Release Notes
Announcements
Release Notes
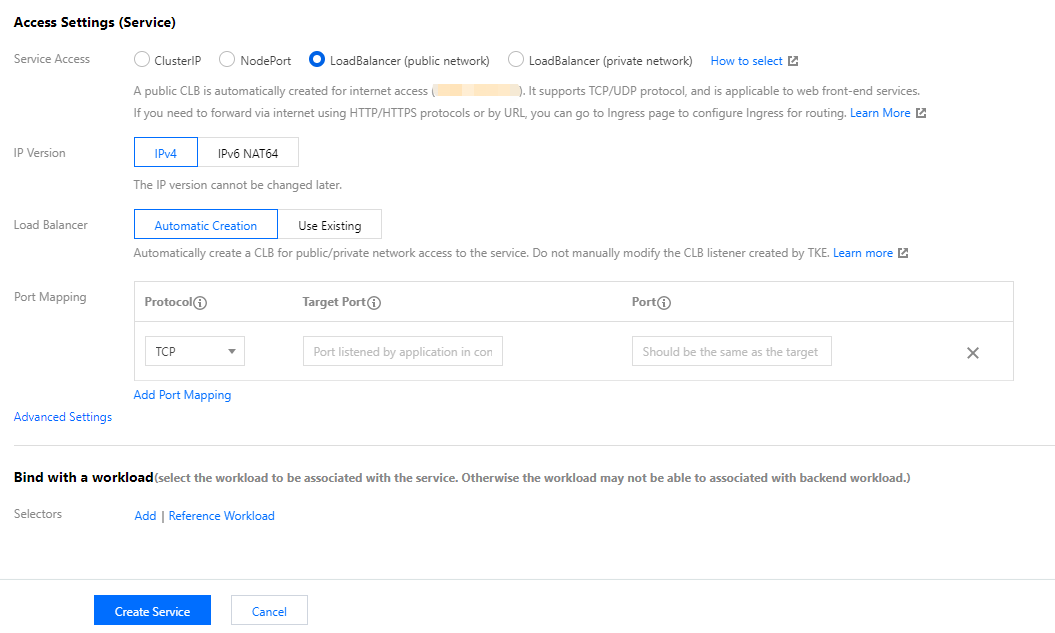
ClusterIP and NodePort modes can be used together. However, the community has restrictions on Services of the LoadBalancer type, and only protocols of the same type can be used currently.LoadBalancer is declared as TCP, the port can use the capabilities of extension protocols to change the protocol of CLB to TCP_SSL, HTTP, or HTTPS.LoadBalancer is declared as UDP, the port can use the capabilities of extension protocols to change the protocol of CLB to UDP.LoadBalancer mode.LoadBalancer mode.Service Spec is not covered in the annotation of the extension protocol, Service Spec will be configured according to your declaration.Service Spec, the configuration will be ignored.Service Spec, the protocol configuration declared in Service Spec will be overwritten.{"80":{"protocol":["TCP_SSL"],"tls":"cert-secret"}}
{"80":{"protocol":["HTTP"],"hosts":{"a.tencent.com":{},"b.tencent.com":{}}}}
{"80":{"protocol":["HTTPS"],"hosts":{"a.tencent.com":{"tls":"cert-secret-a"},"b.tencent.com":{"tls":"cert-secret-b"}}}}
{"80":{"protocol":["TCP","UDP"]}} # Only supported in direct access mode. For more information, visit https://www.tencentcloud.com/document/product/457/36837.
{"80":{"protocol":["TCP_SSL","UDP"],"tls":"cert-secret"}} # Only supported in direct access mode. For more information, visit https://www.tencentcloud.com/document/product/457/36837.
{"80":{"protocol":["QUIC"],"tls":"cert-secret"}}
cert-secret in TCP_SSL and HTTPS indicates that a certificate must be specified when you use the protocol. The certificate is an Opaque type Secret, the key of Secret is qcloud_cert_id, and the value is the certificate ID. For details, see Ingress Certificate Configuration.apiVersion: v1kind: Servicemetadata:annotations:service.cloud.tencent.com/specify-protocol: '{"80":{"protocol":["TCP_SSL"],"tls":"cert-secret"}}' # To use other protocols, change the value in the key-value pair to the above contentname: test....
apiVersion: v1kind: Servicemetadata:annotations:service.cloud.tencent.com/direct-access: "true" # TKE Serverless clusters default to use the CLB-to-Pod direct access mode. For TKE clusters, you must enable the CLB-to-Pod direct access mode with reference to the document.service.cloud.tencent.com/specify-protocol: '{"80":{"protocol":["TCP"]},"8080":{"protocol":["UDP"]}}' # It specifies that port 80 uses the TCP protocol, and port 8080 uses the UDP protocol.name: nginxspec:externalTrafficPolicy: Clusterports:- name: tcp-80-80nodePort: 32150port: 80protocol: TCPtargetPort: 80- name: udp-8080-8080nodePort: 31082port: 8080protocol: TCP # Note: Only the same type of protocols can be used because of the limits of Kubernetes Service Controller.targetPort: 8080selector:k8s-app: nginxqcloud-app: nginxsessionAffinity: Nonetype: LoadBalancer
Apakah halaman ini membantu?
Anda juga dapat Menghubungi Penjualan atau Mengirimkan Tiket untuk meminta bantuan.
masukan