使用 JWT 进行认证
Download
聚焦模式
字号
JWT 认证是基于 Token 的鉴权机制,不依赖服务端保留客户端的认证信息或者会话信息,客户端在密码字段或单独字段中提交 JWT,MQTT 将验证 JWT 的签名和声明信息,验证通过后服务端接受客户端连接请求。
什么是 JWT?
整体的认证原理如下图所示:应用程序从身份识别和访问管理服务(简称 IAM)获取 JWT,客户端在连接请求中携带 JWT,MQTT Broker 将使用预先配置的签名方式(下图的示例为公钥证书集的方式,也可以使用其他签名方式)对收到的 JWT 进行验证,如果内容一致,说明在传输过程中 Token 没有被篡改,认证成功;反之认证失败。
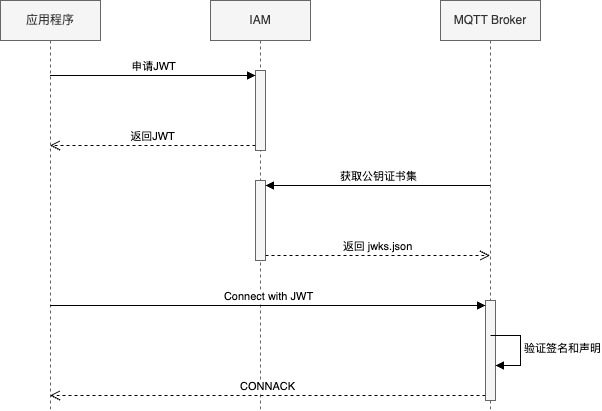
MQTT 基于 JWT 的认证原理
腾讯云消息队列 MQTT 版支持客户对接外部 JWT 服务进行认证和授权。
客户端使用用户名或密码字段携带 JWT,在发起连接时(发送 CONNECT Packet 时),MQTT 服务端会使用配置的密钥进行签名验证,判断 JWT 签名是否有效,以防被伪造或篡改。
当签名验证通过后,MQTT 服务端会进一步检查 Payload 中的声明信息(Claims),例如 iss(Issuer、签发者)、exp(Expiration Time、过期时间)、nbf(Not Before、生效时间)、iat(Issued At、签发时间)、aud(Audience、受众) 等, 判断 JWT 的合法性。
exp (过期时间):检查令牌是否已经过期。如果已过期则拒绝连接。
nbf (生效时间):检查令牌是否已经生效。比如令牌在5分钟后生效,那么5分钟前尝试连接会被拒绝。
iat (签发时间):判断令牌是否签发过早。
iss (签发者):检查令牌是否是由信任的签发者颁发的。
aud (受众):检查令牌是否是专门颁发给腾讯云 MQTT 服务的,防止一个发给其他服务的令牌被滥用到这里。
当 JWT 通过签名验证和 Claims 检查后, MQTT 服务端接受客户端连接请求。
前提条件
客户需要自行实现 JWT 服务用于给客户端分发 JWT Token,并且对应的签名算法要和下文在控制台配置的内容一致,您可以使用 JWT 官方提供的 JWT 调试器进行调试。您也可以使用自有的 JWKS(Json Web Key Set)服务器进行认证,请保证 JWKS 服务器可用并可以通过 TDMQ MQTT 的服务端访问到。
另外,为了保证认证的安全性,您还需要注意以下几点:
1. JWT 的 Payload 部分请勿携带敏感信息。
2. JWT 本身包含认证信息,一旦泄露,JWT 持有者将获得该令牌的所有权限。为了减少风险,JWT 有效期不宜过长。
