Custom Application Gateway Integration
If your business is deployed on third-party public clouds, private clouds, on-premises IDC data centers, etc., you can use the Hybrid Cloud WAF solution to access and manage your web applications both on and off the cloud through a unified Web Application Firewall (WAF). Hybrid Cloud WAF integration brings cloud-based protection capabilities to other cloud platforms or on-premises IDC regions, providing an integrated web application security management solution combining both local and cloud-based defenses.
Application Scenarios
Hybrid Cloud Business: Business deployed simultaneously on Tencent Cloud, other public clouds, private clouds, on-premises IDC, and VPC internal networks, requiring a unified web application protection solution.
Special Business: Specific business traffic that cannot be protected by public cloud WAF but needs to use Tencent Cloud’s WAF protection capabilities.
Functional Advantages
Supports unified security operation and management of cloud and on-premises assets and protection policies, reducing the complexity and workload of security operations.
Localized deployment solutions can provide proximity protection for customer business and support web protection in complex environments, reducing the risk of business transformation.
Real-time synchronization of cloud protection rules and threat intelligence capabilities, reducing operational costs.
Supports custom application gateway SDK integration, bypass detection, and manual bypass capabilities to enhance business operation stability.
Supports cluster object protection, where default protection policies at the cluster level are applied, reducing the risk of missed blocking and fully mitigating exposure to risks.
Activation Requirements
Activate the annual or monthly enterprise or flagship WAF instance and ensure at least 2 hybrid cloud nodes are available.
Ensure the required node deployment resources are prepared. For related resources, refer to the Hybrid Cloud Cluster Resource Preparation.
Hybrid Cloud WAF Cluster Management and Traffic Access Configuration
Step 1: Create Hybrid Cloud Cluster
1. Log in to the WAF console, and in the left navigation bar, select Service Settings > Hybrid Cloud Management.
2. On the Hybrid Cloud Cluster Management page, click Configure Now to automatically create a hybrid cloud cluster.
Step 2: Local Protection Node Deployment
Contact Tencent Cloud after-sales support experts to obtain the deployment scripts and images for the protection nodes, which support local deployment.
Automated installation is suitable for environments with more flexible development requirements, mainly including: importing database data, installing Helm applications, and requiring kubectl access privileges. After modifying the files, run
./install.sh.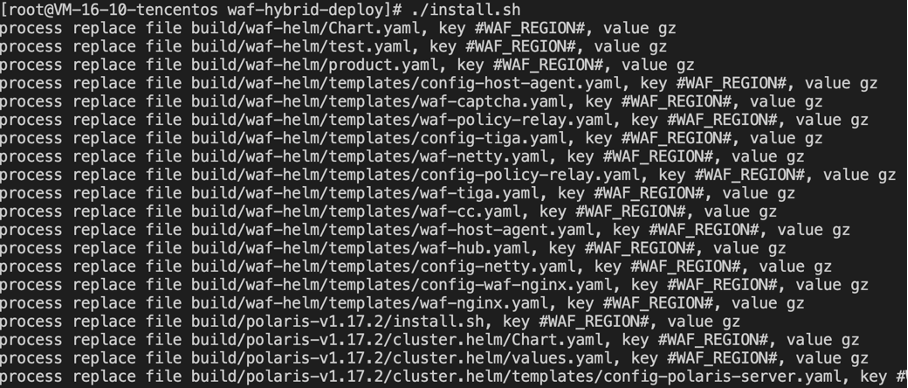
Step 3: Access Domain and Cluster Objects
1. Log in to the WAF console and select Connection Mangement > Domain Onboarding on the left sidebar.
2. On the domain onboarding page, click Add domain, configure relevant parameters, and click OK.
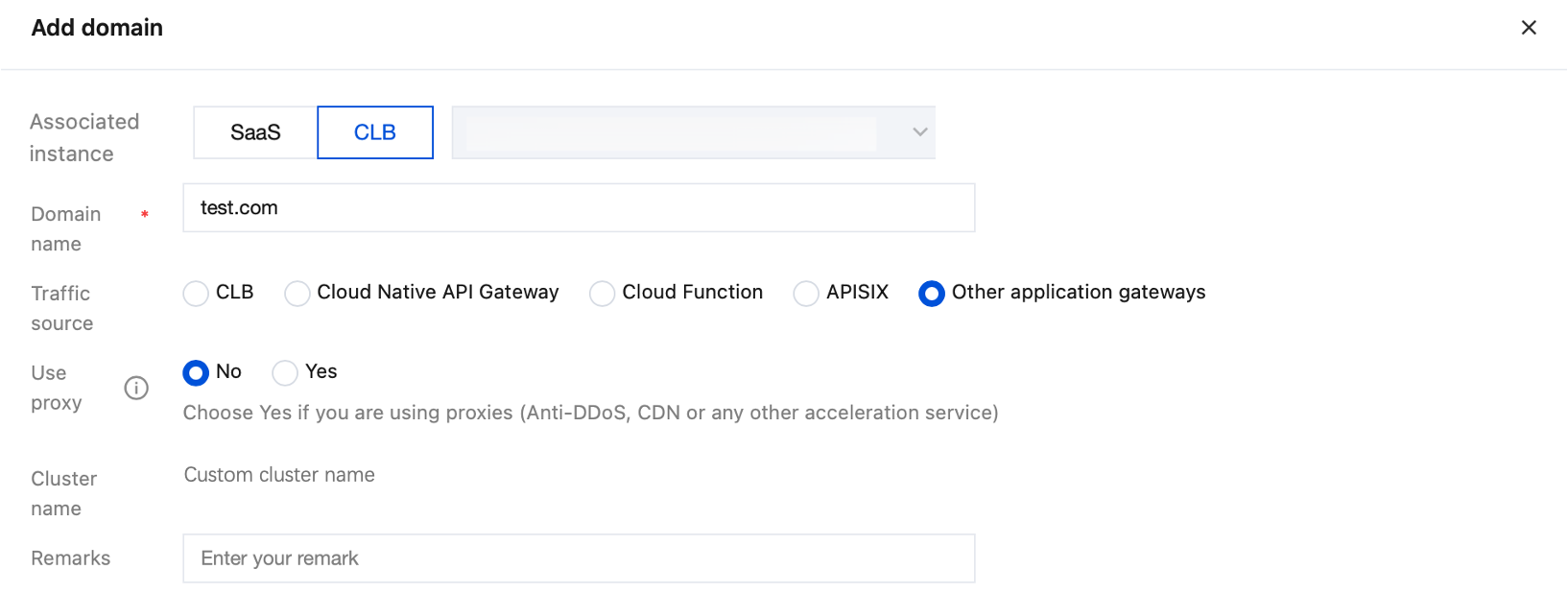
Field description
Associated instance: Select the CLB type and cluster object name.
Domain name: Enter the domain name to be protected, such as
test.com.Traffic source: Select Other application gateways.
Use proxy: Select whether proxy services including Anti-DDoS and CDN are used based on the actual conditions.
Note:
If you select Yes, WAF will get real client IPs, which may be forged, from the XFF field as the source IPs.
Cluster name: Custom cluster name.
Remarks: Enter your remark.
3. After clicking OK, return to the domain access page where you can view the protected domain, gateway instance ID, and name, along with other information.
Step 4: Install SDK for Traffic Forwarding
SDK integration requires deploying the SDK plugin on the unified access gateway. The SDK plugin duplicates the gateway's business traffic and forwards it to the WAF protection cluster. In this mode, the hybrid cloud WAF protection cluster does not participate in traffic forwarding, achieving separation of business forwarding and detection.
