Step 4: Configuring a Client Certificate
A client certificate is a digital certificate issued by a CA certificate to a client device. When a connection is established with the server, the server performs security verification on the client's identity based on the client certificate. After successful verification, both parties can achieve secure communication using the built-in encryption key in the certificate. If verification fails, the server will reject the client's connection request.
Restrictions and Limitations
The maximum number of client certificate signups per second is 15, and any requests exceeding this limit will be rejected.
Prerequisites
Registering a CA certificate
Client certificates support two registration methods: manual registration and automatic registration. The registration method is specified when One-device-one-certificate is enabled. For specific steps, see Enabling One-device-one-certificate.
Automatic Client Certificate Registration
If automatic client registration is selected, when the client connects to the server, the server will check whether the CA certificate associated with the client certificate has been registered. If the corresponding CA certificate is not registered, authentication fails and the client connection will be rejected.
If the corresponding CA certificate is registered, authentication succeeds, and the client certificate will be automatically registered and appear on the Client Certificate Management page.
Manual Client Certificate Registration
Step 1: Use a CA certificate to generate a client certificate
If you use a self-signed CA certificate to generate a client certificate, you can follow the instructions below.
1. Create a configuration file named
client.conf. Modify the file content according to actual needs.[v3_req]basicConstraints = critical, CA:FALSEkeyUsage = critical, digitalSignatureextendedKeyUsage = clientAuth
2. Generate a client certificate
client.crt.openssl ecparam -genkey -name prime256v1 -out client.keyopenssl req -new -key client.key -out client.csr -subj "/C=CN/ST=ZheJiang/L=HangZhou/O=IoV/CN=SN0001"openssl x509 -req -in client.csr -CA CA.crt -CAkey CA.key -CAcreateserial -out client.crt -days 365 -sha256 -extfile client.conf -extensions v3_req
openssl genrsa -out client.key 4096openssl req -new -key client.key -out client.csr -subj "/C=CN/ST=ZheJiang/L=HangZhou/O=IoV/CN=SN0001"openssl x509 -req -in client.csr -CA CA.crt -CAkey CA.key -CAcreateserial -out client.crt -days 365 -sha256 -extfile client.conf -extensions v3_req
Step 2: Register the client certificate
1. Log in to the MQTT console.
2. In the left sidebar, click Resource > Cluster. Select a region, and click the ID of the cluster for which you want to configure a certificate, to go to the basic information page of the cluster.
3. Go to the Client Certificate page, and click Register Client Certificate. Fill in the client certificate information in the following pop-up window:
Source: Manual registration.
CA Certificate: Select a registered CA certificate.
Client Certificate: Upload the issued client certificate according to the file format requirements.
Client ID: A supplementary field in the "one-device-one-certificate" scenario, which is optional. You can fill it according to your actual scenario. If the client id passed during client connection is empty, this field will be considered as the client id. If both the client id and this field are empty, the server will use the Common Name field of the client certificate. Therefore, if the client does not pass a client id, please ensure this field does not have duplicate values.
Whether to activate: Indicates the activation status of the client certificate after registration. It is enabled by default. You can also manually enable it in the console after registration.
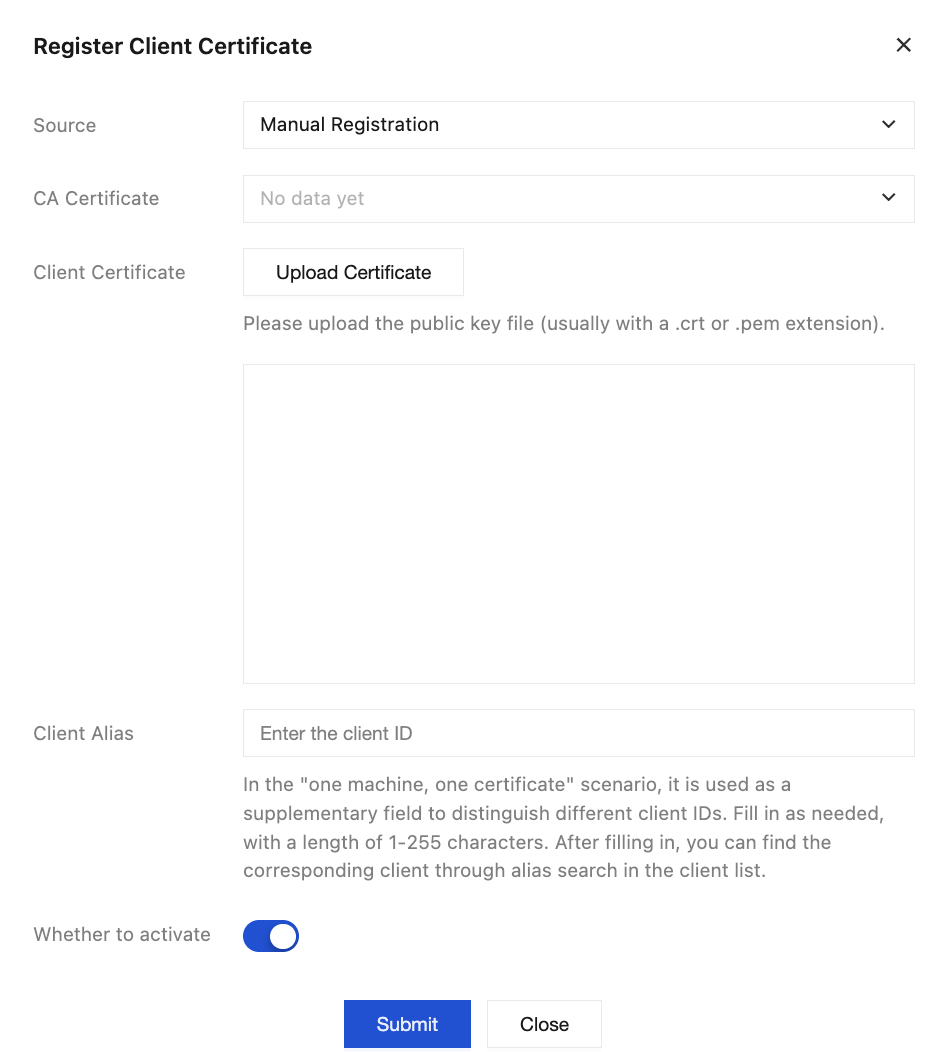
4. Click Submit to complete the client certificate registration.
Manage a Client Certificate
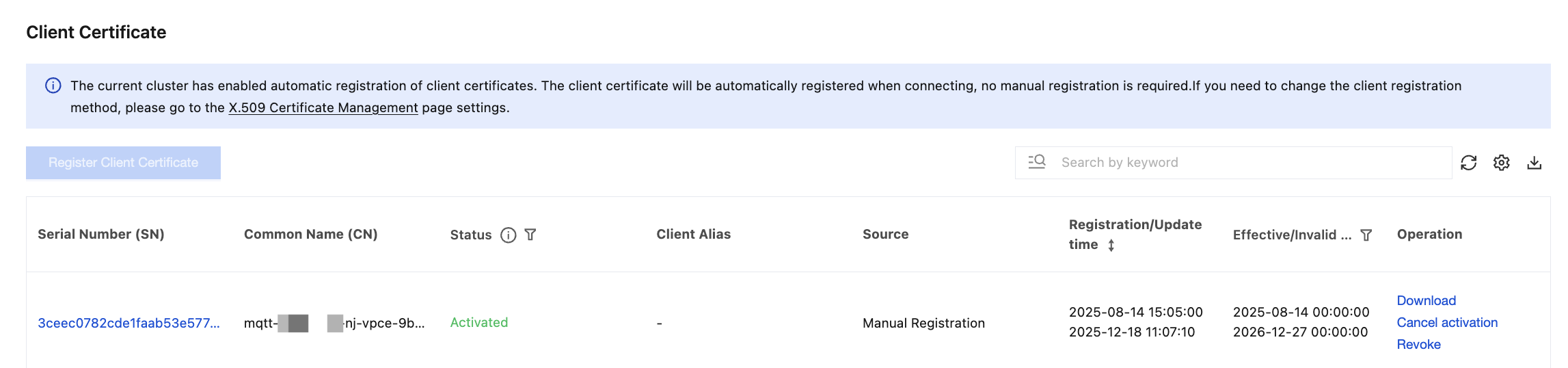
After the client certificate is registered, you can view the status of the registered certificate on the client certificate list page. Client certificates have four statuses: Activated, Not activated, Registered but not activated, and Revoked.
Operation | Operation Path | Description |
Filter by Effective/Expiration Time | Click the  | Filter expired certificates and expiring client certificates (expiring within 30 days). |
Deactivating a certificate | Click Deactivate in the operation bar. | After a certificate is deactivated, clients using that certificate will be rejected during connection. Therefore, special attention is required regarding the impact on client connections when the certificate status is changed. |
Deleting a Certificate | Click More > Delete in the operation bar. | Certificates in the "Activated" status cannot be deleted. Only certificates in the "Not activated" or "Revoked" status can be deleted. |
Revoking a Certificate | Click More > Revoke in the operation bar. | Once a client certificate is revoked, it cannot be reactivated. After the certificate status changes, there is a minute-level delay before the new status takes actual effect. |
View Certificate Details | Click Serial Number of the certificate. | On the certificate details page, the following information of the certificate is displayed: Basic Information: Displays Status, Common Name, Serial Number, and other details of the certificate. Associated Clients: Displays the list of clients associated with the current certificate. |
The search box on the client certificate list page supports filtering by multiple resource attributes and combinations of attributes, including: Certificate Serial Number (SN), Certificate Organizational Unit (OU), Certificate Common Name (CN), Certificate Status, and Effective/Expiration Time.
Help and Support
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback