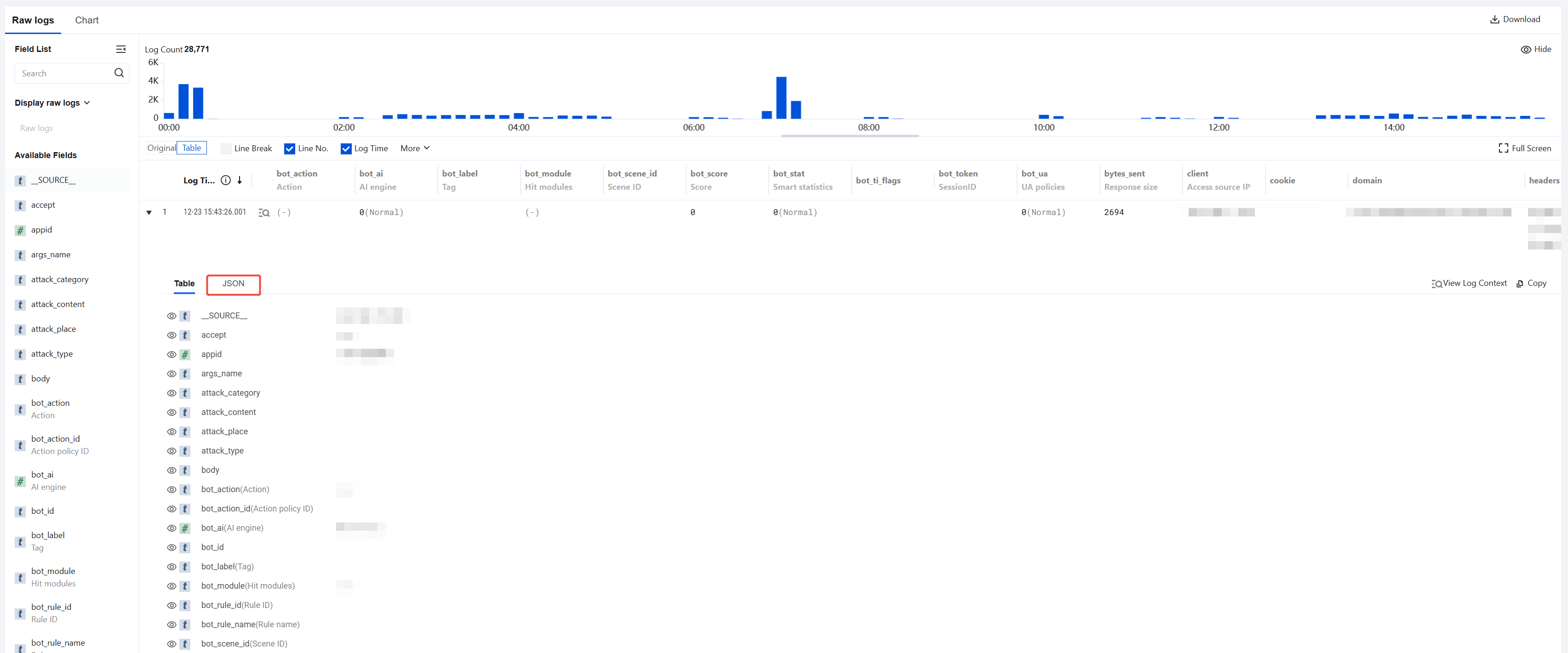
Information Type | Field Name | Description | Example |
Basic Information | domain | Domain name accessed by client requests. In cases of wildcard domain names or object-based access, the current domain name is the exact one. | clbwaf-example.qcloudwaf.com |
| request_time | Request latency: the time taken for a client request to reach the Web Application Firewall (WAF) and return from the WAF. Unit: seconds. | 0.003 |
| client | IP address of the access source: the source IP address of client requests. | 1.1.1.1 |
| uuid | Request UUID: the unique identifier for HTTP requests. | 2325eec3f71112f07263bd594440e7a9-20f1db72af339bd9587110a22ec2b913 |
| schema | Request protocol: HTTP or HTTPS. | http |
| method | Method for client requests. | GET |
| instance | WAF Instance ID | waf_examplename |
| query | Query String of the client HTTP request, maximum length is 1K Byte. | content=article&post_id=123 |
| time | The time when the client HTTP request was recorded by NGINX, expressed in a locally readable time format. | 23/Jun/2025:11:58:22 +0800 |
| timestamp | Timestamp in ISO 8601 format for when the client HTTP request occurred. | 2025-06-23T11:58:22+08:00 |
| appid | APPID of the user's Tencent Cloud account. | 1234567891 |
Header details | url | Client HTTP request header field, which records the content between the first "/" after the domain name and "?" in the complete request path. | /products/item123 |
| accept | Client HTTP request header field, used to inform the server of the response content types supported by the client. | text/html |
| encoding | Client HTTP request header field, used to inform the server of the compression algorithms supported by the client. | gzip |
| language | Client HTTP request header field, used to inform the server of the languages supported by the client. | en-US |
| connection | Client HTTP request header field that controls connection behavior, such as keep-alive, disable connection, and so on. | close |
| content_type | Client HTTP request header field that specifies the MIME type of the request body. | application/x-www-form-urlencoded |
| cookie | Client HTTP request header field that records the Cookie information of the request, maximum length is 1K. Unit: Byte. | k1=v1;k2=v2 |
| host | Client HTTP request header field that records the requested domain name. | 1.1.1.1:80 |
| referer | Client HTTP request header field that records the source URL information of the request. If the request has no source URL information, this field displays -. | http://example.com |
| x_forwarded_for | Client HTTP request header field that records all proxy IP addresses passed through by the client request and the client's real IP address. | XX.XX.XX.XX |
| user_agent | Client HTTP request header field that records the client's software and operating system information. | Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/49.0.2623.112 Safari/537.36 |
| request_length | Size of the client HTTP request. Unit: Byte. | 435 |
Response Details | upstream_status | Response status code returned from the origin server to the Web Application Firewall. | 0 |
