Authorizing Policies for Sub-Accounts or Cross-Cloud Accounts
Download
포커스 모드
폰트 크기
Sub-account permission segmentation between the Tencent Cloud accounts (root accounts) and sub-accounts, and authorizing different permissions to sub-accounts as needed, can avoid security risks resulting from the exposure of Tencent Cloud account keys.
Authorizing a Permission Policy for a Sub-Account
Background
Company A has enabled the TencentDB for CTSDB 3.0 service and needs its own team members to operate the cloud resources involved in the CTSDB 3.0 service. For security or trust considerations, Company A does not want to directly disclose the cloud account key to team members, but hopes to create corresponding sub-accounts for them. Sub-accounts can only operate cloud resources with root account authorization, and no need for independent metering and billing for sub-accounts. All expenses are accounted under the company's Tencent Cloud account, and sub-account operation permissions can be revoked or deleted at any time.
Directions
Step 1: Creating a Sub-Account User
You can create through the console or API interface.
Log in to Cloud Access Management (CAM) console of Tencent Cloud, and then enter the User List page to create. For detailed operation, see Creating Sub-Users.
Add sub-users and set permissions by accessing the key call AddUser interface. For details, see Adding Sub-Users.
Step 2 (Optional): Creating a Custom Permission Policy
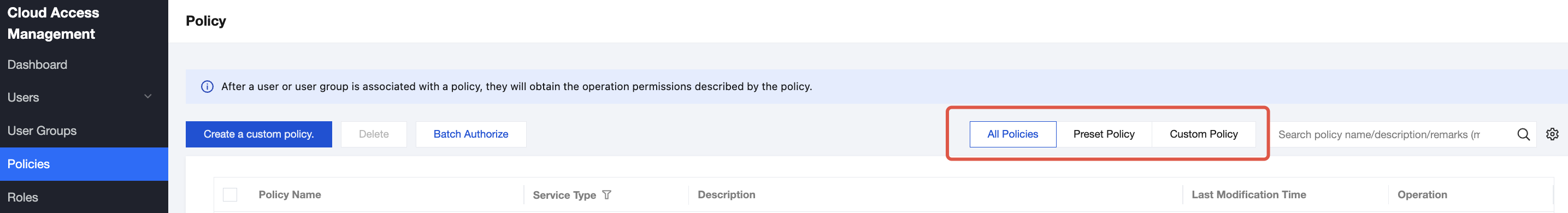
1. Search for policy in the search box in the upper right corner on the Policies page in the CAM console. Preset policies are system default policies, and custom policies are defined by users based on business requirements. Search for policies based on actual conditions.
2. If the policy does not exist, you need to create custom policies. For specific operations, see Creating Custom Policies.
Step 3: Authorizing Permission Policies to Sub-Account Users
Find the permission policy to be associated in the Policies page of the CAM console, and associate it with the sub-account user. For detailed operations, see Authorization Management.
Find the sub-account user to be authorized in the User List page of the CAM console, and associate it with the policy. For detailed operations, see Authorization Management.
Step 4: Logging in to the Tencent Cloud Console via Sub-Accounts
Use a sub-account to log in to the Tencent Cloud console and access CTSDB 3.0. For detailed operations, see Logging in to the Console with the Sub-Account.
If you need to view and modify the user information of a sub-account, see Users Information.
If you want to revoke or delete sub-account operation permissions, see Deleting Sub-Users.
Authorizing a Permission Policy for a Cross-Cloud Account
Background
Company A has enabled the TencentDB for CTSDB 3.0 service and hopes that Company B can have partial business permissions for its CTSDB 3.0. For example, instance read and write permissions, database management, and more. Company B hopes to have a sub-account responsible for this part of the business. Company A can authorize Company B's sub-account to access the resources of CTSDB 3.0 through role access. For the specific concept and application scenarios of roles, see Role Overview.
Directions
Step 1: Company A Creating a Role for Company B
1. Log in to Tencent Cloud CAM console and enter the Role page.
2. Click Create Role, and in the Select a role carrier dialog box, select Tencent Cloud account.
3. On the configuration wizard page of Create a Custom Role, create a role.
a. On the Enter role carrier information page, select Cloud account type as Another root account, input the root account of Company B in Account ID, set other parameters according to the prompts, and click Next.
b. On the Configure role policy page, select the policies that need to be authorized for the role, and click Next.
c. In the Role Name input box on the Review page, set the role name, such as DevOpsRole. Review the selected policies, and click Completed.
Step 2: Company B Authorizing the Permission of Role Assumption to the Sub-Account
1. Log in to Tencent Cloud CAM console with the root account of Company B, and then enter the User List page to create a sub-account. For detailed operations, see Creating Sub-Users.
2. On the Policies page of the CAM console, click Create a custom policy.
3. In the dialog box of Select a policy creation method, select Create according to the policy syntax.
4. In the configuration wizard of Create according to the policy syntax, create a policy.
a. In the Select a policy template area, select Blank Template and click Next.
b. On the Edit Policy page, set the policy name in the Policy Name input box, such as sts:AssumeRole.
c. In Policy Content, assign permissions for the sub-account to assume roles according to the policy syntax and click Completed. The example is as follows:
{"version": "2.0","statement": [{"effect": "allow","action": ["name/sts:AssumeRole"],"resource": ["qcs::cam::uin/12345:RoleName/DevOpsRole"]}]}
5. Back to the Policies page, find the created custom policy, and click Associate User/Group/Role in Operation column.
Associate the custom policy with the sub-account of Company B and click OK.
Step 3: Company B Using the Sub-Account to Access Cloud Resources Through the Role
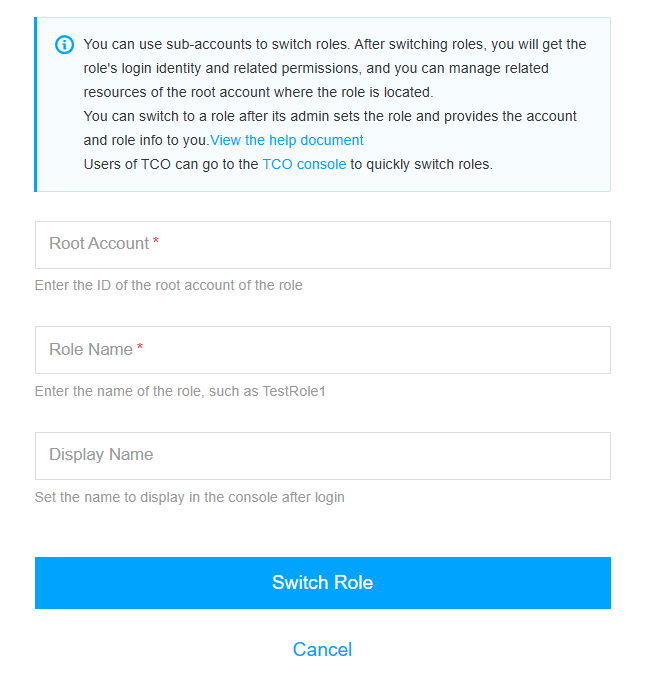
1. Log in to the console with the sub-account of Company B. In the profile photo pull-down menu in the console, select Switch role.
2. On the Switch Role page, enter the root account of Company B and role name. Click Switch Role to switch to the role identity of Company A.
More References
If you need to modify a role, see Modifying Roles.
If you need to delete a role, see Deleting Roles.
피드백