3. 为了安全考量,JWT 应按业务场景分别授予。
4. 传输链路应该安全,应避免使用明文公网传输。
配置 JWT 认证
1. 登录 MQTT 控制台。
2. 在左侧导航栏单击资源管理 > 集群管理,选择好地域后,单击要配置证书的集群的“ID”,进入集群基本信息页面。
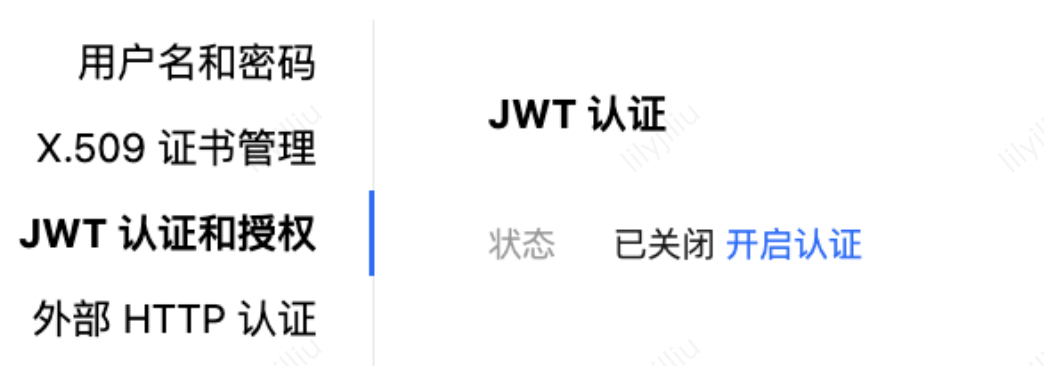
3. 单击认证管理,切换至 JWT 认证和授权。单击开启认证。
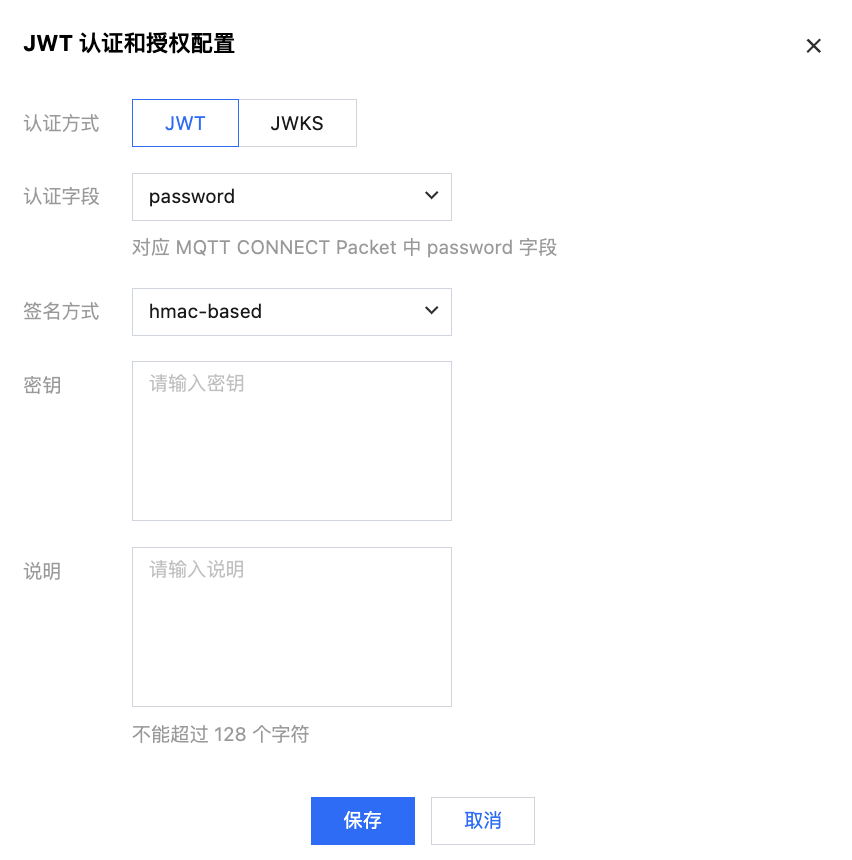
4. 在弹窗内完成 JWT 认证和授权的相关配置,认证方式支持 JWT 和 JWKS 两种。
根据下面说明完成配置:
认证字段:指定 MQTT 客户端在连接时使用 CONNECT Packet 的 Username 或者 Password 字段携带 JWT Token。
签名方式:JWT Token 的签名算法,当前支持 HMAC-based 和 公钥(public-key)两种方式的各类主要算法。使用公钥时请填写 .pem 文件格式的密钥。
密钥:根据不同签名方式的选择,填写对应的密钥,密钥内容由客户根据加密规范自行定义。
说明:非必填,按需填写,不能超过128个字符。
腾讯云消息队列 MQTT 版也支持客户使用 JWKS(Json Web Key Set)的形式来使用 JWT 进行认证,根据下面说明完成配置:
认证字段:指定 MQTT 客户端在连接时使用 CONNECT Packet 的 Username 或者 Password 字段携带 JWT Token。
认证信息来源:支持 JWKS 服务器和 JSON 认证两种方式。
服务器认证:JWKS 服务器指 MQTT 服务端动态从指定的地址获取公钥集合,因此您除了填写 JWKS 服务器地址之外,还需要填写定期从服务器获取公钥集合的时间。
当您的 IAM 提供的 JWKS 端点公网可以访问时,请选择服务器认证。
刷新时间:MQTT Broker 从 IAM 服务刷新公钥集的间隔。默认值为60s。
JSON 认证:JSON 认证方式指您维护固定的公钥集合,MQTT 服务端每次根据请求时的规则选用特定的公钥集里的公钥进行验签。认证器将使用从 JWKS 端点查询到的公钥列表 exp(Expiration Time),nbf(Not Before),iat(Issued At)。
当 IAM 提供方的 JWKS 端点服务网络与 MQTT Broker 网络不通时,选择 JSON 认证。请从 IAM 提供方下载 jwks.json 文件并将内容复制到文本框中。

5. 填写完成后,单击保存。
文档反馈