| user_agent | SaaS-based Web Application Firewall response status code returned to the client: 200: Normal request 202: Front-end defense 302: Redirect 403: Intercept 4XX: Refer to the standard definitions of HTTP response status codes. 5XX: Refer to the standard definitions of HTT P response status codes. CLB-based Web Application Firewall response status code returned to the load balancer: 600: Normal request 624: Front-end defense 621: Redirect 615: Intercept | 600 |
| bytes_sent | Response body size. Unit: Byte. | 112 |
| upstream_connect_time | Connection time from Web Application Firewall (WAF) to the origin server for client requests. Unit: second. | 0.033 |
| upstream_response_time | Time taken for the client request to return from the origin server to the Web Application Firewall (WAF). Unit: s. | 0.033 |
| upstream | IP address of the origin server. | 1.1.1.1 |
Basic Attack Logs | attack_type | Attack Type: specific attack type triggered | XSS Attacks |
| sec_action | Action taken: the mitigation action triggered by client attacks, including four types of handling results: Observe (0), Block (1), CAPTCHA verification (2), Redirect (3). | 1 |
| rule_id | Rule ID: ID of the rule that triggered the protection policy | 10000244 |
| risk_level | Risk Level: risk level triggered by client attacks, including three risk levels: High-risk (1), Medium-risk (2), Low-risk (3). | 1 |
| sec_chain | Security modules through which the request passed and the corresponding actions taken. | {"acl":{"ac":6},"areaban":{"ac":6},"bw_list":{"ac":12},"web_sec":{"id":10000244,"ac":1},"whitelist":{"ac":6}} |
BOT Protection Details | bot_module | BOT detection module hit by current access request. | Module Name/Chinese-English Processing |
| bot_action | BOT action taken for the current access request. | intercept |
| bot_score | information about the BOT score of the current access request. | 20 |
| bot_label | BOT Tag hit by current access request. | Malicious bot |
| ua_type | User-Agent type of the accessing user in the current request. | bot |
| ua_crawlername | Name of the User-Agent suspected to be a crawler in the current access request. | CensysInspect/1.1 |
| ua_fake | Whether the User-Agent in the current access request is forged, 0 for no, 1 for yes. | 0 |
| ua_goodbot | Whether the BOT in the current access request is goodbot, 0 for no, 1 for yes. | 0 |
| bot_ai | Whether the current access request is flagged as abnormal by the AI engine, 0 for normal, 1 for abnormal. | 0 |
| bot_stat | Whether the current access request is identified as abnormal by intelligent statistics, 0 for normal, 1 for abnormal. | 0 |
| bot_ti_tags | Whether the current access request matches threat intelligence, displaying the matched intelligence Tag. | "WEB Exploit","Bot","FTP Scan" |
| bot_id | BOT ID of the current access request. | |
| bot_scene_id | ID of the BOT scenario hit by the current access request. | 3100806770 |
| bot_action_id | ID of the BOT action policy hit by the current access request. | |
| bot_rule_id | ID of the BOT rule hit by the current access request. | 3300002268 |
| bot_rule_name | Name of the BOT rule hit by the current access request. | Censys |
| bot_token | ID of the BOT session for the current access request. | |
| bot_tld_risk_tag | Endpoint risk Tag status for the current access request (requires purchase of RCE TDS capability). | |
| bot_ua | Whether the current access request hit the ua policy. | 0 |
Access IP address information | ipinfo_nation | Country of origin of the IP address used for access. | China |
| ipinfo_state | Country of origin of the IP address used for access, in ISO country code format. | CN |
| ipinfo_city | City of origin for the IP address used for access. | Guangzhou |
| ipinfo_province | Province of origin for the IP address used for access. | Guangdong |
| ipinfo_isp | ISP for the IP address used for access. | chinaunicom.com |
| ipinfo_detail | Details of the IP address used for access. | - |
| ipinfo_longitude | Longitude information associated with the IP address used for access. | 113.65302 |
| ipinfo_dimensionality | Latitude information associated with the IP address used for access. | 34.7625 |
Other custom fields | headers | Protocol header information: including custom header information. | waf-customize-lbid: lb-exmple accept: */* stgw-orgreq: GET / HTTP/1.1 x-waf-uuid: 03043817b707b17ba519d478944e0634-e88bfddc17eb7a9193a92db7b0c00000 stgw-orgcontentlength: 0 content-length: 0 stgw-orgservername: clbwaf-shjr.qcloudwaf.com stgw_request_id: 78b504122b27657f7355af12dbd00000 connection: close |
| body | Request content: Request Body | |
| attack_category | Attack Primary Classification / Protection Module | WEB Generic Attack |
| attack_content | Attack content: the content that triggered the attack from the client side. | {"action":3,"type":1,"field":"alert("m3nsHen_Va1idation")","mc":"XSS attack","offset":0,"sc":"XSS attack","level":5,"target":"Parameter","match":"alert("m3nsHen_Va1idation")","data":"alert("m3nsHen_Va1idation")","sid":"010000244"} |
| attack_place | Attack location: the position of the attack vector within the HTTP request. | Parameter |
| count | Number of attacks: the number of attacks aggregated every 10 seconds from the same attacker IP address and attack type. | 1 |
| waf_verify | Captcha verified token | success |
| pan | Access domain name or clb object | lb-example, wildcard domain |
| http_log | Log files that record HTTP request and response information | {"REQUEST_METHOD":"GET","PROCOTOL":"HTTP/1.1","REQUEST_ARG_RAW":"{"1750650000.4178421":true,"alert("m3nsHen_Va1idation")":true}"} |
| args_name | Attack hit log parameter name: parameter name in the HTTP request | Parameter |
name of the module field | Module type |
web_sec | Web Basic Security |
cc | CC Protection |
areaban | Access Control - Region Blocking |
whitelist | Custom Allow Rule |
bw_list | IP Blocklist/Allowlist |
acl | Access Control |
bot | Bot Management |
ip_punish | Web Basic Security - IP Blocking |
business_risk | Business Security |
ai | AI Engine |
captcha | Captcha service. |
api_sec | API Security |
Action Code | Action Description |
0 | Bypass |
1 | Deny |
2 | CAPTCHA |
3 | Redirect |
4 | Log |
5 | No_Action |
6 | Empty_Rules |
7 | Allow |
9 | Return |
10 | Reload |
11 | Error |
12 | Miss |
13 | JSChallenge |
14 | Delay |
15 | AUTO_CAPTCHA_LOG |
16 | AUTO_CAPTCHA_DENY |
20 | Action Unknown |
Apakah halaman ini membantu?
Anda juga dapat Menghubungi Penjualan atau Mengirimkan Tiket untuk meminta bantuan.
masukan