Step 5: Verification Test
In the browser, enter the URL
http://<Gateway Domain or IP>/?test=alert(123)and access it. If the browser returns a blocked page, it indicates that the Web Application Firewall protection function is working properly.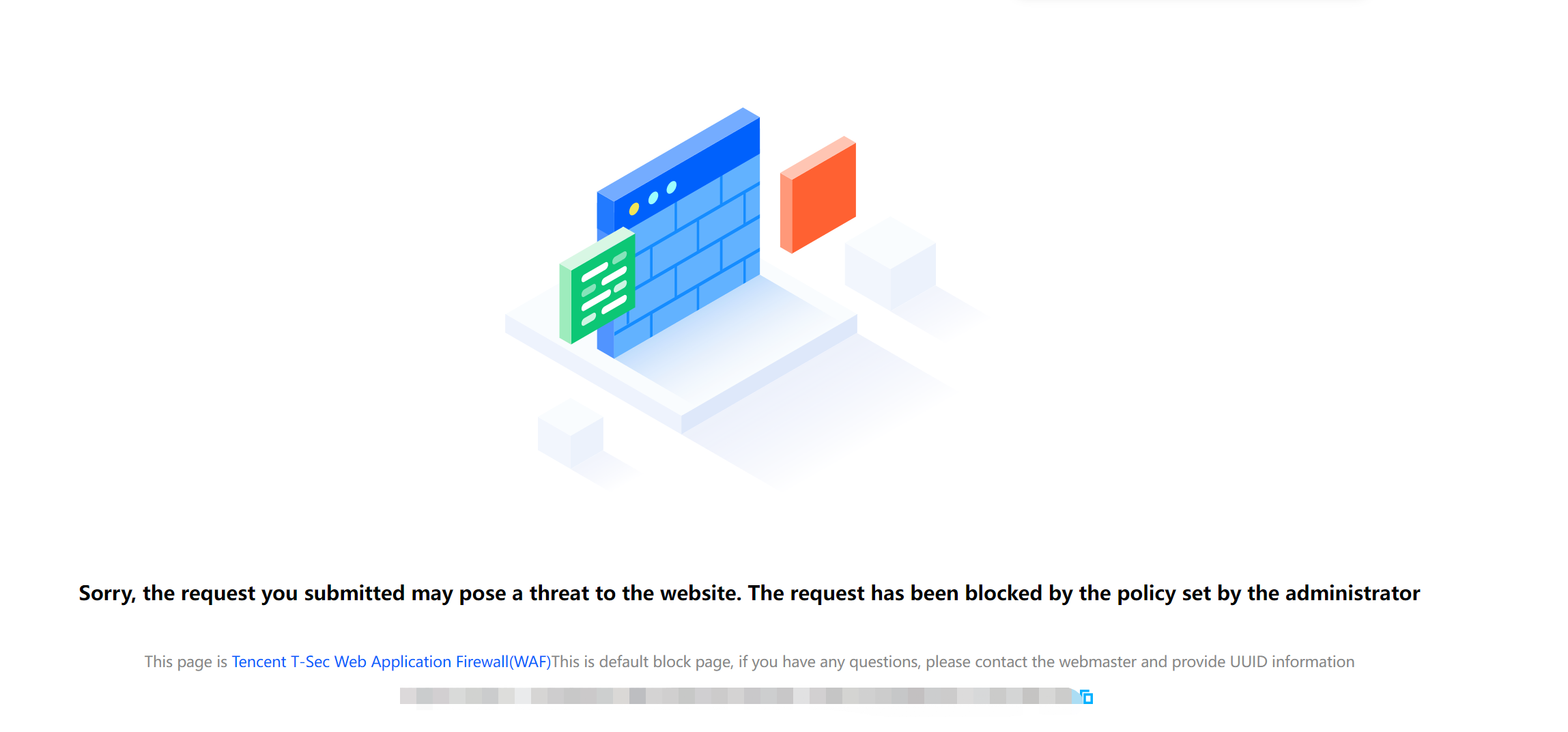
Help and Support
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback