Encrypted Traffic Detection
フォーカスモード
フォントサイズ
Overview
Network Detection and Response (NDR) has added encrypted traffic detection capability, supporting parsing and detecting encrypted traffic (such as HTTPS/TLS) for CVM assets, container assets, and the public network traffic of GAAP assets, comprehensively enhancing visibility of full traffic and threat detection capability. Users can learn from this chapter about the configuration and usage of this feature. This document uses CVM assets as an example to provide relevant operational instructions, and the same applies to other assets operations.
Note:
Currently in public beta version, only available to invited users. Non-invited users who wish to experience this feature can submit a ticket to apply for access.
Prerequisites
Users need to configure security group rules to authorize the probe to collect network traffic, meeting the data input requirements of Network Detection and Response.
Method 1: Configuration of the Enterprise Security Group
1. Log in to the Cloud Firewall console, choose Access Control > Enterprise Security Group (New).
2. On the Enterprise Security Group page, click Add Rule, and enter the rule information as required in the table.
Configuration Item | Set Value |
Access source IP address | 0.0.0.0/0 |
Access destination IP address | 9.9.9.199 |
Destination port | 47891,47892,47893 |
Protocol | UDP |
Policy | Allow |
Description | NDR allow rule |
3. Click Save, and the rule will be deployed to associated instances.
Method 2: Configuration of the Single Instance
1. Log in to the CVM console, and select Instances.
2. On the instance page, click the instance name that requires detection of encrypted traffic to be enabled.
3. On the instance details page, select Security Group, and click the Security Group ID/Name of the bound security group.
4. Click Add Rule, and fill in the rule information according to the requirements in the table.
Configuration Item | Set Value |
Type | Custom |
Target | 9.9.9.199 |
Protocol Port | UDP: 47891,47892,47893 |
Policy | Allow |
Remark | NDR allow rule |
5. Click OK, and the rule will be deployed to associated instances.
Specification Description
Note:
CVM assets and container assets specifications primarily refer to host and cluster resources; GAAP assets specifications refer to the performance metrics of their acceleration instances.
Specifications include the applicable scope and capabilities of encrypted traffic detection, as well as resource consumption.
1. Log in to the CFW console, in the left sidebar, click Network Detection and Response.
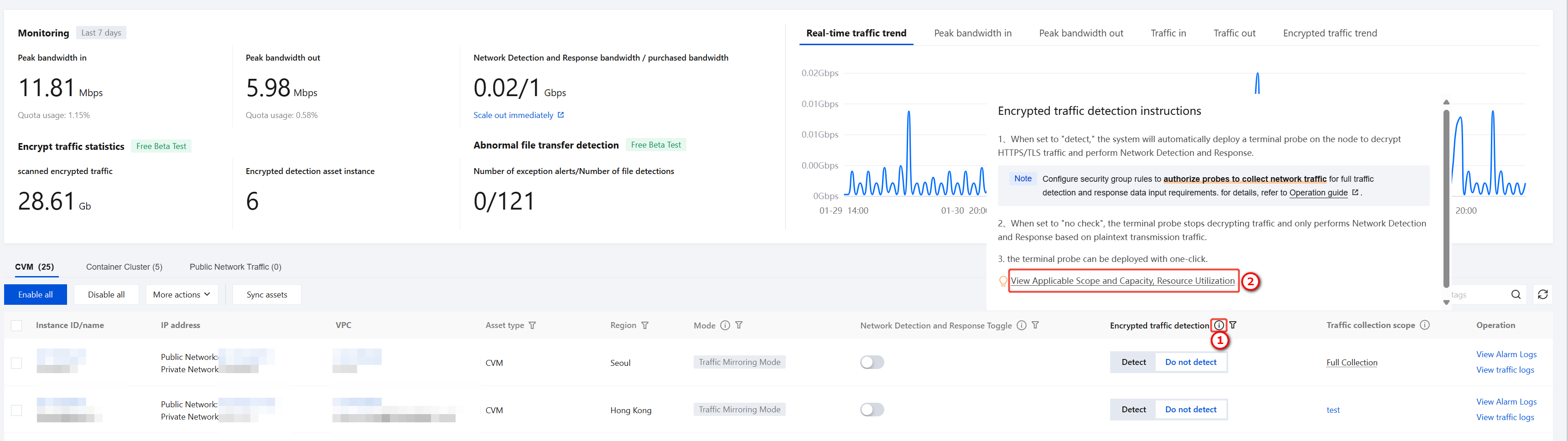
2. You can click View Applicable Scope and Capacity, Resource Utilizati to view detailed applicable scope and capabilities, resource consumption in the side panel.
Kernel Version Compatibility
Linux kernel version | Applicable | Not applicable |
Below 4.18 | Curl command Python version 3.8.15 and above | OpenSSL dynamic library Java program Golang program |
Greater than or equal to 4.18 | OpenSSL dynamic library Curl command Python version 3.8.15 and above GnuTLS dynamic library | Java program Golang program |
Specific Decryption Capability
Protocol compatibility: HTTPS, SMTPS, FTPS.
Algorithm support: TLS 1.2/1.3 (RSA, ECDHE, DHE).
Length: The maximum length of a single encrypted traffic packet supporting decryption is 64K.
Performance: 10Gbps (supports dynamic scaling).
Resource consumption
CVM Encrypted Traffic Detection
Resource occupancy: Under the traffic pressure of establishing 100 new HTTPS sessions per second, the resource utilization of the encrypted traffic detection Agent is as follows.
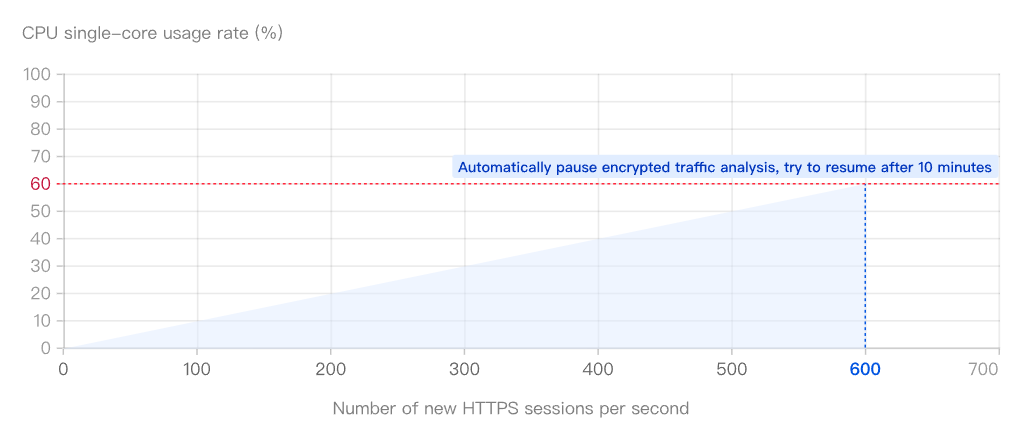
CPU occupancy: When continuously establishing new HTTPS sessions at a rate of 100 per second in the runtime environment, the single-core cpu utilization is approximately 10%. It supports up to 60% occupancy rate, corresponding to about 600 new HTTPS sessions per second.
Memory Usage: Initialization occupies 100MB, which improves as new HTTPS sessions are established, with a maximum occupancy of 500MB.
Auto pause when exceeding limit: When CPU or memory usage exceeds the limit, the Agent automatically pauses the "encrypted traffic analysis" feature (other basic features remain unaffected, and the Agent will not disrupt existing service connections or generate new encrypted traffic analysis results until resources are restored). It automatically retries analysis every 10 minutes. If the limit is still exceeded after restoration, the pause will continue until resource usage falls within the threshold.
Container Encrypted Traffic Detection
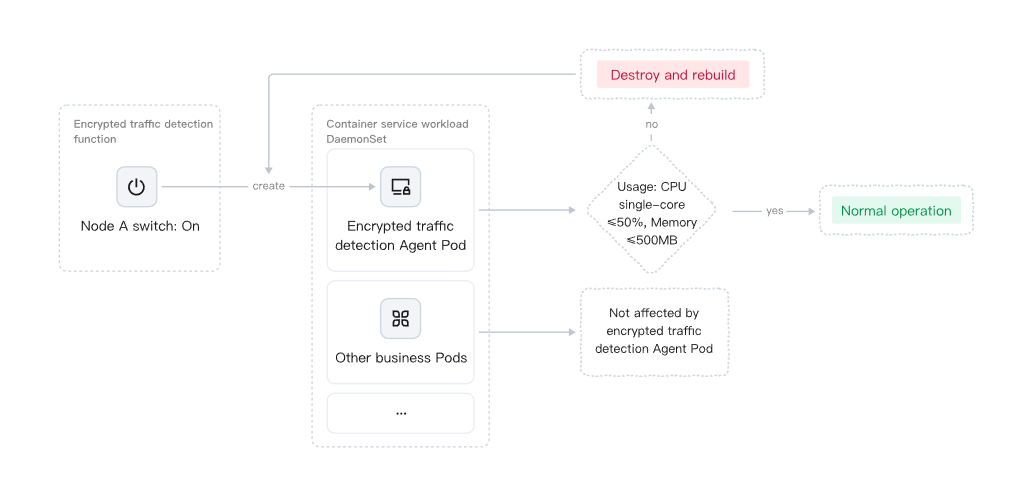
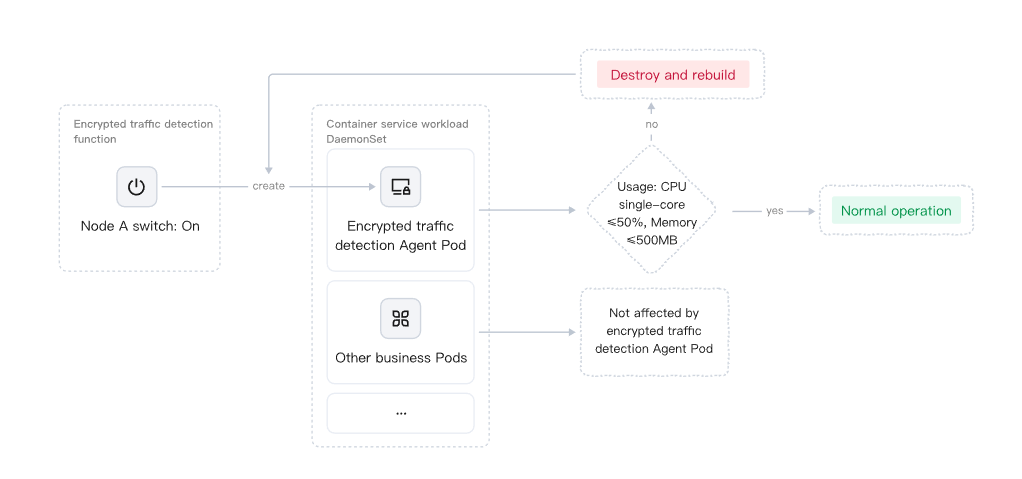
After enabling container decryption, the system will create an Agent Pod for encrypted traffic detection in the corresponding TKE workload > DaemonSet. The resource occupancy limits are as follows:
Overall restriction: Each Agent Pod can occupy a maximum of 50% of a single-core CPU and 500MB of memory.
CPU usage:
Each node with encrypted traffic detection enabled will independently create a corresponding Agent Pod. The functioning of this Pod will not affect the normal operation of other business Pods on the same node.
The TKE platform enforces mandatory limits on the CPU and memory usage of DaemonSet Pods. If a Pod's resource usage still exceeds the limit (e.g., due to anomalies breaking through 50% CPU or 500MB memory), the platform will automatically destroy the Pod and rebuild a new instance. This process will not affect other business Pods on the same node.
Enable Detection of Encrypted Traffic
You can navigate to Network Detection and Response > CVM, Container Cluster, or Public Network Traffic to enable/disable encrypted traffic detection for single or multiple assets.
Note:
Taking CVM assets as an example.
Single CVM Asset
In the CVM asset list, the system has added an "Encrypted Traffic Detection" operation column for CVM asset types. You can flexibly control the encrypted traffic detection status of individual assets using the "Detect" or "Do Not Detect" options in this column:
When you select Detect: The endpoint probe Agent is deployed with one-click rapid deployment, requiring no manual installation, and the system automatically completes the configuration. The encrypted traffic detection feature will be enabled for this CVM asset, and the page will display the real-time detection status, which falls into the following scenarios:
No prompt (normal state): When no abnormal alerts are displayed, it indicates that encrypted traffic detection is operating normally. The system has automatically deployed an endpoint probe Agent on your CVM node. This probe decrypts the HTTPS/TLS encrypted traffic of the asset and incorporates the decrypted plaintext traffic into the analysis scope of Network Detection and Response.
Red alert (abnormal state): If the detection feature becomes abnormal, the page will display a red alert icon and abnormal information, indicating that the current detection is unavailable. For details about the abnormal information and guidance, see Abnormal Information and Guidance.
Gray indicator (feature disabled state): When the main switch of Network Detection and Response is disabled, the encrypted traffic detection feature automatically stops, and the asset only detects plaintext traffic.
When you select Do Not Detect: The system will not enable detection of encrypted traffic for this CVM asset, performing only regular detection based on plaintext traffic.
Multiple Assets of CVM
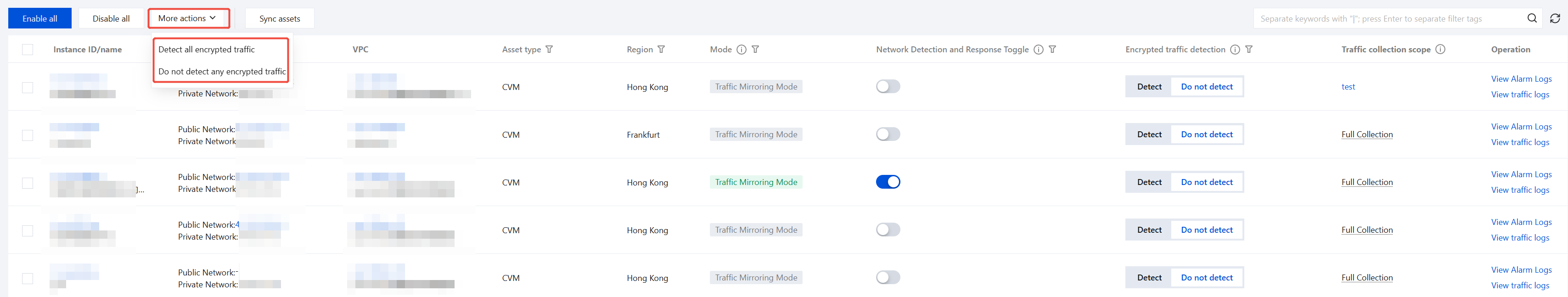
1. If you need to uniformly configure the status of encrypted traffic detection for all CVM assets, you can quickly do so via More Actions:
Detect all encrypted traffic: The system will automatically deploy endpoint probes on all CVM assets, decrypt their HTTPS/TLS encrypted traffic, and incorporate the decrypted traffic into the analysis scope of Network Detection and Response.
Do not detect any encrypted traffic: Endpoint probes on all CVM assets will stop decrypting encrypted traffic, performing only regular detection based on traffic transmitted in plaintext.
