



Frequently
Asked Questions
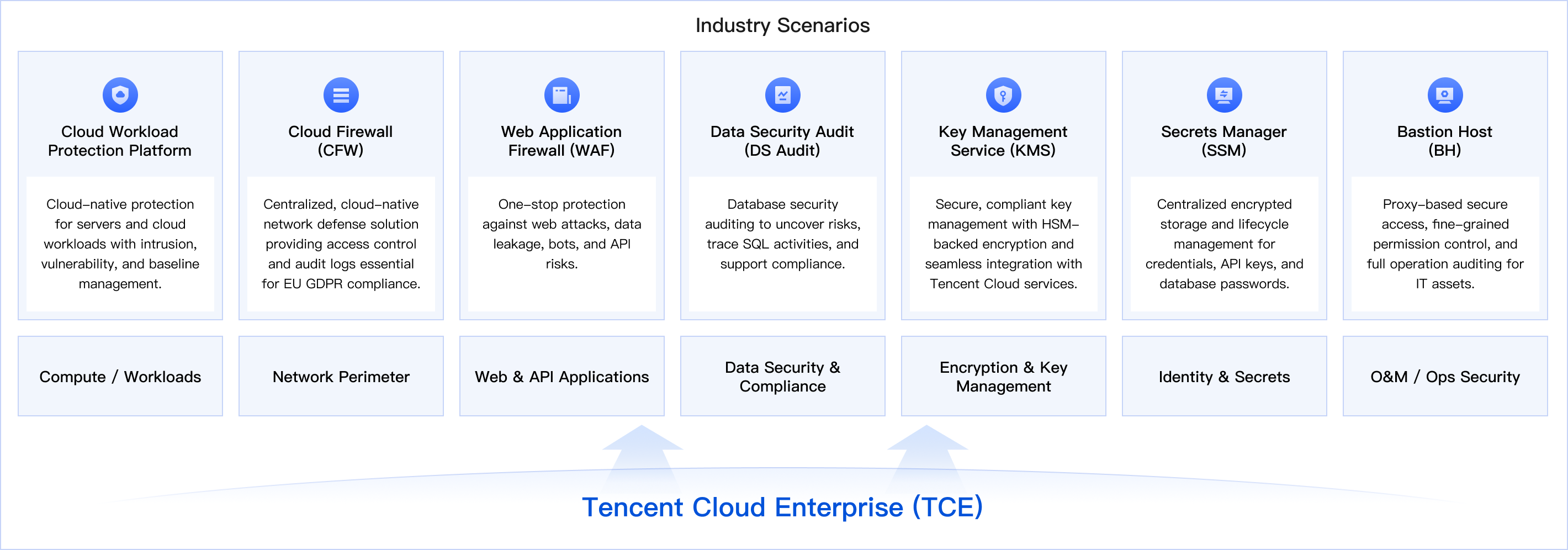
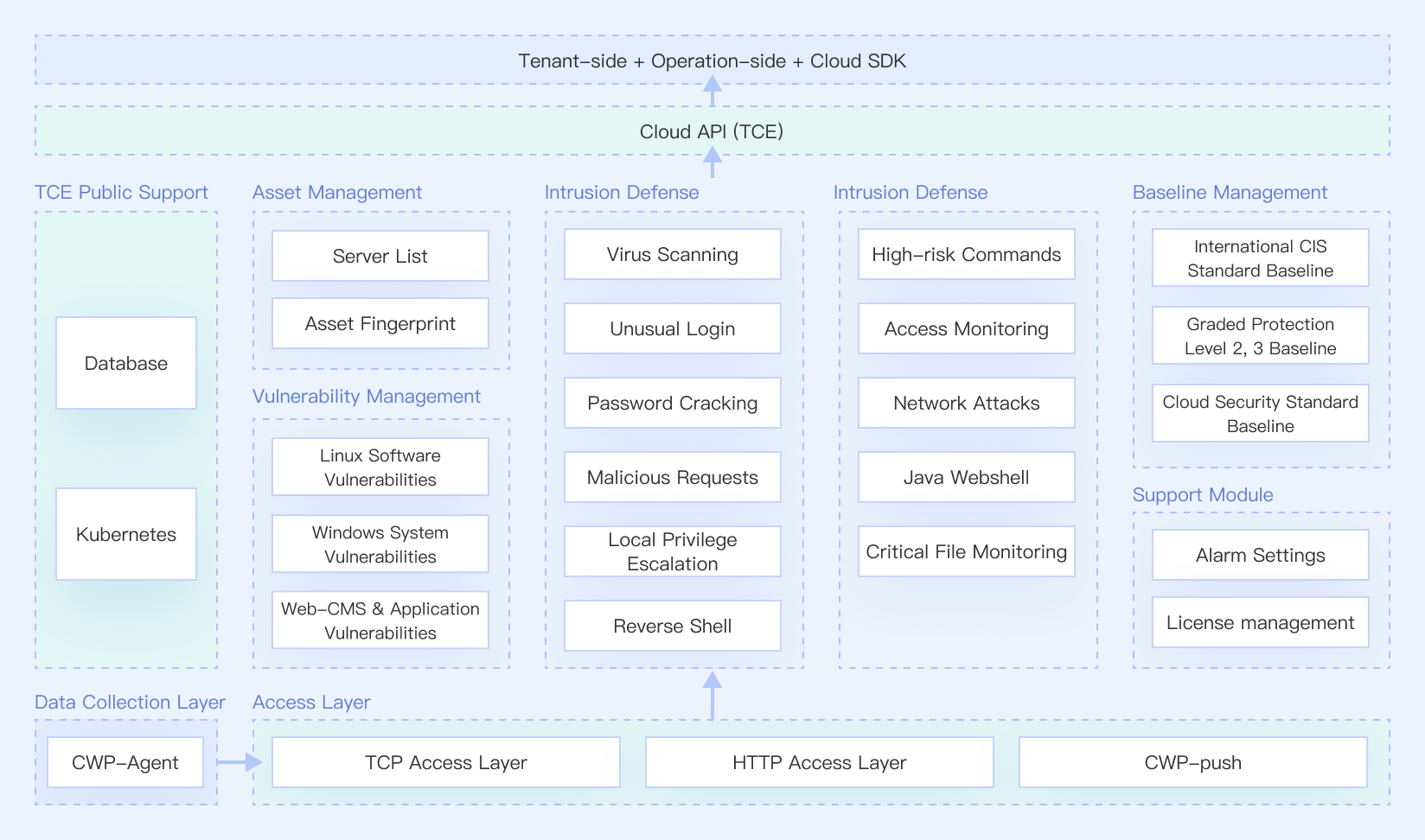
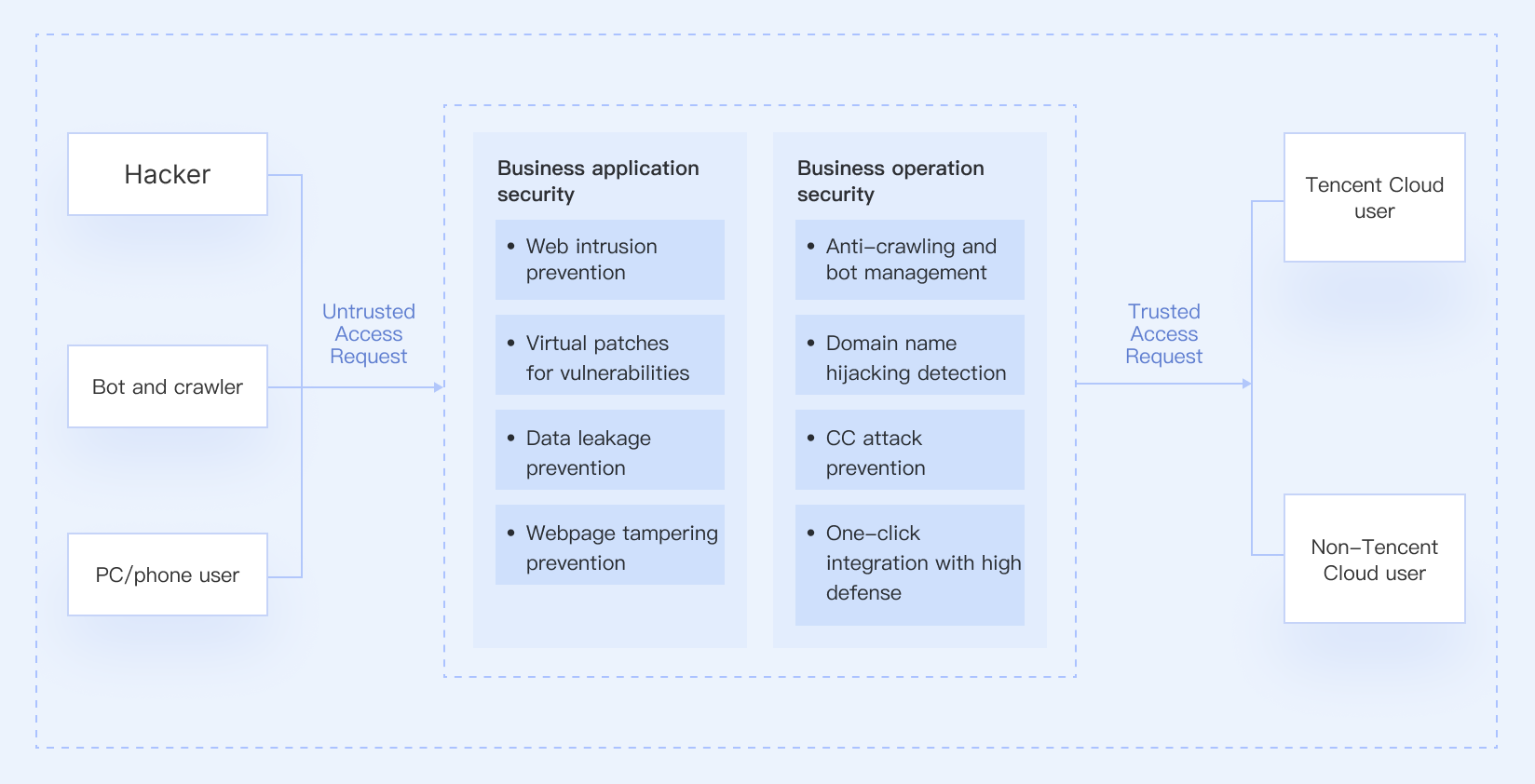
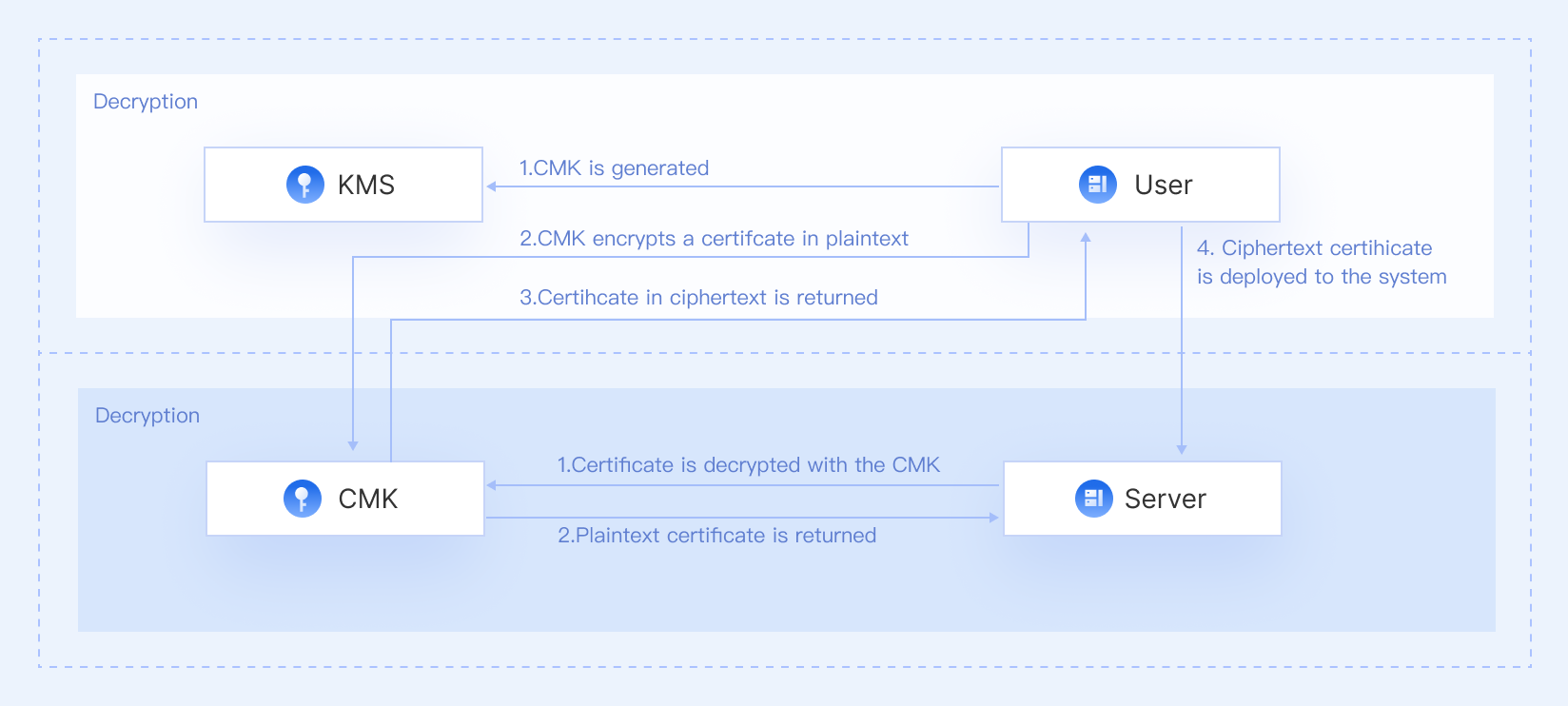
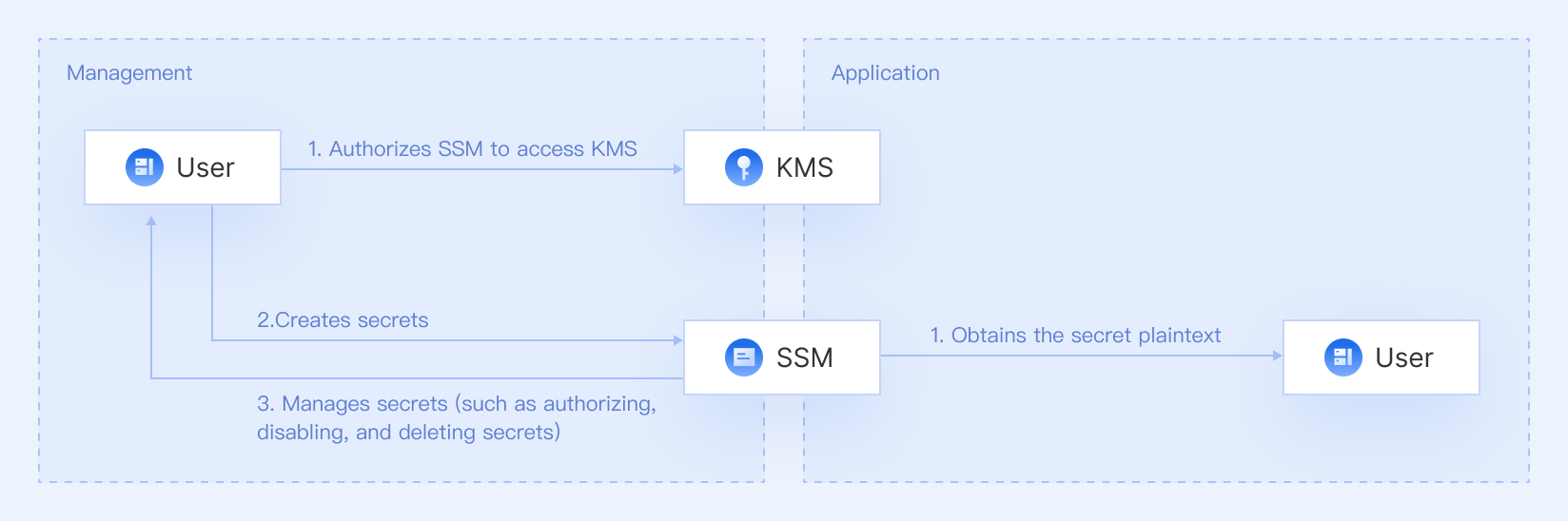
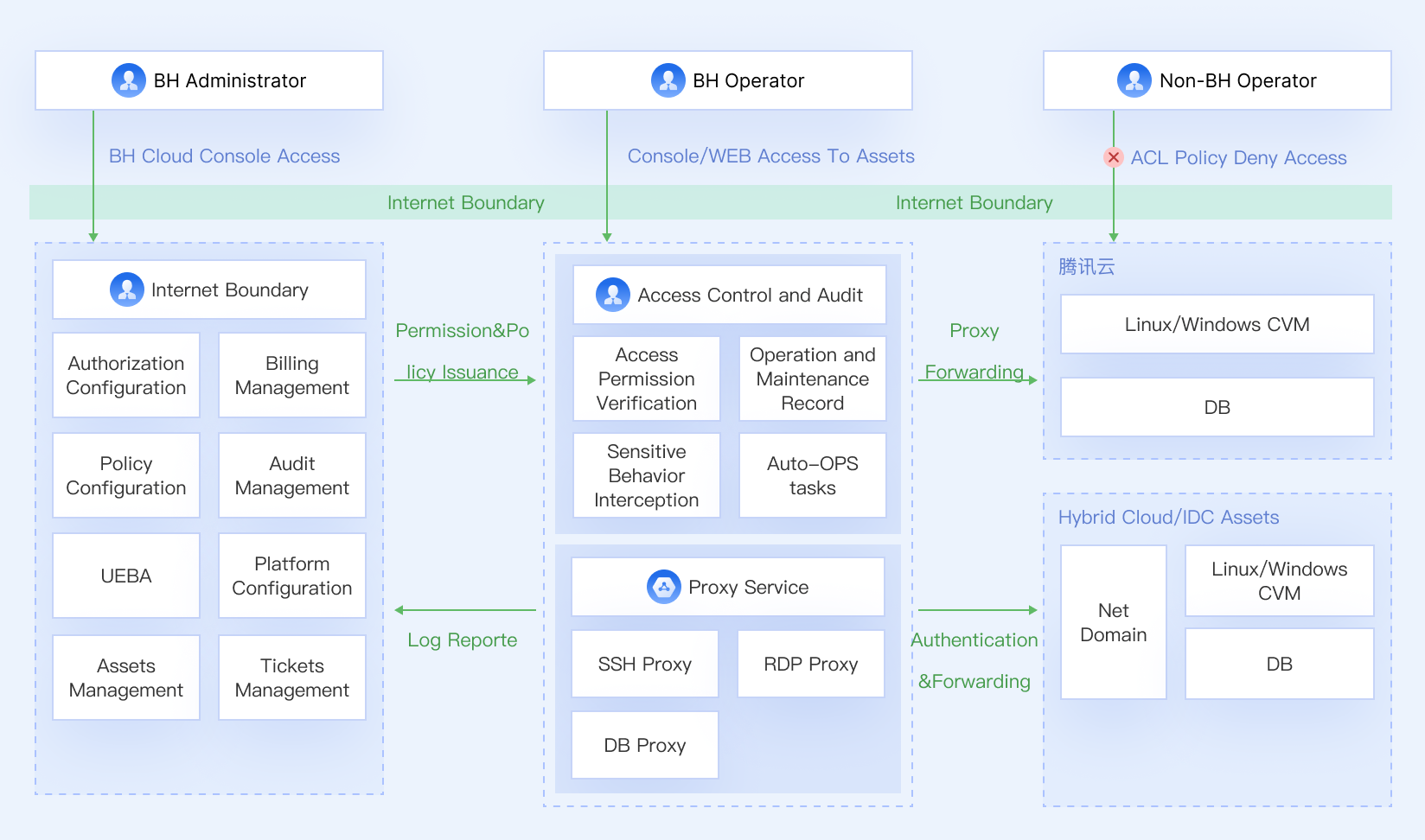
The TCE Security Suite includes seven cloud-native products: Cloud Workload Protection, Cloud Firewall, Web Application Firewall, Data Security Audit, Key Management Service, Secrets Manager, and Bastion Host. Together, they cover compute, network, application, data, and O&M security.
Yes. You can deploy any product individually for specific use cases, or use multiple products together as an integrated security stack.
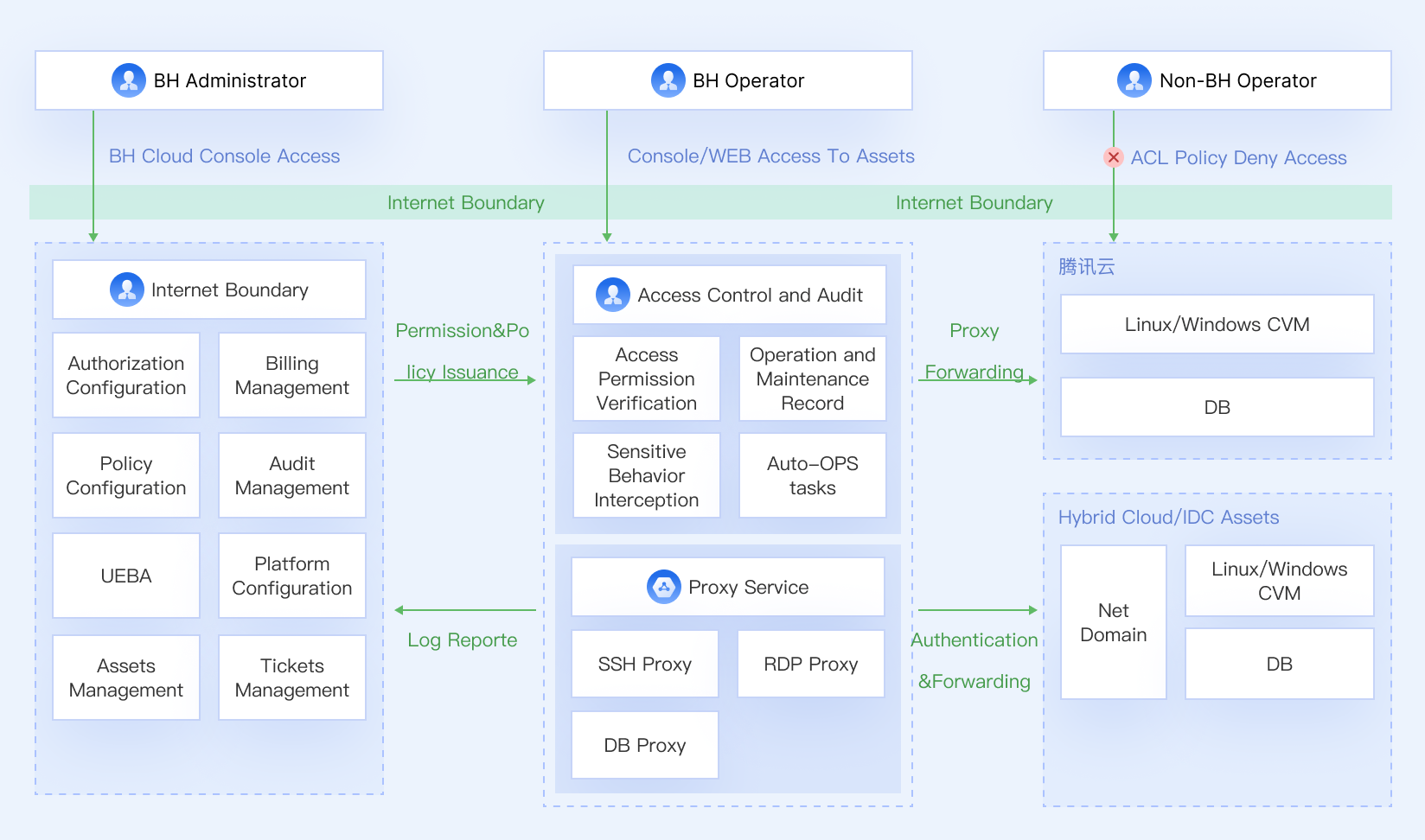
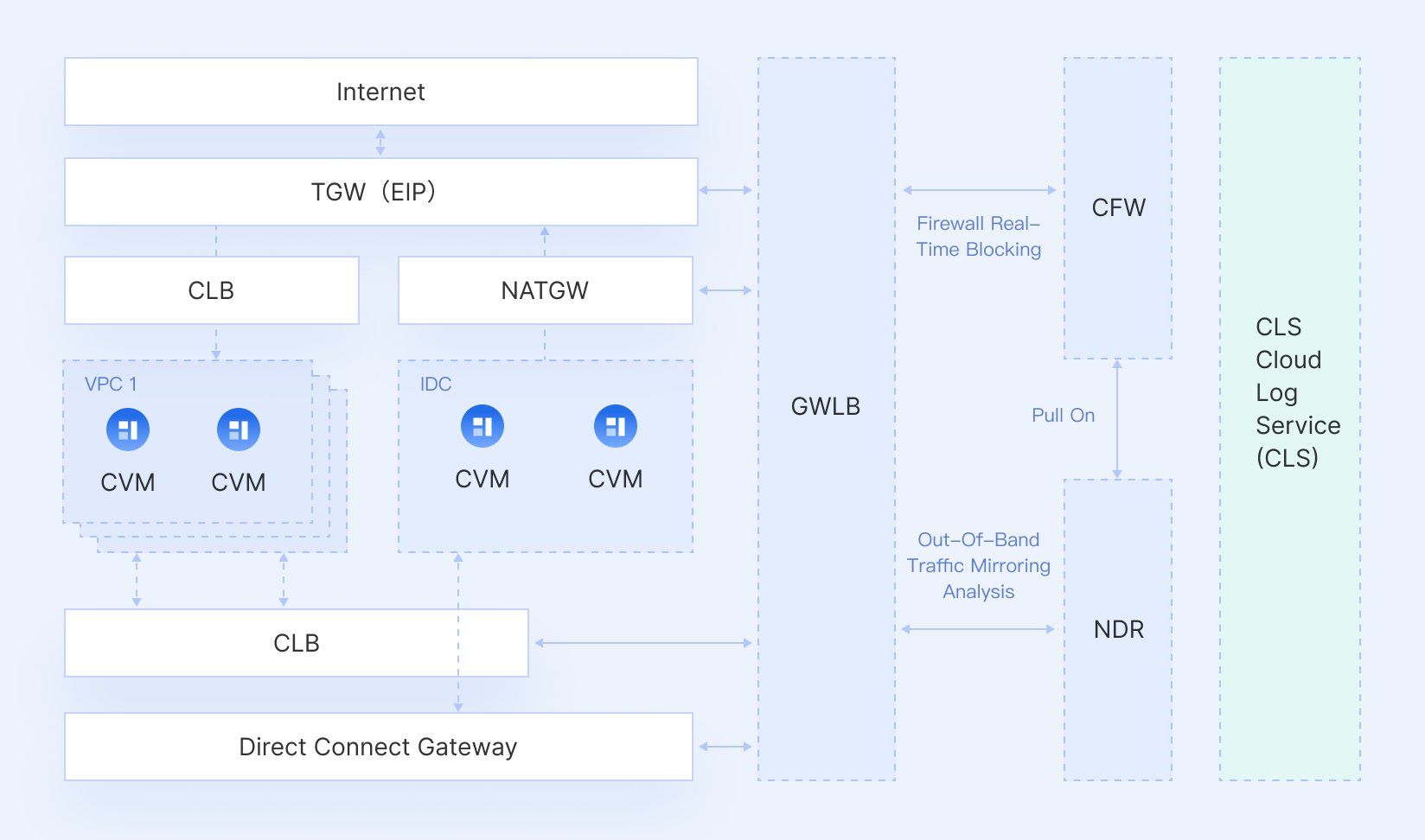
Many products support hybrid and multi-cloud environments, such as protecting on-premises servers or self-built databases. Please refer to each product’s documentation for detailed environment support.
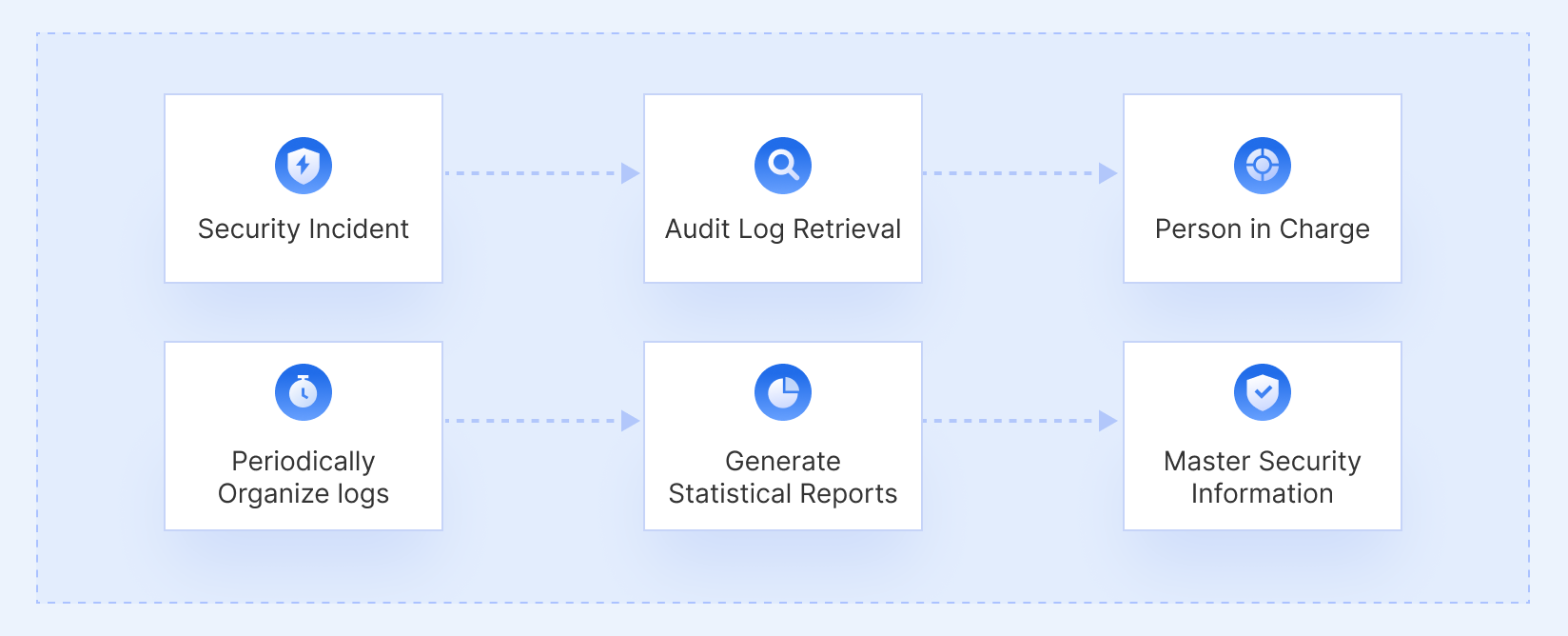
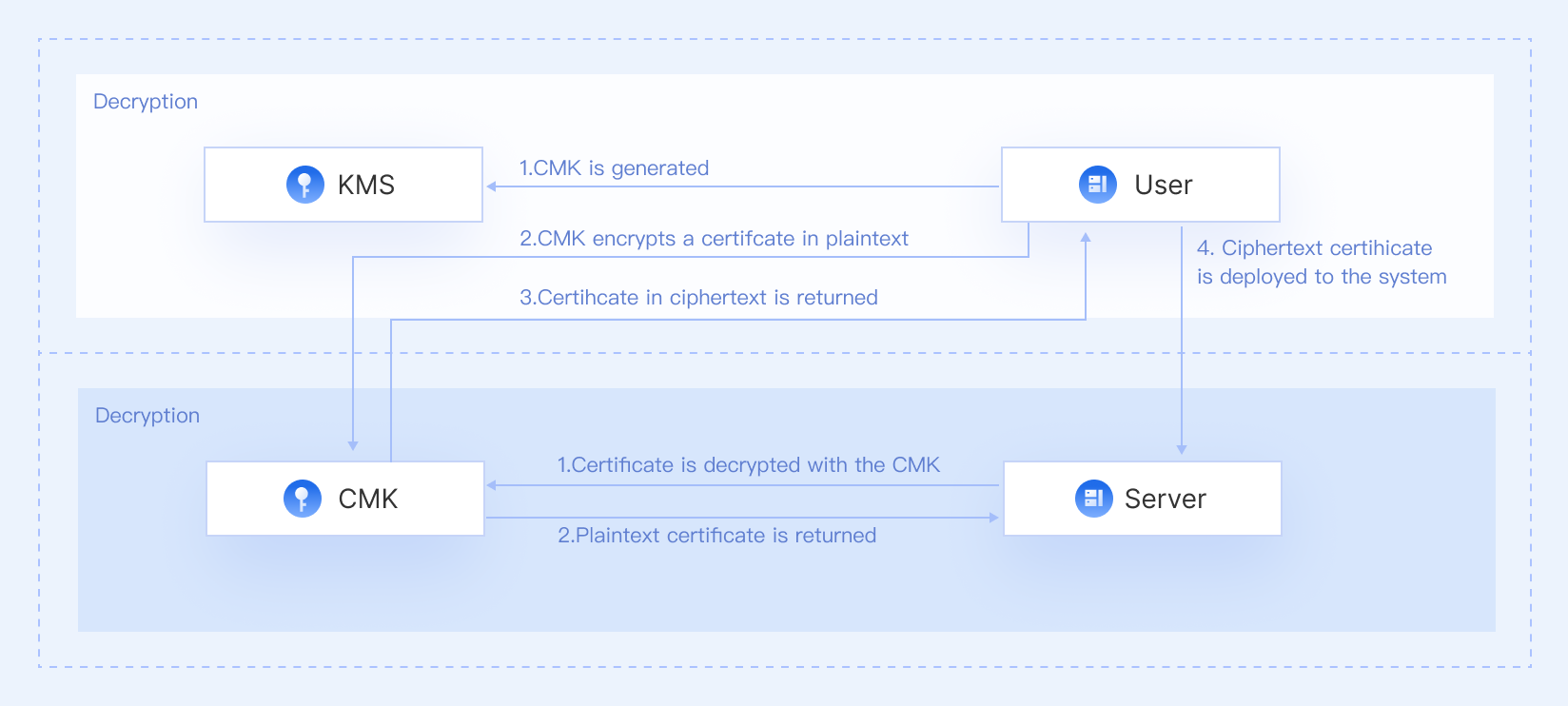
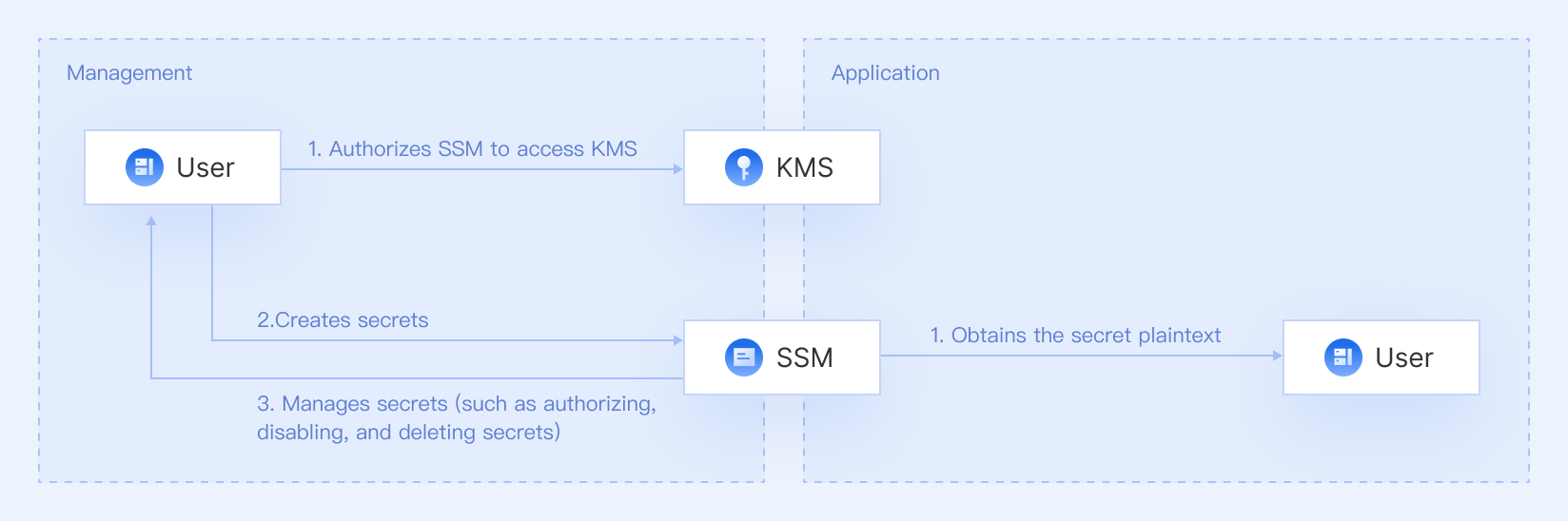
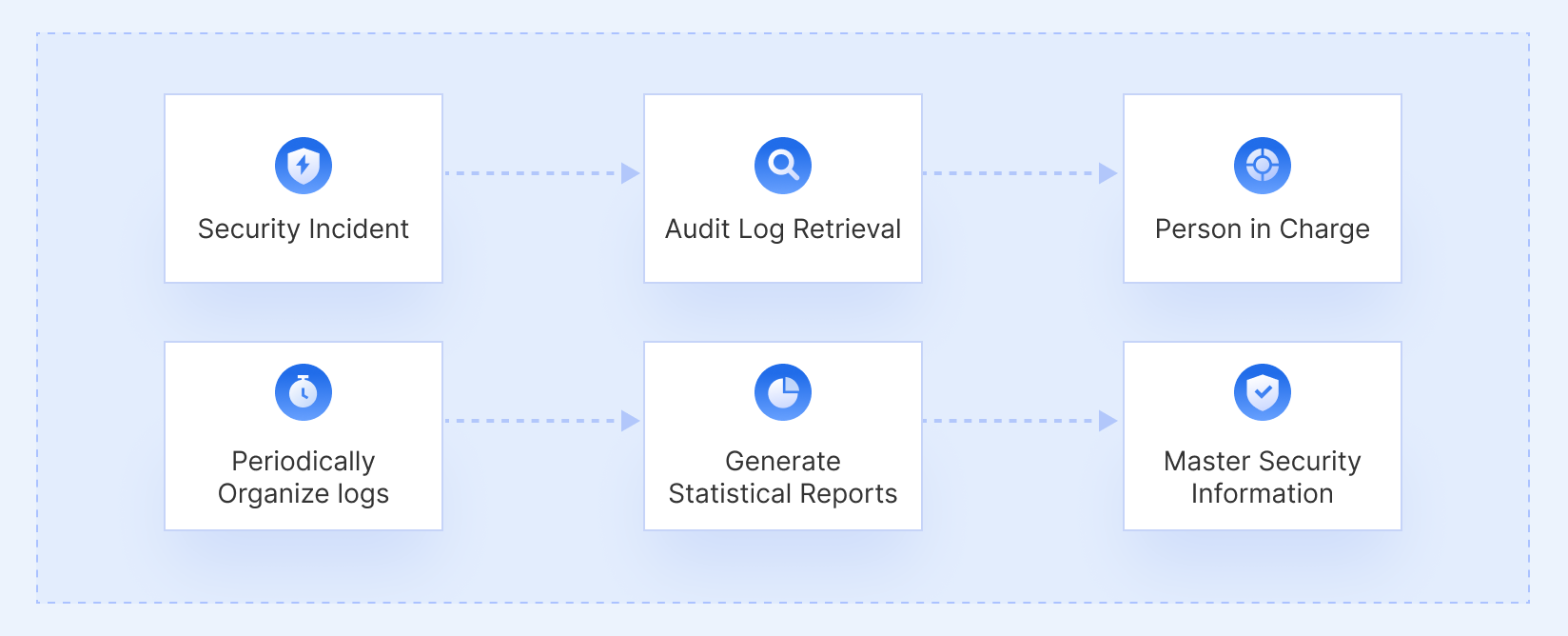
The suite provides capabilities such as database auditing, key management, encrypted secret storage, traffic logging, and O&M operation auditing, which can help you meet industry standards and internal compliance requirements.
You can enable most products directly from the Tencent Cloud console or purchase them via the product pages. For tailored architecture design or large-scale deployments, you can contact Tencent Cloud sales for guidance.
Frequently
Asked Questions
The TCE Security Suite includes seven cloud-native products: Cloud Workload Protection, Cloud Firewall, Web Application Firewall, Data Security Audit, Key Management Service, Secrets Manager, and Bastion Host. Together, they cover compute, network, application, data, and O&M security.
Yes. You can deploy any product individually for specific use cases, or use multiple products together as an integrated security stack.
Many products support hybrid and multi-cloud environments, such as protecting on-premises servers or self-built databases. Please refer to each product’s documentation for detailed environment support.
The suite provides capabilities such as database auditing, key management, encrypted secret storage, traffic logging, and O&M operation auditing, which can help you meet industry standards and internal compliance requirements.
You can enable most products directly from the Tencent Cloud console or purchase them via the product pages. For tailored architecture design or large-scale deployments, you can contact Tencent Cloud sales for guidance.