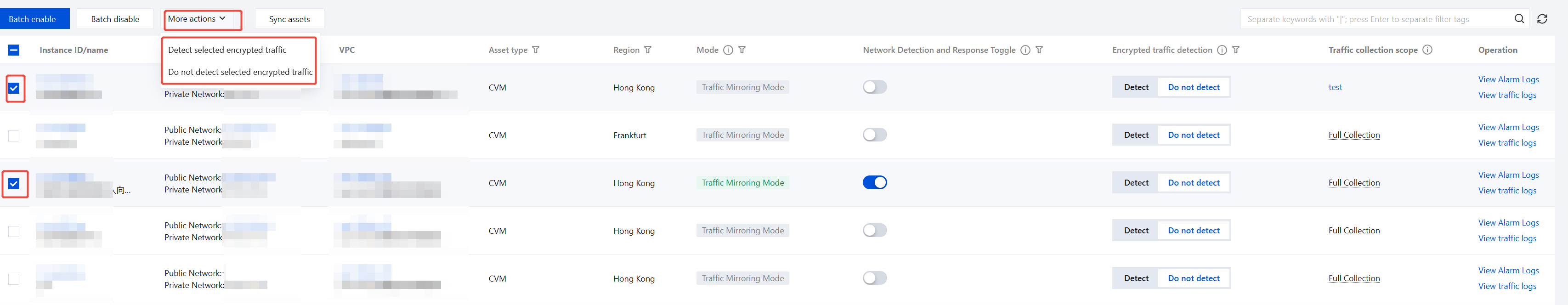
2. If you only need to uniformly configure the status of encrypted traffic detection for some CVM assets, you can do so by following the steps below:
2.1 In the CVM asset list, click More Actions.
2.2 Select the CVM assets that require configuration (multiple selection is supported).
2.3 Select batch operations:
Detect selected encrypted traffic: The system will automatically deploy endpoint probes on the selected CVM assets, decrypt their HTTPS/TLS encrypted traffic, and incorporate it into Network Detection and Responseanalysis.
Do not detect selected encrypted traffic: Endpoint probes on the selected CVM assets will stop decrypting encrypted traffic, detecting only plaintext traffic.
3. If you need to configure encrypted traffic detection for new assets, refer to Network Detection and Response switch.
Status Monitoring
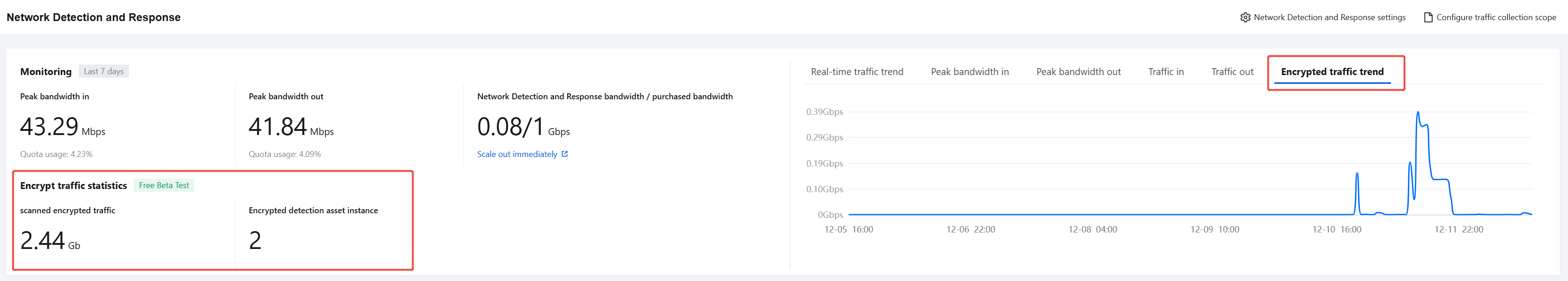
The system has added a dedicated statistics panel for encrypted traffic in the Monitoring module, helping you monitor the operating status and overall scale of encrypted traffic detection in real time. The core monitoring metrics include the following three items:
Statistics on cumulative parsed volume of encrypted traffic: Shows the total volume of encrypted traffic that has been parsed.
Count of Assets with Encrypted Traffic Detection: Displays the current number of CVM assets with encrypted traffic detection enabled.
Trend Chart of Cumulative Encrypted Traffic: Illustrates the dynamic changes in encrypted traffic parsing volume over the last seven days.
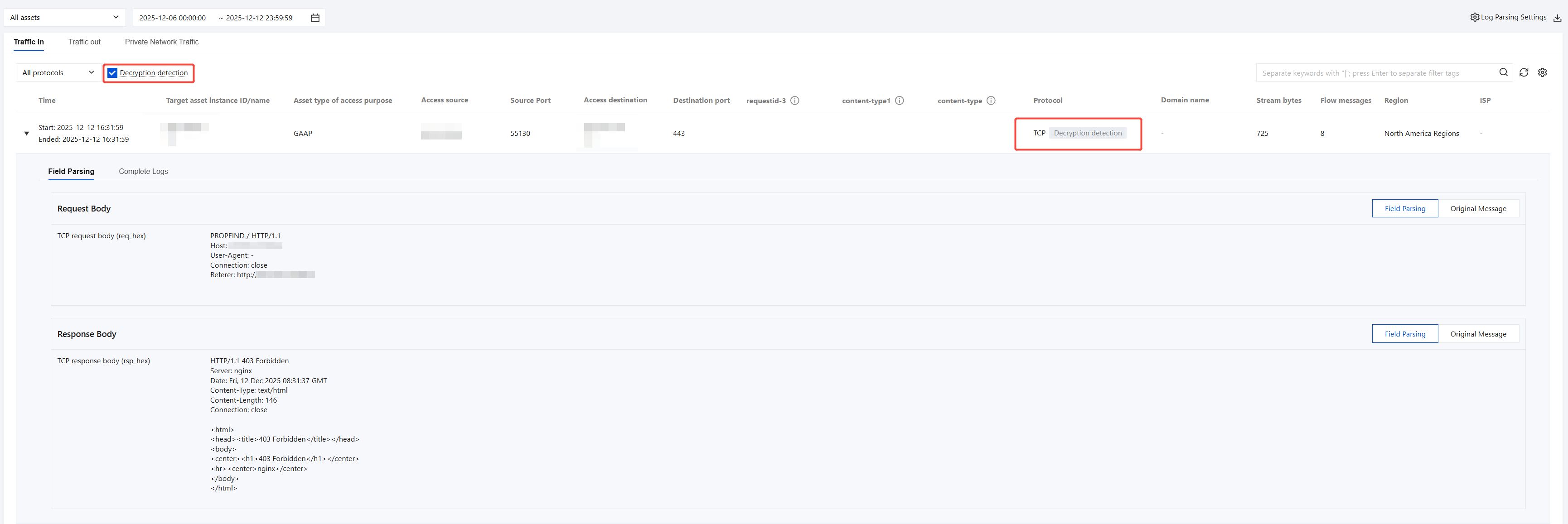
Encrypted Protocol Traffic Log
On the Log Auditing > Network Detection and Response Logs > Traffic Analysis Logs or Traffic Alarm Logs page, for traffic logs of encrypted protocols such as HTTPS, SMTPS, FTPS, the system will first restore the plaintext content (such as request headers, response bodies, and so on) and label it with Decryption Detection beside it; you can also select the Decryption Detection option to quickly filter and view all logs related to encrypted traffic detection.
Appendix
Exception Information and Guidance
Error Message | Solution |
The instance does not have the Terminal Automation Tool (TAT) installed. | The instance does not have Endpoint TAT installed. Please see TAT Deployment Guide and retry after completing the installation. |
The current operating system type is not supported. | The current operating system is not supported. Please visit the NDR-Technical Solution to confirm compatibility. |
The server is temporarily unavailable. Please try again later. | Temporary unavailability of the server has been detected. Please wait 5 minutes and try again. If the issue persists, please submit a ticket to contact technical support. |
Permission exception when container cluster access is obtained | Failed to obtain container cluster permissions, unable to handle Agent DaemonSet Pod exception. Please submit a ticket to request assistance. |
Terminal Agent abnormal | 1. The Agent network may be abnormal. Please check whether security groups allow access. 2. Operation of the Agent process may be abnormal. Please verify the operating system status. 3. If no abnormalities are detected, submit a ticket to contact technical support. |
フィードバック